Seeking SaaS Management Success? These 11 Guiding Principles Will Get You There
February 9, 2017
28 minute read
Technology is awesome. Managing technology is difficult. And preparing for technology challenges that don’t even exist yet–well, that’s absolutely daunting.
But it doesn’t have to be this way.
There are baseline best practices that, if followed, will help better position your IT team and organization for success in the near future and the years to come.
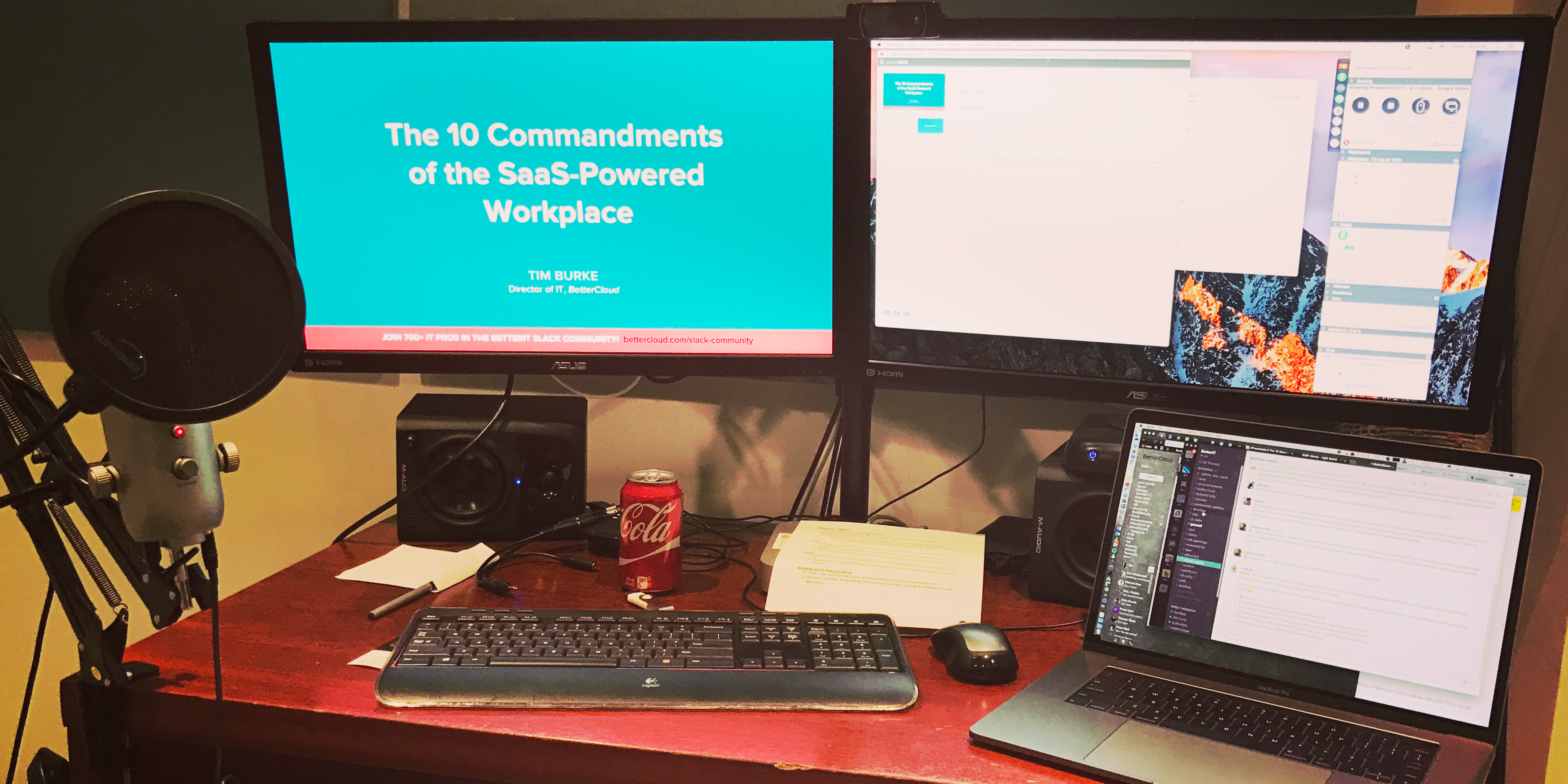
We call these principles: “The 10 Commandments of the SaaS-Powered Workplace.” (Shh…there are really 11 on this list.) BetterCloud Director of IT Tim Burke recently held a webinar on the topic.
