SECURITY & COMPLIANCE
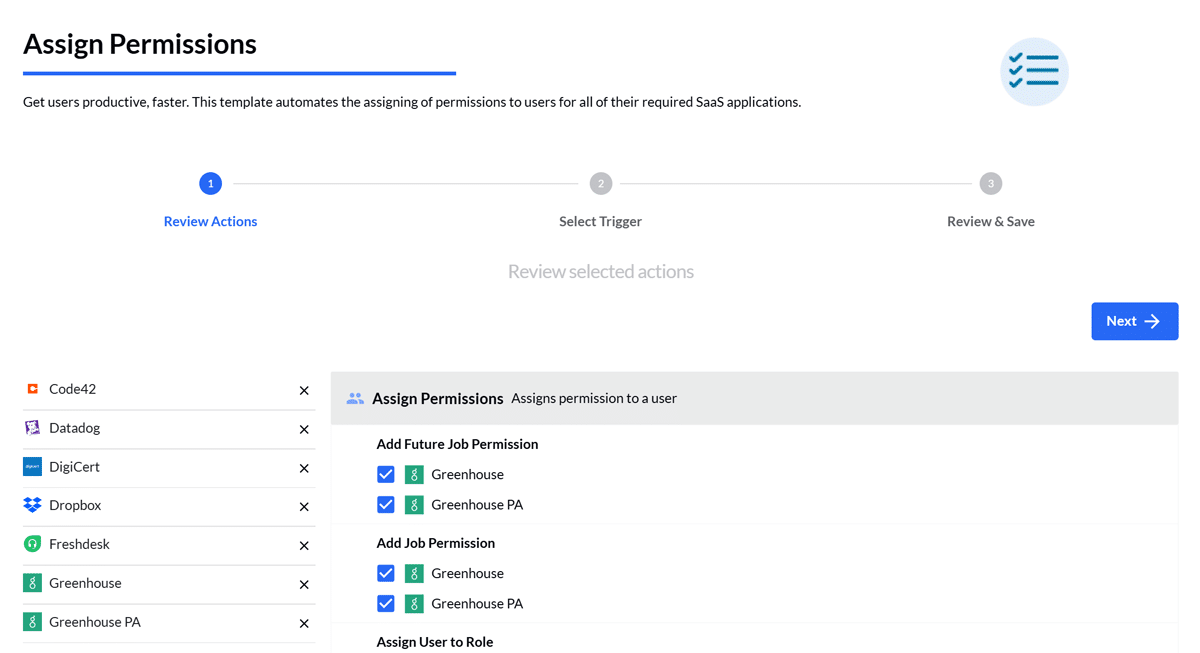
Give your help desk superpowers
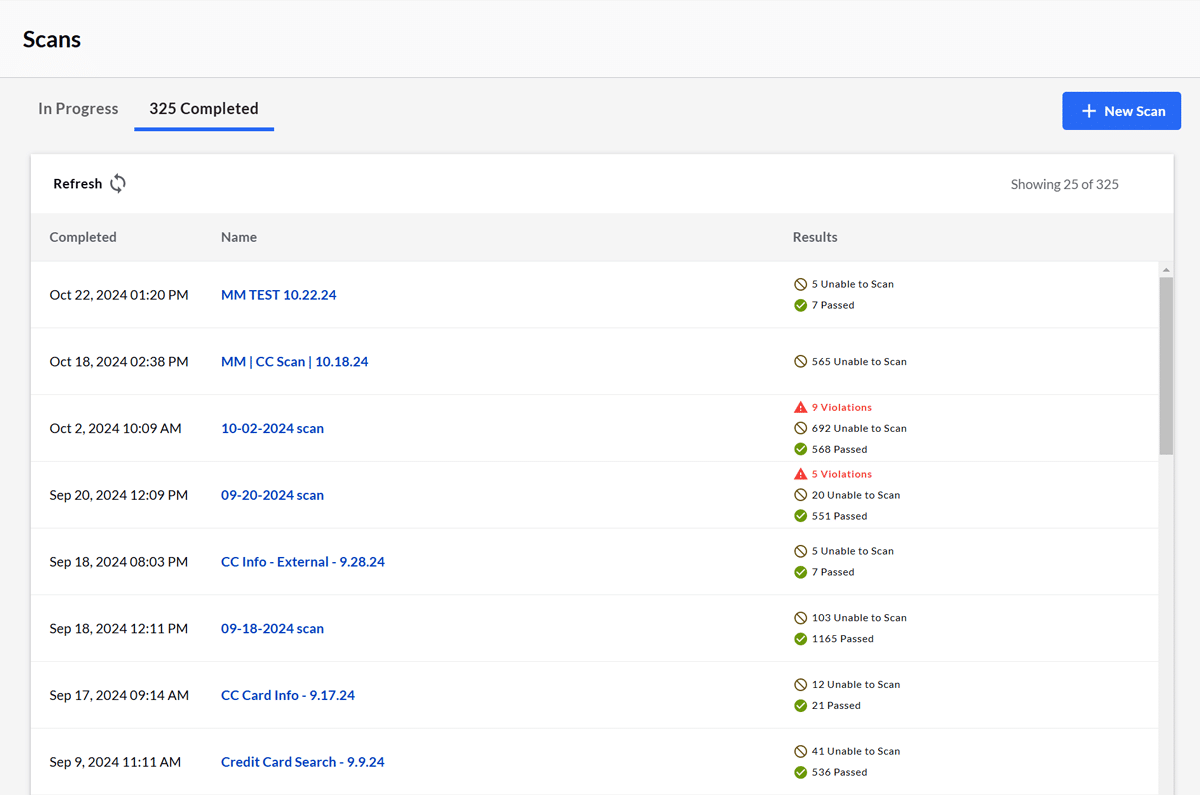
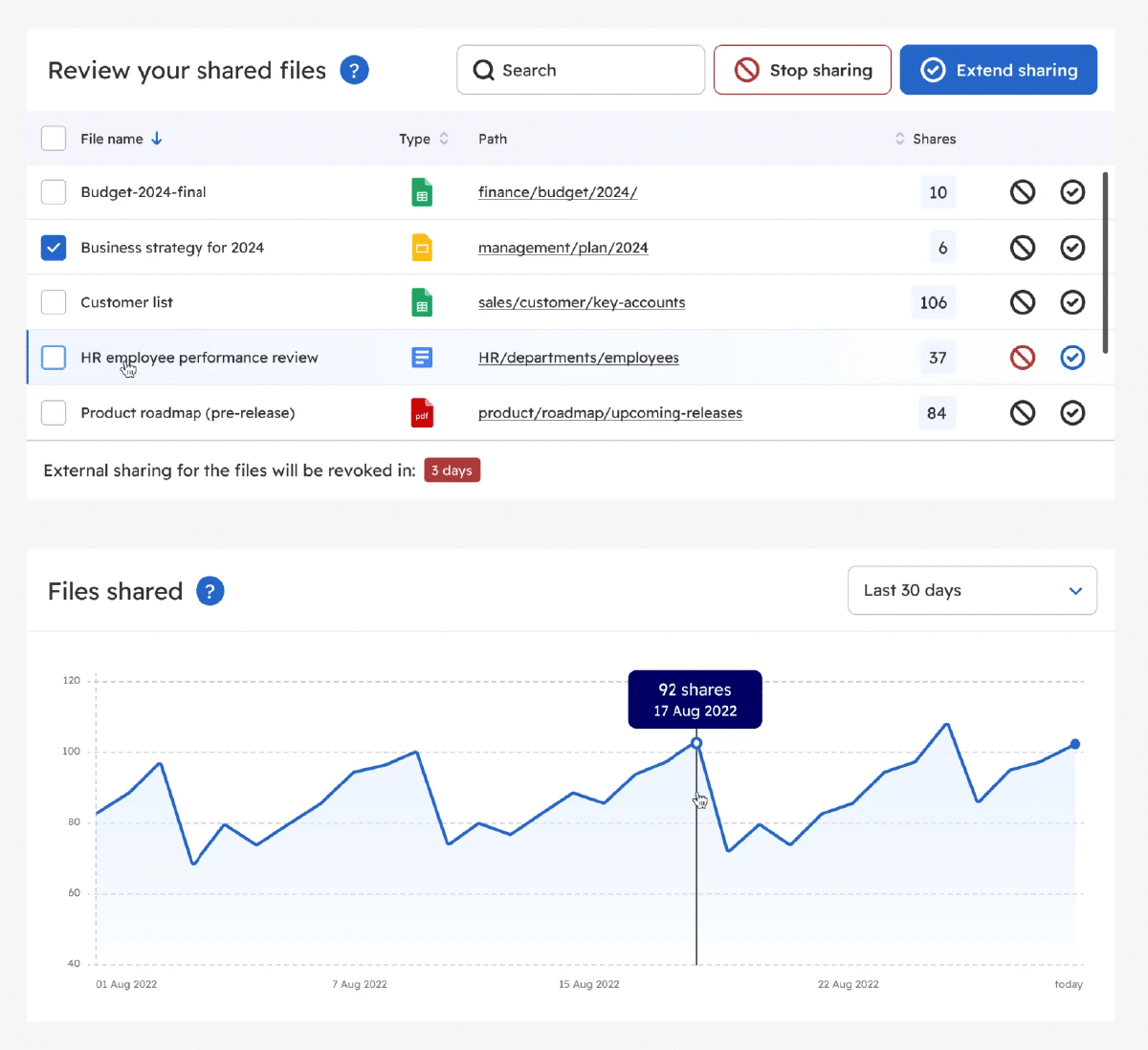
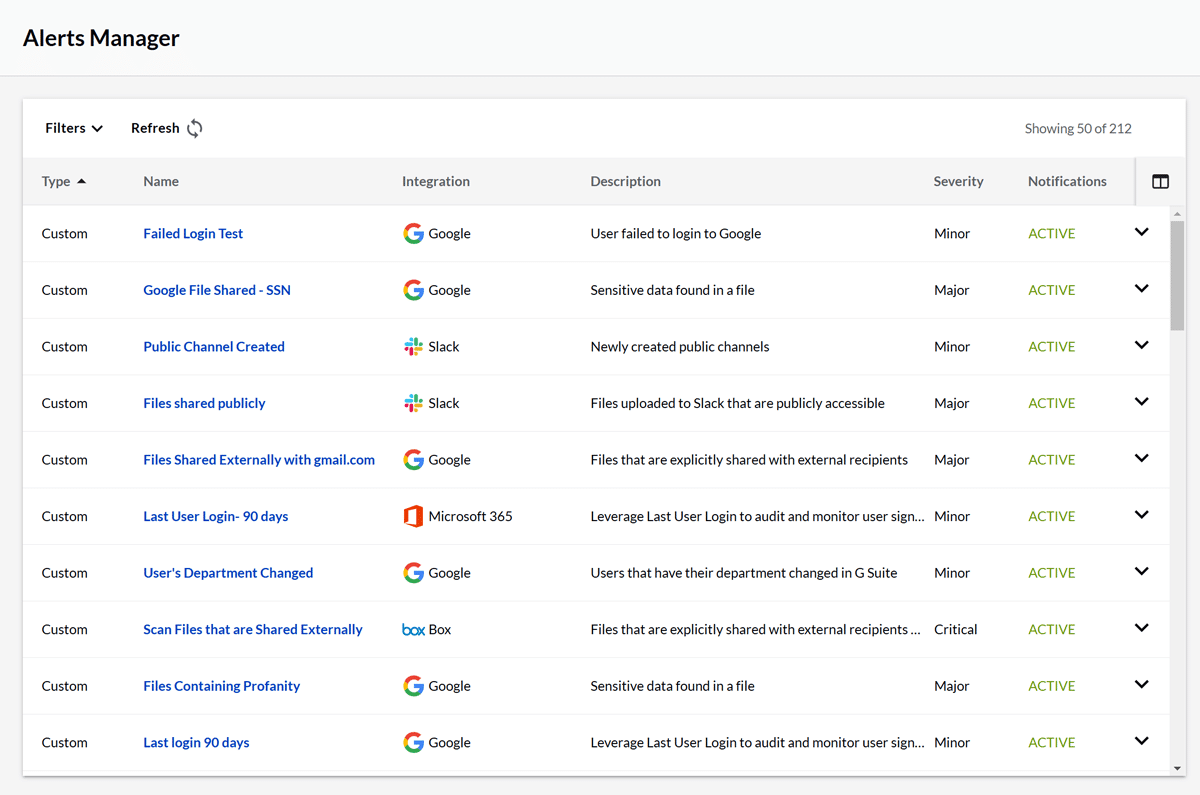
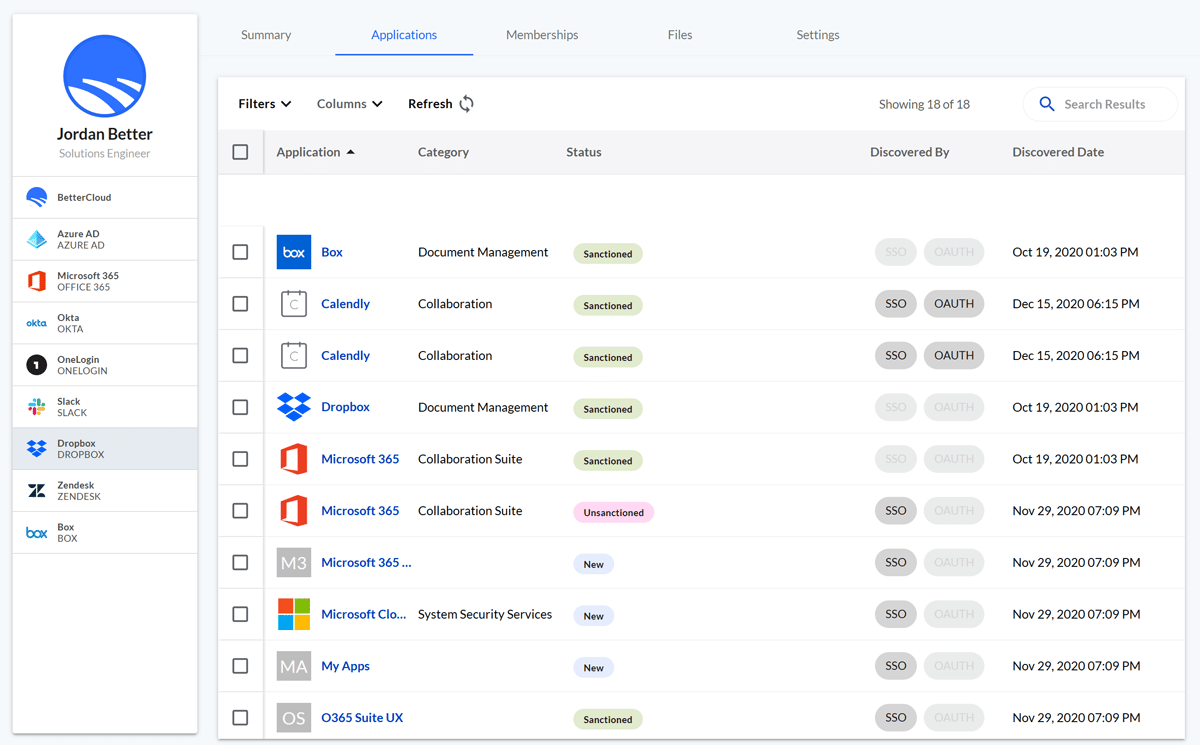
Get control over your apps, data, and users to ensure that all your security standards are being met.
“
BetterCloud offers more granular alerting than what is offered through specific apps, such as being able to audit file security.”
— Hazlitt Van Goethem, Junior Site Reliability Engineer, Curve
Benefits of BetterCloud
Help IT and security teams save time auditing potential exposures and demonstrating that security requirements have been met
See what else BetterCloud can do for you
IT teams chose BetterCloud: Leader in the G2 Spring 2026 Grid Reports
Recognized as a Leader in 30+ categories in the G2 Spring 2026 Grid Reports, including SaaS Management, SaaS Spend Management, and Data Loss Prevention, BetterCloud helps IT teams reduce manual work, strengthen security, and get more value from every SaaS app.