Where does BetterCloud fit into your tech stack?
January 21, 2026
13 minute read
TL;DR: The SaaS Operations Management Framework
As we move deeper into the AI era, the question isn’t if you have a tech stack, but how much of it is running on autopilot. As organizations adopt more and more SaaS and approach SaaS maturity, the role of a SaaS operations management tool has shifted from a “nice-to-have” utility to a necessity. It’s now the central automation and orchestration engine of IT.
- The Hub of the Software Stack: BetterCloud doesn’t replace your existing tools; instead, it acts as a “Manager of Managers.” It sits between your Identity (IDaaS), Service (ITSM), and Security (CASB/SSPM) layers to automate the granular actions those tools can’t reach.
- The “Last Mile” of Identity: While an IDaaS like Okta or Microsoft Entra ID gets a user through the front door, BetterCloud manages the interior—automatically configuring and managing specific in-app settings, Slack channels, multi-SaaS automations, and file permissions.
- Zero-Touch Operations: By integrating a SaaS management platform into your tech stack, you evolve from manual ticketing and multiple software consoles to managing autonomous fulfillment. When a ticket is approved in your ITSM, BetterCloud executes the task and closes the loop without human intervention. Fast and secure. Every time.
- Continuous Governance: Beyond onboarding and offboarding, BetterCloud provides a 360-degree view of your software stack, identifying Shadow IT—and its close cousin Shadow AI—reclaiming underutilized licenses for spend optimization, and remediating file security risks in real-time.
The Bottom Line: BetterCloud is the connective orchestration layer that transforms a disconnected collection of apps into a unified, secure, and cost-efficient ecosystem of SaaS apps.
In the early days of SaaS, a tech stack was relatively simple: perhaps a dozen core applications. Today, the average enterprise manages over 100 SaaS applications. This SaaS sprawl hasn’t just increased the number of browser tabs open; it has fundamentally changed the nature of IT work, as IT has adopted many SaaS tools themselves. You all use SaaS-based security, identity, and service management, and probably wonder where BetterCloud fits into your tech stack.
As you know, modern IT teams no longer just fix computers. They are the architects of a complex system of SaaS apps. To manage this tech stack, they require a specialized SaaS operations management tool that can sit above the fray and coordinate action. But how exactly does a SaaS management platform fit into your software stack, and how does it interact with the other tools your IT team uses?
Stay with us as we will break down the modern software stack for IT and show how BetterCloud acts as the critical connective and automation layer between identity, security, and service management.
The evolution of the modern software stack
Before we look at the “where,” we have to understand the “what” that goes into the tech stack used to manage IT and SaaS.
Most IT professionals probably recognize those tools by the acronyms that define them: IDaaS (identity as a service) or IdP (Identity Provider), IGA (identity governance and administration), CASB (cloud access security broker), SSPM (SaaS security posture management), ITSM (IT Service Management). You know, just to name a few.
Right now, a robust enterprise tech stack is generally divided into four functions:
- Identity and access: Tools like Okta, Microsoft Entra ID, and Google Workspace.
- Service and support: IT service management tools like ServiceNow, Zendesk, and Jira Service Management.
- Security and compliance: CASBs, SSPMs, Endpoint Management (MDM), and SIEMs like Splunk.
- SaaS management and orchestration: This is where BetterCloud operates.
Without that fourth function—the all-in-one SaaS operations management tool—the other three tend to operate in silos. IT is left manually bridging the gap: Exporting a list of users from the Identity tool, cross-referencing it with the ITSM tool, and manually clicking buttons in each app security revoke access and transfer files.
BetterCloud changes this by providing a unified orchestration layer that allows all functions to communicate and act as one.
Can BetterCloud serve as our entire tech stack for IT?
A common question we hear is: “If BetterCloud can do so much, do I still need my other tools?”
The answer depends on a few things.
First, there’s the maturity and scale of your organization. For a small-to-medium business (SMB) that is 100% SaaS, like educational institutions that primarily use just Google Workspace, BetterCloud often serves as the primary “command center.” In fact, we have many digital-first customers that solely rely on us to operate IT.
Second, what if you don’t have complex on-premise infrastructure or a legacy Human Resources Information System (HRIS) and you’ve got dozens and dozens of SaaS applications? A SaaS management platform fits into your tech stack as the primary driver of user lifecycle management.
For example, let’s say all your applications are SaaS. If you use an all-in-one SaaS management platform, its rich functionality enables IT to manage many aspects of SaaS operations.