Below you’ll find the webinar recording and transcript. You can download the webinar slides here.
http://bettercloud-1.wistia.com/medias/jv04jj86m2?embedType=async&videoFoam=true&videoWidth=444
Webinar Introduction
All right. Good afternoon. Tim Burke here from BetterCloud. Thank you so much for joining me for the 10 Commandments of the SaaS-Powered Workplace webinar. Before we get started, just a couple quick reminders. First off, if you’re not a member, please join the BetterIT Slack community. Only about half the folks in there are actually BetterCloud customers. It’s really a community focused on cloud-powered IT in general, so we talk about a whole bunch of stuff outside of BetterCloud and outside of G Suite.
[ad-banner image=”https://www.bettercloud.com/wp-content/uploads/sites/3/2020/05/monitorpost-ad-video.jpg” url=”https://www.bettercloud.com/bettercloud-product-overview/”]We’ve already got a couple questions that I’ll get to at the end, but by all means, feel free to submit questions throughout the entire webinar and we’ll get to them at the end. Then, if anyone wants to chat with me directly, I am on the BetterIT Slack, just @tim, T-i-m, so find me there.
Before we dive in, if you’re not familiar with BetterCloud at all, we’re the first multi-SaaS management platform. We help IT departments unify the management of all of their different SaaS apps. We used to do just G Suite. We’re now expanding out into the SaaS-powered workplace, so if you’d like to learn more, head over to bettercloud.com, or in the Slack community there’s a BetterCloud channel.
Anything that you’d like to know, any introductions, any questions, by all means check it out. Now, I am a little biased because I do work here, but I think it’s a really awesome product and it really does enable me day to day and a lot of really awesome customers day to day. With that being said, let’s get into this. First off, why are you here? We’re going to cover these 10 fundamentals that I think are really the way to set a perfect groundwork, a solid foundation for a SaaS-powered company, SaaS-powered IT department. Now, these are pretty general. We wanted to apply them to everyone, and we wanted to make them pretty future proof.
They’re all best practices, they’re all things that we do internally, and depending on the maturity of your organization you may already be doing some of these or all of these, but hopefully everyone at least has a takeaway. But you as an IT professional are here for just two simple reasons. With all of this digital change that’s happening, you’ve got to facilitate it, you’ve got to hasten it, and with everything changing so fast, you’ve got to secure and you’ve got to manage that digital transformation. So, every organization is undergoing this digital transformation. Now, you could be in the social and collaboration space or analytics or mobile, but we believe that for the core, all businesses in the future we’re going to be looking at a completely SaaS-powered workplace.
The fully SaaS-powered workplaces are this 29% of digitally maturing organizations. The rest of the 71% are either in this early or developmental stage where they’re trying to become and trying to stay digitally mature but maybe aren’t quite there yet, and that goal to become digitally mature is exactly what’s pushing this tremendous growth in the usage of all these different SaaS applications. Some survey data that we have, 31, the median number of sanctioned SaaS apps in organizations with over 500 employees. Now, every organization is adopting SaaS at a different pace, and it’s far outside of just G Suite or just Office 365 or just Salesforce.
This SaaS-powered workplace is a huge number of these little niche SaaS apps. Here at BetterCloud, we use over 100 SaaS applications. That’s almost one for every user, and for IT, this means that no matter how digitally mature we actually are, how sophisticated we think our SaaS-powered workplace is, IT has a responsibility to manage all of these applications to the best of our ability. Alright, so we’re going to open up a quick poll question. What stage do you think best characterizes your level of IT expertise? Do you feel like you’re early, just getting started with this digital transformation? Do you feel like you are developing, you’re in the middle stages?
