Achieving Compliance with IGA and SMP Tools
May 4, 2021
6 minute read
Compliance requires a successful audit that proves an enterprise complies with its security policy. In this mission, many enterprises use two important technologies: identity governance and administration (IGA) and SaaS management platforms (SMPs). So here, we discuss achieving compliance with IGA and SMP tools and how they help with compliance and audits.
But, first let’s make sure that we’re all on the same page.
What are audits, IGAs, and SMPs?
Let’s begin with explaining what happens in an audit, which itself starts with your security policy. Among other things, that security policy needs to cover identity management, approval processes, and data protection.
Audits are a part of compliance, regardless of the exact laws or standards an enterprise follows.
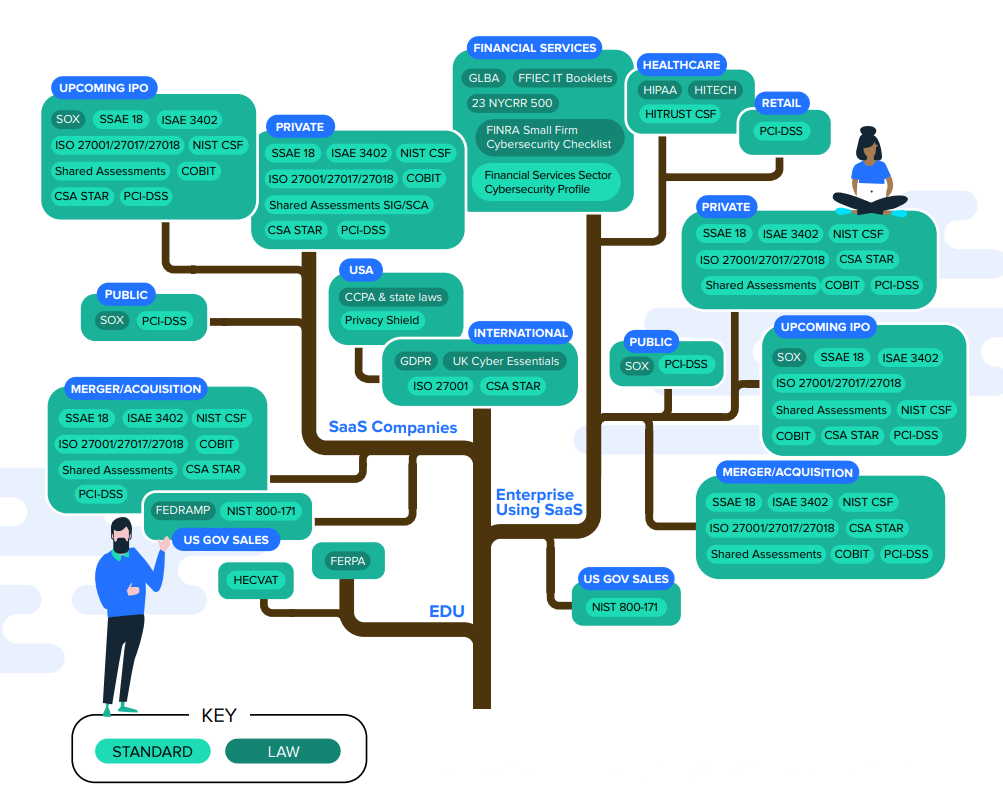
This compliance tree can help you navigate which laws, regulations, and standards might be applicable to you.
A compliance audit means the auditor follows three fundamental steps to understand:
- What do you say you do for effective security and privacy compliance (e.g., the documented data privacy and security policies and processes)?
- Does what you say satisfy requirements of relevant laws, regulations, or standards?
- Do you do what you say?
Audit trails show whether an enterprise satisfies requirements of laws, regulations, or standards.
IGA and SMP functions are key to the audit trail
IGA, sometimes called identity management and governance, or IGM, is an automation platform for provisioning, deprovisioning, and managing user accounts, roles, and access rights. They work across both cloud and on-prem infrastructure and provide visibility into managing passwords, access certifications, and access approvals for both on-prem and SaaS apps.
They facilitate compliance because they provide:
- Identity-related risk insight
- Improved security
- Ability to meet audit requirements
Mostly used by large organizations or highly regulated ones, IGAs are an established technology that is deployed on-prem or as a service in the cloud.
Meanwhile, an SMP is a comparatively new IT automation platform that enterprises are now quickly adopting.
In enterprise IT, an SMP provides a central place to automatically discover SaaS apps in use throughout the organization, as well as manage and secure users, apps, data, files, folders, and user interactions within SaaS apps.
SMPs are used for many reasons, and among them are:
-
- Spend reporting
- Spend optimization
- Least privilege access enforcement
- SaaS app management
- File security and compliance
- File sharing and data exposure alerts
- User lifecycle management (on/offboarding and mid-lifecycle changes)
As such, to accomplish these tasks, SMPs are the ultimate technology team player.
To operate, they must integrate with several other systems. These could be: a cloud access security broker (CASB), IT service management tool (ITSM), or a human resources information system (HRIS). They’ll also integrate with identity providers like OneLogin as well as endpoint management tools like Jamf. From there, they obviously integrate with a range of cloud productivity apps, like Google Workspace and Microsoft 365, as well as point apps like Asana, Jira, and countless others.
Achieving compliance with IGA and SMP tools
Now you know that each tool performs different functions for enterprise IT, let’s take some time to detail how IT teams achieve compliance with IGA and SMP tools.
Improving compliance with IGAs
App approvals are obviously part of user onboarding—and to a lesser degree, mid-lifecycle changes. And compliance generally requires that organizations verify and closely track requests for app approvals.