Over recent years, the best SMPs have evolved from managing users in a single cloud productivity suite into powerful platforms capable of much more. Now from a unified platform, you can optimize SaaS usage, spending, and budgets. This crucial tool also helps you automate repetitive tasks, enable secure user lifecycle management, maintain SaaS file security and governance, prove compliance, as well as many other tasks.
But as companies grow in headcount and complexity, their IT tech stacks tend to include an SMP like BetterCloud alongside other tools. While BetterCloud handles some of the finer details like file access policy, permissions, and admin settings, you don’t necessarily say farewell to your CASB or IDaaS.
In these cases, for the enterprise, BetterCloud is a force multiplier. It doesn’t replace your identity provider, it makes it more powerful. It doesn’t replace your ticketing system, it makes your ticketing system autonomous. In these environments, BetterCloud is the tool that executes the more granular actions that broad infrastructure tools simply weren’t built to handle.
A quick note before we move on. Our friends in solutions engineering urged me to let you know that these following examples are specific to user lifecycle management for automated onboarding and offboarding. They’re also not a one-size-fits-all solution for all IT organizations.)
Where BetterCloud fits in your tech stack
So how does BetterCloud play nicely with an IDaaS, IGA, ITSM, or a CASB?
While each organization’s tech stack is unique in its own way, we can quickly identify a few trends. At a glance, here’s what we’ll unpack in this very long section:
- Customers use an IDaaS to handle the initial user provisioning tasks of an onboarding process.
- Companies use an IGA to manage approval processes for compliance
- IT relies on ITSMs for managing IT services and help desk across all IT infrastructure, not just SaaS
- After a user gains basic access to SaaS applications, BetterCloud handles the finer details, like managing SaaS licenses and budgets, maintaining SaaS file governance, determining which types of files should be shared in Slack and creating custom admin roles in Google Workspace.
OK, enough context. Let’s explore some specific examples of how BetterCloud fits into your tech stack.
Architecture with an IDaaS
The relationship between IDaaS, like Okta or Microsoft Entra ID, and BetterCloud is often the most misunderstood part of the tech stack.
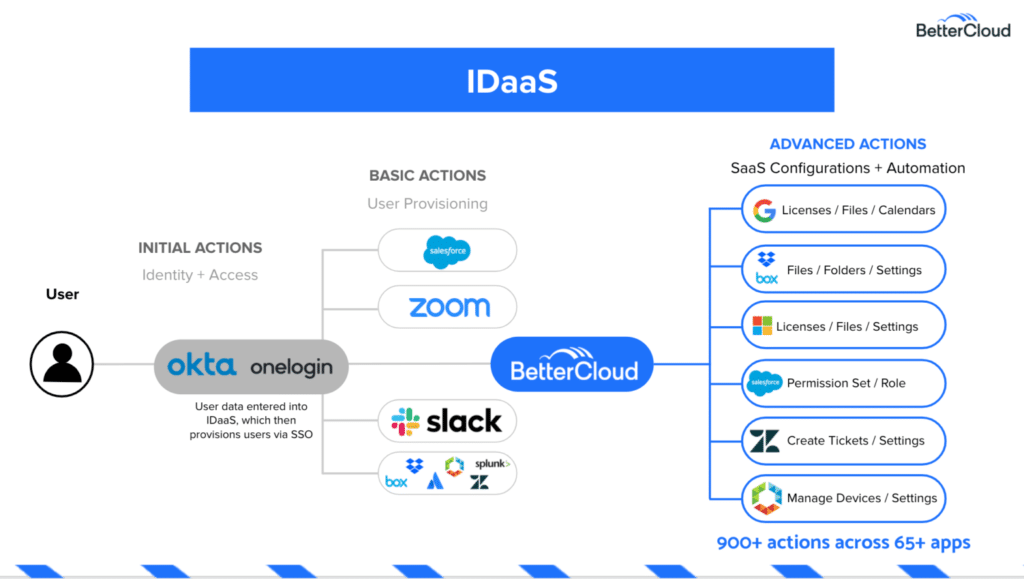
The “coarse-grained” vs. “fine-grained” distinction
Most IDaaS tools are excellent at “coarse-grained” access. They can create an account in Salesforce and give a user a login. But that is where their visibility ends. They cannot tell you if that user is sharing a sensitive “Project X” folder with a personal Gmail account. They cannot tell you if a user hasn’t logged into a specific Slack channel in six months.