Or, do you feel like you’re maturing? Of course, also this is a great time to drop questions in the Slack channel. We’ll get to those at the end, but I’m going to leave this poll open for a little bit longer and then we will share the results with you guys. Alright, awesome. Well, we have a very engaged audience today. We’ve got 85% of people voted, thank you very much for that, and you want to take a look at the results? Got 26% think that they’re early, 52% think that they’re developing, 22% think they’re maturing. Hopefully for all of you guys, everyone, there’s something to take out from here, and with that, we will hop back into the slides.
Know Your Environment
Alright, so commandment one, thou shall know thy environment. Getting a little biblical here. What does this mean? Half of all IT professionals believe that they lack visibility, 61% believe that they don’t have enough control over their SaaS applications. What we’ve heard from customers, from prospects, from other IT folks, the majority of organizations maybe are not doing the best job managing all of their SaaS applications. Now, sometimes SaaS doesn’t make it easy and your ability to control and manage them may not be exactly what you’re used to in the on-premise world, but if you don’t even understand the base state of where you’re starting, it’s really hard to know what the risks are and it’s really hard to know how to move forward.
Here, I’m taking the approach if you inherited an IT department or maybe you’re the first hire, maybe you’re in the beginning of a digital transformation project at a really big company. How do you lay the groundwork? Well, you lay the groundwork by capturing the current state, but with that, 31% of non-executive IT believe that former employees can still access data. Obviously this is a risk, obviously this is what we get paid not to have happen. I think 31% is a little low. Deeper visioning is something that a lot of companies really don’t excel at, so this could definitely be higher, and this is definitely a risk. We’ll talk about that a little bit later, but what I’m trying to say is you can’t fix what you don’t understand.
Before you make any changes to anything, you capture the current state of it, right? So, how do we do that? Well first off, we build a really comprehensive IT service catalog. Now, all of these are basically the columns that we took out of ours. These are the recommendations for what a really good IT service catalog should have. Just a couple things to call out. We do capture billing information including contract information, we have both the end user URL and the admin URL, so it’s a really easy way to just hop into those services and for every service, we have a primary owner and a secondary owner, so that there’s always coverage on the service and it’s really clear to know there’s an issue with the service who you’re going to.
Once you’ve done all this and it’s not a one off, it’s something that you need to continuously iterate on, make sure that it’s up to date, but once you have a good service catalog, you can hop into a budget. Your budget is the baseline for all of your operations. Your budget will never tell the whole story, but it certainly does make things easier. If you can figure out where you are, especially if you can cultivate a really good relationship with your finance team, you can quantify what you’re trying to do and why you’re trying to do it. It’s so much easier than just pulling projects out of a hat.
While you do this, you might find that you’re paying for redundant, duplicative services, or people within your organization are doing shadow IT, maybe on personal credit cards and then expensing them. So, how do we start to tackle this? Well, I would say we should start by shadowing and surveying the users, being consultative with them. Shadow IT is not always the worst thing. The way that I see it, it’s a pretty relief valve, it’s almost your users sending up a flair that maybe IT isn’t providing them all of the services that they really need so they’re going off and doing it on their own, so not letting your ego get in the way and listening to your end users.
They actually know their needs really, really well. They may not know exactly what services and what integrations they need, but when it comes to business processes and the day-to-day experience, they’re actually smarter than you think. If you listen to them, you can capture their requirements, you can be that person that ties everything together and delivers those really fantastic services. We have this kind of three level idea here, that you have core services, that if you lose these core services your business would just stop running. Connected to these core services, you have what we call connective services, and these are important but maybe not business critical, but they pull data in and out of the core services and are heavily integrated.
Then, outside of that you have shadow IT. As an example, here some of our core services would be like G Suite, Salesforce, NetSuite. Without those, we can’t effectively run a business. Now, connected to all of that we have things like Lucidchart, DocuSign, Smartsheet that provide additional value but are not a core service. Now, at one point we had Slack as shadow IT. Our developers loved Slack, it was a free account, we had no provisioning or deprovisioning, it was a single sign-on, and we tackled that head on.
There’s actually a great post in the BetterCloud Monitor telling the story about how we onboarded Slack when it was shadow IT and secured it. We started working with Slack and we eventually connected it to all of these core apps. We started adding value with integrations, with single sign-on, and then finally when it was really truly integrated, when it started becoming this alert system of record, this group chat of record, it became a core service for us, and this is the model that we like to follow. Identifying challenges, tackling them, onboarding these apps, and solving real problems.
