How Risky Is an Interaction? Here’s How to Tell (and Level Up Your SaaSOps Security)
January 16, 2020
4 minute read

This article is excerpted from BetterCloud CEO David Politis’s new book, The IT Leader’s Guide to SaaSOps (Volume 2): How to Secure Your SaaS Applications. To learn more and get a copy of the book, click here.
In the world of SaaSOps, not all interactions are created equal.
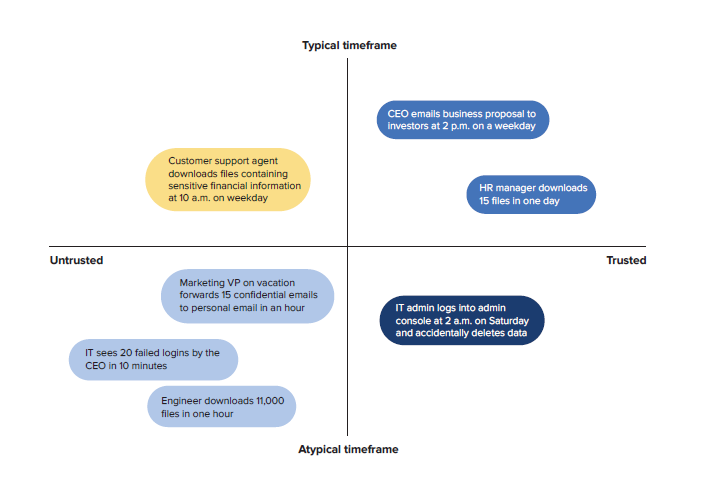
Similar to the idea of trusted vs. untrusted users, some interactions are far riskier or more important than others. Some warrant more scrutiny; others, less.
But how do you classify interactions? What implications do they have for IT teams and your data protection strategy? That all depends on several key factors I call “dimensions.”
Identity: Who’s doing the interacting?
Identity—who is doing the activity, and who they’re sharing data with—plays a critical role in how you think about interactions. You can think about identity in a few ways:
-
- Business role. Is the user a C-level executive or is he an intern? Senior management will have access to more sensitive and valuable data than, say, a part-time intern. It’s why “whaling”—phishing attacks that specifically target executives—exists.
- External vs. internal. Does the user belong to your organization or is he outside it? External users (like contractors and partners) need special attention since they are outside the company. The least privilege model dictates that their access be restricted in some way, whether by time, group membership, privileges, etc.
- Part-time vs. full-time. Is the user a part-time (temporary) or full-time worker? According to a Forrester research report, temporary employees have a much higher turnover rate than full-time employees; they are much less loyal. On top of that, many enterprises do not have dedicated security policies and controls for temporary workers due to IT staff capacity limitations or the misguided belief that short-term workers “don’t have enough time” to be dangerous.
- Remote vs. in-office. Does the user work remotely or are they in the office? Remote workers pose their own set of challenges—the major risks being the inability to enforce security, a lack of commitment to security best practices, and risky behavior on their part. If a remote worker is using public Wi-Fi (say, at a coffee shop) to access company data, that free hotspot doesn’t require any authentication to establish a network connection. This means that hackers can potentially access all the info a remote worker sends on the internet, including account logins, credit card information, confidential business data, you name it.
- Trusted vs. untrusted. Of course, the definition of trust will vary across orgs. Based on who the user is and what kind of data they have access to, are they trusted or untrusted in your eyes?
Time: When are these interactions happening?
Thinking about time—not only when, but how often an interaction occurs—can help you decide if it’s to be trusted or untrusted. Think about:
- Time of day. Are these interactions happening during work hours or outside work hours? If your work culture is one where employees typically “disconnect” from all things work-related after five p.m., after-hours interactions may signal an issue.
- Time of week. Are these interactions happening on weekdays or the weekend? The digital workplace means work and personal time are more fluid, but weekend interactions are generally less common.
- Time of year. Are these interactions happening on holidays or non-holidays? If you work in a seasonal industry, is there a flurry of interactions during the off-season?
- Vacation/sick days. Are interactions happening while a user is on vacation, sick, or otherwise out of the office?
- Frequency. Are interactions happening at an expected frequency? If there’s an abnormally high number of interactions in a short timeframe, this can be a major indicator that something is awry. Here are two examples:
- Multiple, consecutive failed logins in a short window. Perhaps the user has forgotten their password, or perhaps they are the victim of a password-guessing brute force attack.
- An unusually high number of file downloads in a short window. According to CSO Online, modifying large numbers of files in a short period of time can be a warning sign of an insider threat. An exiting employee may be tempted to download files in bulk and take them to a new company.
Data classification: How sensitive is the data?
Users interact with data every day to do their jobs, but not all data is created equal.
How sensitive (or non-sensitive) is the data accessed by the interaction? If bank account numbers were exposed publicly, you’d likely be very concerned; a community calendar, maybe not so much.
“Sensitive” can mean a few different things. Think about:
- Personal information. Are users interacting with PII? Examples of PII include biometric data; passport numbers; Social Security numbers; bank account numbers; driver’s license numbers; and medical, educational, financial, and employment information.
- Business information. Are users interacting with any confidential information that, if discovered by the general public or a competitor, could pose a risk? Examples include trade secrets, patents, product roadmaps, sales pipeline data, credit card numbers, financial information, customer lists, exit interview notes, tax documents, M&A plans, proprietary research, employee salary information, etc.
- Dangerous or harmful information. Are employees using profanity in their files or phone conversations? For EDUs, are students referencing drugs, bullying, suicide, or self-harm in their interactions? It’s important to remember that sensitive information isn’t limited only to personal or business data.
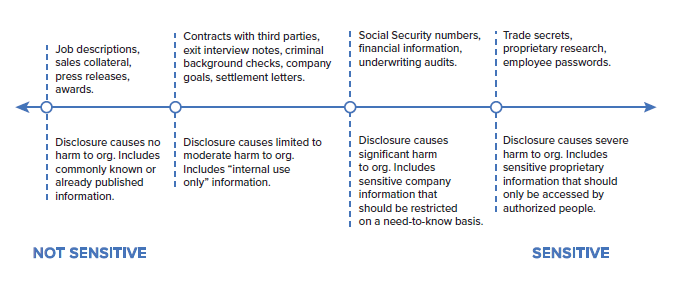
Think about how you’d classify your organization’s data. What’s considered sensitive and what’s not? If this data was disclosed, would it cause severe, significant, limited, or little to no harm to your organization?
No single factor can define how risky an interaction is. It’s the confluence of all these factors—identity, time, data sensitivity—that you need to think about when determining whether an interaction is trusted or not. Your definition of trust will vary based on the complexity of your IT environment, industry and compliance requirements, and business needs.
In our next blog post, we’ll discuss how you can start protecting data with a three-step SaaSOps action plan.
Looking for more SaaSOps info? Check out www.bettercloud.com/what-is-saasops/ for in-depth webinars, books, success stories from SaaSOps practitioners, and more.
To learn more about how BetterCloud can help you manage and secure your SaaS applications, request a demo.