Complete automated processes
When a SaaS management platform fits into your tech stack alongside an IDaaS, you create a complete user lifecycle:
Step 1 (IDaaS): A new hire is added to the HRIS. The IDaaS triggers the creation of a Google Workspace account.
Step 2 (BetterCloud): BetterCloud detects the new user and begins the “fine-grained” work. It adds the user to 15 specific Slack channels based on their sub-department, sets their email signature, shares the “All Hands” calendar, and grants specific “Editor” permissions to three folders in Dropbox.
Step 3 (Continuous Governance): Throughout the employee’s tenure, BetterCloud monitors their interactions. If they try to change a security setting in an app that violates company policy, BetterCloud reverts it instantly—something an IDaaS isn’t designed to do.
Let’s say one user in your org has transitioned to another department. When you update that person’s profile in OneLogin or Okta, this will trigger BetterCloud to complete any number of tasks that IT would otherwise take manual effort. This includes tasks like reassigning that person to different groups in Google Workspace or changing permissions in Salesforce.
Finally, for offboarding, when you change a user’s status to “suspended” on either platform, BetterCloud can automatically begin the offboarding process.
But wait, doesn’t your identity provider handle user deprovisioning? It does, but BetterCloud handles the finer details (and enables you to easily automate them using no-code workflows), such as transferring files to a manager, wiping devices remotely, ordering a box to be shipped, and waiting a set period of time before deleting the user.

Ultimately, BetterCloud is a complementary tool to an IDaaS, which is a complementary tool to an Identity Governance and Administration (IGA) solution.
Architecture with an IGA
Identity governance and administration is a policy-based approach to identity management and access control. That makes sense, right? But it doesn’t explain how an IGA works with an IDaaS—and more importantly, how BetterCloud fits in the tech stack.
Here’s another visual to help make sense of the confusion:
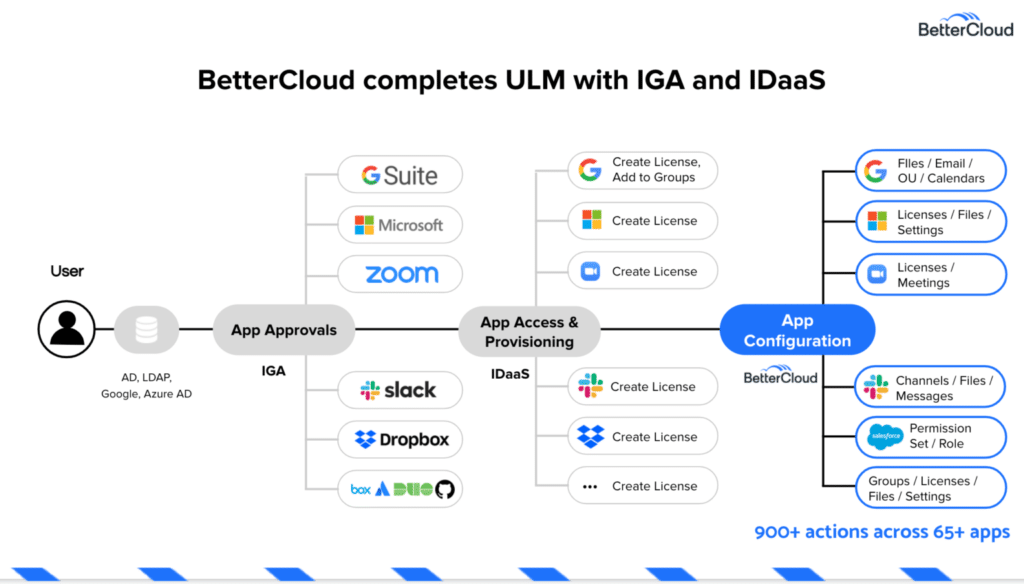
Identity Governance (IGA) tools like SailPoint are designed for the heavy lift of compliance. They are used to prove to auditors that the right people have the right access to approved apps and followed the proper subscription approval process. However, these tools often struggle with the “last mile” of SaaS.
IGA tools are great at the “Why” and “Who” in accordance to your security policy, but BetterCloud is great at the “How” for execution.
When you combine IGA with an SMP, you create a robust compliance framework:
- Policy (IGA): Defines that only Marketing Directors should have access to the corporate LinkedIn page.
- Audit (IGA): Runs a report to show who has access.