Seek Simplicity
You should always seek simplicity. Thou shall always seek simplicity, as you’re going through this. Now, I’m sure everyone knows the KISS principle, Keep It Simple Stupid. Do you really think that you’re good at all of this? Because you know what? We think it’s impossible to do everything well. I have to throw credit to this slide for Andy Schwab who spoke at our last Cloud IT Live event. He has this idea for ultralight IT that you only do what you can do well. It’s kind of an ego defining moment that sometimes you do need to step back and say, “You know what? As an IT department, we’re really not great at hosting mail. Google can do that better for us. We’re not great at running a datacenter. Someone else can do that better than we can.”
Eliminating this complexity as much as you can, doing only your core, what you’re absolutely great at, and then looking for others that have their core, what they’re absolutely great at, and deferring to them. You want to identify and reduce this unnecessary complexity. We’ve broken this down into quadrants and if you’re looking at something that’s very complex, but doesn’t deliver a lot of business value, if it’s down here in the bottom left, it’s probably not even worth your time.
Now, if it’s something that is low complexity but can add a lot of business value, the example I have here is Slack, not very complicated, not very hard to implement, but when used correctly delivers enormous business value. That is your sweet spot. That’s not to say that you should shy away from complex services, because they definitely have their place, but you need to weigh that against the business value, and consistently ask yourself every single day, “Is this a good use of my time? Is this a good use of my team’s time? Is this a good use of my budget?” There are a lot of things that you can probably cut out you might not or shouldn’t be doing.
Understand That Change is the Only Constant
Thou shall always know that change by thy only constant. A little bit of a mouthful there. The pace of tech adoption is speeding up. I feel like I don’t even need to tell you that. The telephone, the iPad, the smartphone, wifi, 3G, 4G, everything is being adopted absolutely at an exponential pace, and this brings some problems for us because we need to stay up to date with all of this. You need to anticipate this change and prepare for it, and at the end of the day your job as an IT professional is to stay up to date. If you don’t learn new skills, if you don’t pick up new services, then you have a shelf life maybe of a couple years in this profession, and if you don’t stay up to date, you will eventually miss the boat.
So, how do you stay up to date? How do you deal with this exponential complexity, exponential adoption, and exponential change? Well, first off, if you’re doing strategic planning, you want to look at shorter planning cycles, and so breaking your plans into three different segments of a short term, a long term, and then an over the horizon kind of plan. Now obviously these depend on the size of your organization, but overall, you need to be ready for a short term plan and have one that’s flexible. Now, you break these projects into three different segments. The critical, the important, and the nice to have.
You look at your requirements and then it might be nice to have some stretch goals, it might be nice to have a little bit of icing that you can add on top, but you can’t lose sight of what’s critical or what’s important in these projects. Of course, getting ahead of change. Getting your IT team on early access programs, whether it’s early access or trusted tester, or beta. If you can see things before they go out to your end users, you can support them, but no one in IT likes surprises. However, you have to be agile because plans change. As an example, here at BetterCloud we may be moving offices or one of our offices at some point this year.
I know that that’s going to be at least a month long project for my team, however, I don’t know exactly when it’s going to happen yet. We’re at the mercy of brokers and landlords and build outs and construction teams and all of that. I know that I have this massive thing on my plate this year. I’m not exactly sure when it’s going to happen yet, but I’ve scheduled the rest of the year in this kind of medium term plan so that we can be flexible and if that date does move, we can move our other projects around it, because there are a lot of things that you’re tasked with that you may not have as much leverage as you want on timing. I can’t make an office appear and be ready, so with these dependencies that you have outside of IT, you need to be prepared for those and you need to have some wiggle room, have some buffer both in timing and in budget. The old adage, “under promise and over deliver” I think is really powerful.
Align IT’s Goals with Your Organization’s Goals
Thou shall align with thy organization’s goals. Well, what do we mean here? You need to understand two things. How does your organization make and lose money, and how do your organization’s employees use the technology that you provide them? For number one, talk with your sales team, talk with your CFO and your finance team. Look at every department and see how they contribute to the bottom line of the business. If your entire company has really overreaching goals, then look at them and make sure that your IT goals align.
