Content Scanning for Sensitive Data: Part 1 of Compliance Essentials in the SaaS Era
September 4, 2020
3 minute read
The time has come: Regular content scanning for sensitive data should be part of every data privacy and security compliance program.
Confidential and personal identification data leaks happen more often than you think. It’s the email containing personal information that got sent to the wrong person. Or it’s a restaurant’s proprietary recipes stored in Box with public file sharing settings.
This type of unstructured data lives everywhere; it’s your customer contact info, trade secrets, or Social Security numbers. Do a quick mental content scan of what’s on your computer and you soon realize it’s filled with sensitive data. Now, since every business on the planet is run on files like these, the potential for long, slow, and ruinous data leaks surrounds every business all the time. Indeed, time for automated content scanning for sensitive data.
But first, a quick reminder on compliance.
Security compliance is about passing an audit
Okay, that may be an oversimplification of the laws and standards that help protect us all. But to an organization seeking to prove compliance to a standards body or regulator, compliance equals “audit.”
And in an audit, the auditor follows three fundamental steps to understand:
1. What do you say you do for effective security and privacy compliance (e.g., the documented data privacy and security policies and processes)?
2. Does what you say satisfy requirements of relevant laws, regulations, or standards?
3. Do you do what you say?
So compliance starts with a security policy. And that security policy should cover data protection.
Content scanning for sensitive data shouldn’t hamper users
To combat data leakage, organizations have long used Cloud Access Security Brokers (CASBs). After all, they enforce security policies and stop leakage across the cloud as users and devices attempt to access cloud resources. The only problem is, CASBs are usually strict. And strict means limited.
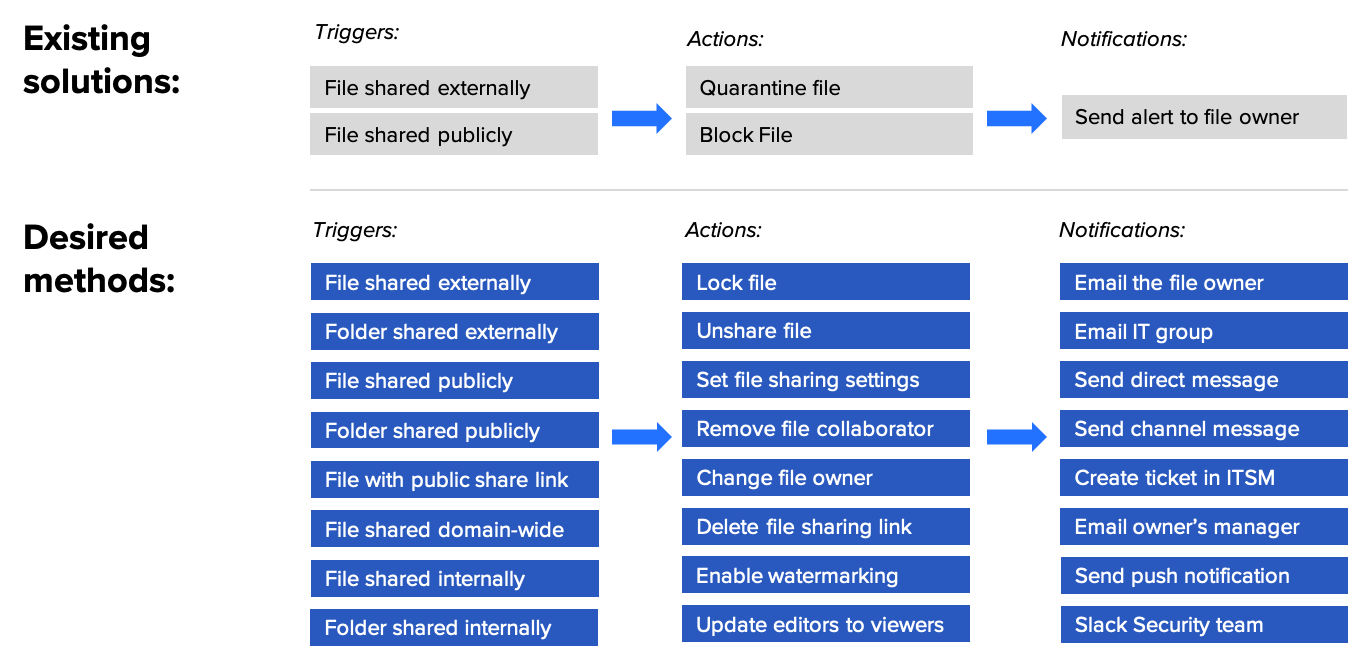
When they do scan content for sensitive data—and find it—the only action they can take is to quarantine or block a file. Since CASBs don’t and can’t consider operational context, user productivity takes a hit.
So how can you boost your organization’s security and productivity, while proving compliance with your security policy? The answer is content scanning for sensitive data that considers operational context. Only a SaaSOps platform can do that.
3 steps to getting your SaaSOps platform to scan content
There are three key steps to effectively set up content scanning to protect sensitive data.
1. Create granular data protection policies.
Create granular data protection policies that can pinpoint suspicious activity and are non-intrusive to employees’ productivity.
The level of granularity you need covers files and folders and the range of how sharing occurs. For example, is data shared externally, publicly, domain-wide, internally, or within departments or groups?
The security policy also defines actions to take if the scan uncovers a violation. A granular policy should dictate the most appropriate action from a greater range of actions that consider context. For example, if a content scan finds a Social Security number that’s shared externally, a SaaSOps platform can unshare the file and notify the boss. If it finds an internal file link of an embargoed press release that shouldn’t be shared, a SaaSOps platform can delete the link and inform the file owner.
Finally, your granular policy should define sensitive data across applications.
2. Automate your granular policy with alerts and audits.
A SaaSOps platform makes it easy; simply select from the 90+ pre-set data identifiers for common sensitive data types across 25 different countries. You could also create your own custom regular expressions to define any niche or non-standard data types. Then run audits that scan content contained in your entire environment or select files to find the most common sensitive content, such as Social Security, credit card, or passport numbers. You can even set up alerts to notify the appropriate teams when files with sensitive data are overshared.
3. Set up automated workflows to prevent sensitive file oversharing.
A SaaSOps platform leverages the granular context stored on users to offer a remediation plan that is not intrusive to user productivity. It can also allow you to build workflows that prompt file owners to confirm (via email or Slack bot integration) whether a file is shared appropriately or not. That way, admins build an automated checkpoint for employees to confirm whether a shared file was intended to be shared. In addition, it can automate any required remediation.
You can set up automated workflows to remediate threats by accessing a library of actions. This extensive library includes administrator actions across all connected applications and on-demand macros to quickly remediate the oversharing of files with sensitive content. This is how a SaaSOps platform offers granular context on users and groups to help determine appropriate remediation paths.
Follow these three steps to regularly scan content and protect your sensitive data. Your organization will get happier, more productive users, while it reaches new levels of data security and compliance success.