- Remediation (BetterCloud): If the IGA report finds a former employee still has access, BetterCloud is the tool that actually goes into the application and removes the user.
In an onboarding scenario, once the IGA gives a user the green light, the IDaaS creates the licenses that the person needs. Then, BetterCloud handles the granular actions like settings and permissions for sharing files and folders, applying the appropriate settings to an account, and putting a user in the correct groups and channels.
This synergy ensures that your enterprise tech stack isn’t just compliant on paper, but secure in practice, with the never-expiring audit logs to prove it.
Architecture with an ITSM
The ITSM is the “source of truth” for IT’s work. Whether it’s ServiceNow, Zendesk, or Freshservice, this is where the paper trail lives. However, without a SaaS operations management tool, the ITSM is just a digital pile of requests for IT.
BetterCloud’s integration with leading ITSMs allow IT to build workflows that automate a significant number of IT tasks. Using the ITSM platform’s robust Webhook functionality, it enables BetterCloud to kick off user lifecycle management workflows based on events that occur within the ITSM.
From manual tickets to zero-touch fulfillment
Historically, an employee would submit a ticket for a Zoom Pro license. An IT manager would see the ticket, log into the Zoom admin console, check for available licenses, assign the license, and then go back to the ticket to close it.
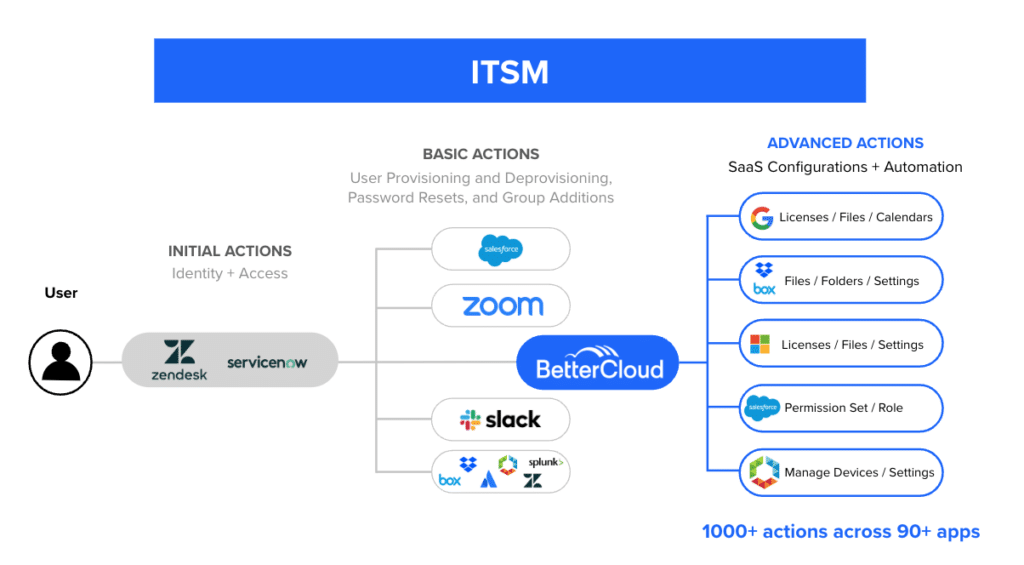
In a modern tech stack like one shown in the above diagram, thanks to your SaaS operations management tool that automates time-consuming help desk ticket resolution, this process is invisible:
- Request: The employee requests a license via a Slack bot or the ServiceNow portal.
- Logic: BetterCloud checks the company’s license inventory. If a license is available, it checks the user’s role to see if they are authorized for a Pro account.
- Action: BetterCloud assigns the license in Zoom.
- Resolution: BetterCloud sends a Webhook back to the ITSM to close the ticket and sends a Slack message to the user: “You’re all set! Your Zoom Pro account is active.”
Using these two tools, IT can completely automate routing for app access approval, app configuration, and closing support tickets. And automated processes that it’s capable of executing don’t end there.
It can automate other manual and redundant ticket requests like password resets, email delegations, group additions, just to name a few.
Now by using the BetterCloud Self-service Agent, a Slack-based IT assistant that seamlessly integrates with your ITSM, IT can extend instant, self-service support to employees. No more ticket queues and no more employees unproductively waiting for resolution.

This zero-touch automation approach is now the ultimate goal for every IT department. It removes IT bottlenecks, keeps users happy, increases organizational productivity, and allows the team to focus on high-level strategy rather than clicking buttons in admin consoles.