In the end, though, every single decision that you make either should help your organization make money, or reduce its chance to lose money. On the security side, generally we’re talking about risk, but overall, you’re either making money or reducing risk. For number two, be a consultant, meet with the department heads, understand every single user’s goals. I think it’s a really powerful thing to actually shadow your users. Sit down with them for a couple hours and genuinely look at their day to day workflow, see what you’re missing, see if you can identify pain points that maybe they take for granted, but as an IT professional would be really easy for you to solve.
Work Tirelessly to Reach and Maintain Security Maturity
Thou shall reach and maintain security maturity. Another mouthful there. The Enterprise Strategy Group put together this really cool chart that basically in one want simple chart, in a very simplified way, allows you to evaluate how mature your security posture is within your organization. Now, this may be very high level, I bet everyone thinks they fall in different buckets in this, but even on a departmental level, looking at the risks, looking at how everything’s put together, your processes, your procedures, even your staffing, looking at all of that and having a really honest assessment of where you think you are and where you think you should be.
By building out a really mature security model, and then presenting it to the executives is a great way to get buy-in. I always suggest that you need to instill a culture of security from day one. You stress it, and so we start here with onboarding. We emphasize security at multiple touch points during the onboarding process. What we absolutely do not want to do is to instill a culture of fear. We don’t want employees to be afraid of falling victim to a security breach and not reporting it. A little bit of fear or a little bit of suspicion is healthy, but if that fear crosses over to the point where your employees are not comfortable reporting something, then you absolutely have a problem.
For us, it’s no punishment, very open. We actually encourage and reward employees to report things like suspected phishing. We have a deal with them that if a device goes missing, we’ll replace it no cost, as long as we’re told immediately that it happens. We can send a remote wipe command, we can follow our incident procedure, and then it’s done, but we have to know about it and your employees have to be comfortable telling you about it. Some of the practical exercises that we’ve done, we run internal phishing exercises, we use LastPass for credential management, so we’ve done a security challenge program there to get people to stop reusing passwords, obviously a major risk, to use randomly generated passwords, and in general, just understand that it actually is more effective to have a password vault with one very secure passphrase, not a passcode, protected by two factor, and then all of these randomly generated passwords everywhere else.
We have a laptop bounty program where if you see a colleague’s laptop sitting unlocked in the office in a public area with no one else supervising it, and you can get proof of that, then you’ll actually win an Amazon gift card. Everyone at our offices has gotten really good about locking their laptops now, because they don’t want to be the one that gets caught doing it. I have a $100 bounty on my back. I’m the Google super admin, my account, my laptop would be something great to compromise, so if anyone ever gets me, it’s 100 bucks for them. Luckily no one has yet, and it certainly keeps me diligent, but it’s a great way to do some positive affirmation for employees and to challenge them a little bit.
Now, like a lot of companies, we do lunch and learns, and some of the lunch and learn topics are on security. We have a really good dedicated security team here, they put on some great lunch and learns and some great training sessions on everything from phishing to good password habits to single sign-on, to a bunch of internal application security stuff. They’re recognized now as thought leaders within the business. They’re respected and they’re trusted, and that’s exactly the relationship that your users should have with IT and with security.
Trying to bake in all of this security from the start. I cannot emphasize single sign-on. I think it’s one of the most powerful tools you have in your security arsenal. Along with single sign-on, for apps that either don’t support it or for other use cases where single sign-on breaks down, having good password management, enforcing multi-factor authentication on all of your important core services, so for us, LastPass, Salesforce, G Suite, and a couple others. Having proactive reporting, so just as an example, if we see an employee’s account get locked out, we have an alert for the security and IT teams on a private Slack channel, and that gives us two things.
It gives us that proactive reporting so if it is a compromise, or some sort of security incident, we’re aware of it immediately, but for the IT team, it also gives us this wonderful opportunity where we can do proactive support and I’ve come over and asked a user if they needed a password reset long before they were even able to open a ticket saying they were locked out. That was a great way to delight them, and having a really solid incident response plan. You won’t be able to think of everything, you won’t be able to put a plan together for everything, but at least for what you can imagine, you need to have something documented. You can’t make up an incident response plan on the fly. You just cannot.