From start to finish, IGAs automate the entire app approval process. This includes:
- Submission of app requests
- Logging of all app requests
- Logging of the entire process to the ultimate app approval
- Audit reports showing compliance with documented process for auditors
An IGA then usually integrates with another identity management tool, the identity as a service (IDaaS) platform. Once a user’s app access is approved, the IDaaS then creates the user, associates necessary SaaS app licenses, and adds the user to the appropriate groups.
While it is possible to use an IGA to automate an entire onboarding process, its out-of-box catalog contains fewer actions IT teams can use to build workflows. To automate more of the process, significant custom programming is generally necessary.
This, of course, hampers the flexibility and agility that IT teams need to manage user lifecycle automations. Quite simply, changing custom programs is difficult, whereas no-code SMP platforms are purpose-built for ULM automation flexibility. An SMP like BetterCloud can also work together with an IGA to handle much of what an IDaaS is typically used for, including account creation and adding users to groups. This functionality is especially critical for organizations looking to transition to a zero touch IT model.
For these reasons, most organizations tend to use an IGA for its strength—the app approval process—and leave the rest to other tools.
Using an SMP to improve compliance
An SMP has some important functions that help compliance. Specifically, it helps with:
- Automating user lifecycle management according to security policy
- Managing files in your SaaS environment to enforce data sharing policies
- Content scanning to prevent data loss
- Proving actions occurred according to built-in audit logs
Let’s go through how each one helps.
Manage the user lifecycle to remain secure and compliant
While IGAs have a greater role in offboarding than offboarding, an SMP plays a role to automate user onboarding, mid-lifecycle changes, and offboarding.
Because each SaaS app has its own way of doing things, SMPs perform a deeper and broader range of app configuration actions within each SaaS app for onboarding.
So while an SMP onboards in a handful of workflows, complete and secure offboarding can take dozens, and in some cases, hundreds of different workflows—each with its own actions.
This includes actions like transferring files—wherever they may be within a SaaS app throughout your SaaS environment—to a manager. It also includes actions like revoking app licenses, starting the compliance-related waiting period for file deletion, and then returning licenses to inventories.
Prove compliance with embedded file security best practices
An SMP allows you to manage, secure, and view all the files and folder contents across your domain’s connected apps, audit details about particular items, filter and search files, and take actions against items you select. An IGA has nothing to do with these actions, so this sort of compliance with an IGA is not possible.
An SMP aids manageability and security by monitoring for:
- Sensitive files being publicly or externally shared
- Sensitive folder paths, like accounting or finance, being publicly or externally shared
- Email forwarding to a personal email account (e.g., Gmail, Yahoo)
- Specific file types being publicly or externally shared (e.g., spreadsheets and PDFs are more likely to contain sensitive information)
- Users who should no longer have access to specific files, folders, calendars, etc. (e.g., consultants, interns, employees who’ve switched teams)
- Users who should no longer belong to specific groups/distribution lists (e.g., contractors, employees who’ve switched teams)
- External domains to which files are shared
- External people with whom files are shared
Boost security and compliance with SMP’s content scanning
Content scanning in an SMP allows enterprises to secure the data within SaaS apps, as well as pinpoint suspicious activity without impeding employees’ productivity.
IT defines what an enterprise considers as sensitive data within apps. And because it’s data within SaaS apps, the SMP enforces granular policies to include users, apps, files and folders and the range of how sharing occurs. For example, should data be shared externally, publicly, domain-wide, internally, or within departments or groups?
SMPs also allows enterprise IT to run audits to scan content contained in the entire environment or select files to find the most common sensitive content, such as Social Security, credit card, or passport numbers. They even let enterprises set up alerts to notify the appropriate teams when files with sensitive data are overshared.
IT also defines actions the SMP should take in the event of a violation. It dictates the most appropriate action from a greater range of actions that consider context.
The best SMPs also makes the process easy. By selecting from pre-set data identifiers for common sensitive data types across different countries, good SMPs allow enterprises to create custom regular expressions.
Make audits easier and more affordable using SMP audit logs
Many laws, regulations, and standards require that organizations prove that they comply with them. In particular, they generally require timeline tracking to log system changes. Of course, this includes when changes were made and who made them.
So audit logs and reporting within SaaS apps are a necessity. Compliance with IGA logs only are simply not enough.
Rather, SMP audit logs show a complete picture of everything that happens within a domain within all SaaS apps.
An SMP, thus, gives complete visibility into:
- Exact action or event
- Date and time action or event happened
- User or entity that took an action
- Integrations and third-party app data
- Status of the action or event
While audit logs help IT teams discover, manage, and secure the SaaS environment, they also verify adherence with compliance policies. As a byproduct of normal operations, an SMP simplifies compliance.
Build confidence in your compliance with IGA and SMP tools
In sum, these two tools are both essential in the large, modern digital enterprise. However, each tool plays a very different role.
Compliance with IGAs is more about automating identity management and tracking the app access approval process. Since SMPs discover, manage, and secure SaaS within each app across the SaaS environment, this platform is valuable for compliance across a broader set of actions occurring in the whole domain. In addition, SMPs show activity within SaaS apps.
Using both an IGA and SMP together is the best way for large enterprises to confidently achieve security and compliance.
For more information on compliance in a SaaS-powered workplace, check out our 4-part blog series:
- Content Scanning for Sensitive Data: Part 1 of Compliance Essentials in the SaaS Era
- Audit Logs & Sarbanes-Oxley Compliance for SaaS: Part 2 of Compliance Essentials in the SaaS Era
- Enforcing Access Privileges for SaaS: Part 3 of Compliance Essentials in the SaaS Era
- Managing Files in SaaS: Part 4 of Compliance Essentials in the SaaS Era