Architecture with IPaaS
If you’re still operating a legacy HRIS, this diagram is just one example of how an IPaaS might work with BetterCloud at your organization.
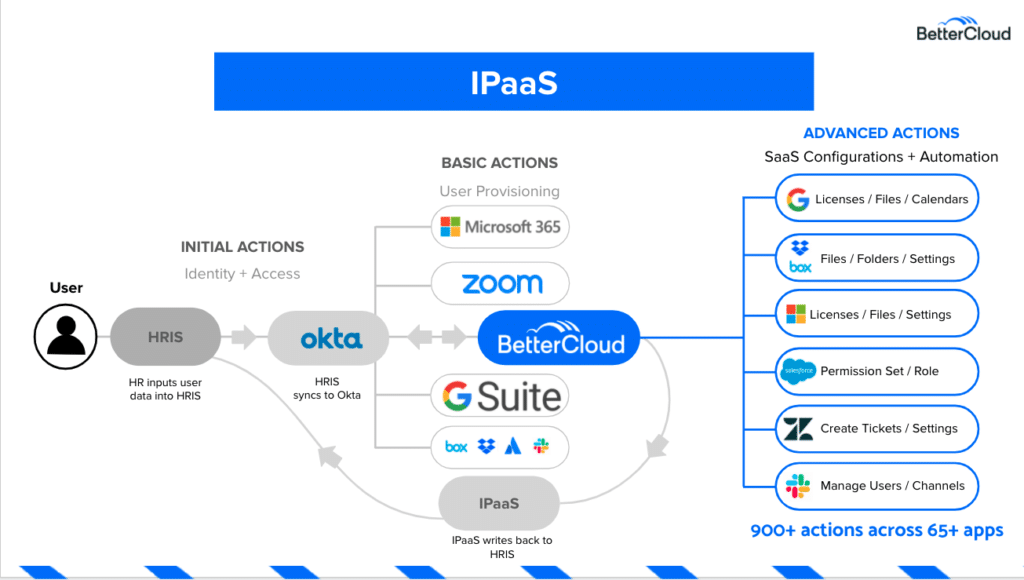
According to our IT folks, this setup tends to be necessary for organizations that use legacy systems. Many of those legacy systems don’t work seamlessly with newer tools like BetterCloud—and in these instances, an IPaaS connects all your systems together.
In this concept, the organization’s HRIS syncs to Okta, which triggers BetterCloud to perform all the magic we’ve discussed several times in previous sections. Once BetterCloud has completed the advanced actions, it syncs back to Okta, which then syncs with the IPaaS, and finally back to the HRIS.
One of the major appeals of an IPaaS is that they enable you to sync data from a variety of sources. But this also means that an IPaaS can live anywhere in an IT architecture. If you’d like to connect your IPaaS directly to BetterCloud, be our guest. If you’d like to connect your IPaaS to something else, we can help you figure that out.
Architecture with security tools like CASBs and SSPMs
In the current security landscape, the biggest threat isn’t a hacker breaking into your server; it’s a well-meaning employee misconfiguring a file sharing setting. This is why a SaaS management platform fits into your tech stack as a security tool.
BetterCloud vs. CASB/SSPM
Many IT leaders ask if they still need a CASB or SSPM if they have BetterCloud. The answer is usually yes, but for different reasons.
- CASBs or SSPMs, like Netskope or Zscaler, are “in-line” tools. They sit on the network and watch traffic. They are great at blocking a user from downloading a file to a personal device.
- BetterCloud is an “API-based” tool. It sits inside the application, making it context-aware. It can see things a CASB cannot, such as “Who has ‘Owner’ permissions on this file?” or “Is this third-party app integrated with our Microsoft 365 environment?”
In a nutshell, pairing an SMP with a SSPM tool enables proactive threat detection and configuration monitoring across the entire tech stack. Although CASBs offer very advanced data loss prevention (DLP) and threat protection for both SaaS and on-prem applications, SMPs complement them by providing administrative control, centralized management of SaaS applications and users, and file governance capabilities.
Especially in larger companies and enterprises, or certain industries like healthcare and finance, a comprehensive software stack for IT will use both an SMP and CASB. As CASB protects the network perimeter, BetterCloud protects the data and configurations.
If a user shares a sensitive document via a public link, BetterCloud detects that sharing, instantly unshares it, and notifies security of the policy violation.