Automate Work Whenever Possible
Thou shall always seek to automate thy work. What do we mean? The best IT professionals are usually the lazy ones. Bill Gates has this great quote, “I choose a lazy person to do a hard job because a lazy person will always find an easier way to do it.” We look at all of these tasks that are kind of manual, very repetitive. Something that I really like is the phrase, “Making license plates.” It’s very simple, it’s just absolutely menial work, and so what can we do about that? Well, on the onboarding side, we’ve automated the imaging, the building of devices on Mac and PC, the addition of groups and shared folders to users as they’re onboarded, and the provisioning of third party apps like Slack, Dropbox, and Zendesk. All of that happens in almost zero touch manner.
For offboarding, we automate termination of access, transfer of documents, inbox delegation, and notification to the appropriate parties. Especially with this, I think there’s a great case for automation for not only saving time but ensuring that the process is repeatable and done perfectly every single time. We’re humans, we are completely fallible. If we do something 100 times, maybe once or twice we’ll make a mistake, but especially on offboarding, you cannot afford a mistake, even if it is only 1 out of 100, so you automate all of this. Then, for security, we have those suspicious login alerts, lockout alerts that I was talking about before, two factor onboarding. You definitely want to remove all of the barriers to entry for your end users, getting two factor set up.
Then, device updates. Even today, I was able to pull a quick list and be able to reach out to users, updating to iOS 10.2.1. makes things much easier when you can automate it and click one button, automatically follow up, automatically push out the updates, all of that. When you hear automation, you might think of scripting. Honestly, I’m not great at scripting. My BASH is pretty terrible and my Python’s probably worse. Even with that, I’m able to automate a ton of my work. There’s some really great products such as BetterCloud that allow you to automate a lot of this without scripting knowledge, and I really believe the future of automation is more about configuration than coding.
Create an IT Information Hub
Thou shall work to centralize thy users, thy apps, and thy data. Centralization gives you intelligence, gives you the ability to automate, and so where do we start? Users. You need a unified directory. It needs to be your single source of truth. Your apps, you want to choose the best-in-breed applications. I know many of you are not sticking with single vendors anymore, and I think there’s a very good reason for it. I don’t think single vendors can succeed in every single line of business application that you need. This is not 1994 anymore, and so we can integrate all of these products, but we do it as we choose the best ones. However, as we’re choosing the best ones, you want to make sure that you’re avoiding overlap as much as possible.
I have worked an environment before where we actually had OneDrive, Box, and Dropbox at a previous job. It was an absolute disaster. You’d be in meetings, someone would take notes and say, “Oh, I’m going to share it to you.” “Okay, are you sharing that on Box or Dropbox, or onedrive?” It was too confusing. You lost all of the benefits of any of those single services on their own by duplicating them, and so picking the best-in-breed, sticking with them and standardizing on them is really, really important.
Now, for all of your data, you want to centralize this as much as you can so that IT is in control, so you can keep the environment secure. You need to know especially for just your internal use only, let alone your confidential information, you need to know where all of it is. You need to know how it’s managed, and data, whether it’s analytics, whether it’s customer data, the appetite for businesses for all this data has grown like crazy. Everyone’s doing big data and reporting and dashboards and all of that, and IT is here to be the stewards of all of that, the custodians of all of the data.
Transform, Train, Repeat
Thou shall transform, train, and repeat. This poll from MIT Sloan asked end users if they were satisfied with their organization’s current reaction to digital trends. Now, in the bottom here we have the organization’s digital maturity level, and there’s an incredible correlation here, not entirely unexpected, that as an organization matures, as they implement more SaaS, as they listen to the business more, as they enable their users more strongly, users become a lot more satisfied with the organization, with how they react, with how the services are provided. Everyone wants to get to the “digitally maturing” level. I don’t think there’s even a level passed maturing because things change so fast, you need to ride it out.
Even if you are maturing, if you stop maturing, two years goes by and a whole bunch of SaaS happens, then you might have slipped back into developing. This is something you need to keep up with every single day. With this, you want to constantly train your employees. You’re going to transform, you’re going to identify pain points in the business, you’re going to test and you’re going to implement solutions. As you’re doing that, you also need to train your employees. I suggest that you really leverage your vendors. There are a lot of vendors out there that have really good training programs, free training sessions, conferences, even end users support from some vendors.