Only SMPs solve the Shadow IT problem
To keep a secure tech stack, one of the most difficult parts of managing a modern software stack is knowing what is actually in it. Employees are savvy; they will sign up for any new tool using their corporate email without telling IT.
BetterCloud acts as a continuous discovery engine. By integrating with your SSO logs and financial systems, like Coupa, it provides a 360-degree view of every piece of software being used, whether sanctioned or unsanctioned.
This allows you to take action to eliminate apps that threaten both your security and your budget.
Now, how does BetterCloud fit in your tech stack with a Security Incident and Event Manager (SIEM)?
SIEMs are complementary to BetterCloud
It depends on how you want to use those tools together. Customers often use a CASB with BetterCloud for on-device or on-endpoint proxy protection, and an SIEM for security analytics, dashboarding and security data storage.
For example, IT might use a SIEM to load all of its SaaS applications’ syslogs into a single dashboard. An administrator can then weight that dashboard with data from BetterCloud to limit alert fatigue.
SaaS management platforms fit into your tech stack as the financial layer
Finally, SaaS operations management tools have also evolved to be finance and accounting tools. It doesn’t just manage users; it manages the apps, licenses, contracts, vendors, dollars, and budgets. Here are some examples:
- Discovery: BetterCloud finds an orphaned subscription that was being paid for by a department head who left the company months ago.
- Optimization: It identifies 50 licenses of a design tool that haven’t been opened in 90 days.
- Action: It automatically emails those 50 users asking if they still need the tool. If they don’t respond, BetterCloud can automatically deprovision the license, saving the company thousands of dollars per month.
- Alerting: It tracks vendor contracts and renewal deadlines preventing accidental automatic renewals.
Make managing your tech stack easier today
The goal of a modern tech stack is not to have the most tools; it’s to have the most productive and cost-effective tools. As we approach the last part of the 2020s, the speed of AI and business will only increase. Organizations that rely on manual SaaS management will find themselves buried under a mountain of tickets, security risks, wasted time, and lost spend.
One thing is certain, though – by implementing a dedicated and continually innovating SaaS operations management tool, you are doing more than just managing the software stack. You are building a scalable, automated, and secure foundation for your entire business by:
- Centralizing orchestration: Don’t let your apps live in silos. Use BetterCloud to bridge the gap between HRIS, IDaaS, and ITSM.
- Automating the mundane: If a task must be done more than twice, it should be a BetterCloud workflow.
- Prioritizing fine-grained governance: Moving beyond “can they log in?” to “what can they do inside the app?”
- Focusing on visibility: You cannot secure or optimize what you cannot see. Use BetterCloud for continuous discovery of your software stack
In closing, where does BetterCloud fit into your tech stack? Again, examples discussed here are not one-size-fits-all solutions. Your IT tech stack, along with your policies, processes, apps, budgets, and people are individual to your organization. How BetterCloud best fits in your IT tech stack will also be unique.
Ready to see how Gartner Magic Quadrant Leader BetterCloud can transform how you manage your tech stack? Request a demo and let’s map out your architecture together.
Editor’s Note: This is an extensively updated article. As the modern enterprise software stack has grown in complexity, the SaaS management platform has evolved into a mandatory orchestrator for all IT operations.
FAQs on how BetterCloud fits into your tech stack
Q: Exactly where does BetterCloud fit into your tech stack if you already have an IDaaS?
A: While an IDaaS (Identity as a Service) like Okta or Microsoft Entra ID manages the entry point to your software stack, BetterCloud handles the in-app orchestration. The IDaaS creates the account, but BetterCloud executes the granular configurations—such as setting up Slack channels, folder permissions, and email delegations—that an IDaaS cannot reach via standard SSO protocols.
Q: How does BetterCloud interact with my existing ITSM like ServiceNow?
A: BetterCloud acts as the fulfillment engine for your ITSM. Instead of an IT ticket being a manual task for a human admin, the SaaS management platform fits into your tech stack as an automated worker. When a request is approved in the ITSM, BetterCloud uses its API connections to perform the work (like granting app access) and then automatically updates and closes the ticket.
Q: Does adding a SaaS operations management tool make the software stack more complex?
A: On the contrary, it simplifies it. Without an orchestration layer, your tech stack is just a collection of silos. A SaaS management platform provides a single pane of glass, allowing IT to manage hundreds of different apps from one interface. It reduces the burden on IT teams by automating repetitive tasks across the entire software stack.