There’s so many resources out there and available today. Google is and IT professional’s best friend. If your Google skills are sharp, you can figure out almost anything with time. YouTube, there’s great tutorials, troubleshooting tips, and then of course newsletters, and along with that, different communities, Twitter feeds, all of that. Use all of your available resources, make sure that you’re plugged in, make sure that your employees feel plugged in as well. Now, here we really like to involve power users, and these are not just IT folks or MIS folks. These are people all around the business.
You need to seek them out, you need to reward them. They can be an excellent beta group, they could help you during concepts, proof of concepts or trials. If they’re really true experts, even if they are non-IT, you can have them lead training sessions. IT doesn’t need to do every single training. There’s some times where we take things very much for granted, and it might be better for a non-technical person to explain it. Then, making these power users part of your company culture, having monthly meetings with them, having them present, and having them be kind of a funnel, you can funnel information to your power users and then they can funnel it down to their departments. We have power users here in every single department of the business, and if I need an honest answer on something, if I’m second guessing myself or if I really need to know what’s going on on the ground right then, I have a whole bunch of trusted people that I can reach out to, and I really suggest that you develop those as well.
Create Comprehensive Documentation and Log Extensively
Thou shall document and log. Of course, as IT professionals, we love logging everything but we hate looking at logs. Your logs should be extensive, but you need to be very wary of alert fatigue, but I say, “When in doubt, log it and hold onto it.” Here are just some examples of the stuff that I log. I did a previous webinar talking about logging and alerting that’s online on the BetterCloud Monitor. You’re absolutely welcome to take a look at that as well. All of this goes back to the first commandment of just knowing your environment. Not all of these are created equal. You definitely need to prioritize what you’re logging and how long you’re retaining them, and of course to be very wary of alert fatigue.
If an alert fires off 10 times and it’s a false positive every single time, when it goes off the 11th time and there’s actually a problem, you’re probably not going to pay attention to it. You really need to look at all of this data, prioritize it, and have it proactively surface itself to you but only when it’s valuable. Now, I would love to compile master reporting lists with everyone on the webinar and everyone in the BetterIT community to see what else you’re reporting on, and also why you’re reporting on it. That’s something that we can talk about in the community after the webinar, but I would definitely love to hear from the community on what else you guys are logging and why. Oh, and of course, more stuff that we log.
Now, for documentation, every good IT department has a really good knowledge base, both an internal knowledge base for your employees, and an external knowledge base for the rest of the organization. Where do we even start? The hardest part is really even just getting started on it. Now, it’s going to take a lot of time, but you start by formalizing. Who’s the audience, how are you going to write it, where is it going to go? Standardize it by creating templates, and saving yourself that time, having a good unified format for everything. Go through every single service, make sure everything is there, and then you’re probably about halfway done because the hard part is actually maintaining it, actually staying up to date with it.
Even if a knowledge base isn’t updated in a month, there’s got to be at least 10 or 20 things that are out of date by then, and so training your IT team as they make changes, as updates happen, as policy changes, all of that, the first thing that they should do, they shouldn’t even have to think about it, is go in and update the knowledge base. For your end users, make sure that they see the knowledge base as a powerful tool, as something that they can look at maybe before the submit a ticket. Now, you can definitely buy a tool, but you don’t have to. It doesn’t matter as much the tool, it matters that the effort that you put into it.
I’ve seen 50 user organizations with really, really fancy knowledge bases and I’ve seen a 10,000 user organization that their knowledge base was just Google Docs and Google Sites. If it works, it works, but it works less because of the tool and more because of the time and the effort and the thought that you as an IT team put into it. It’s not a bad idea to kind of do CYA with documentation. Document everything that’s vital first, work your way down. Require that everyone on the team documents their most important processes, and make sure they’re documenting at least one new thing a week. With that, you can build out a really good knowledge base fairly quickly.
Value Your Network and Verify Your Backups
All right, number 10. Thy network be they rock, and they backup be thy savior. Well, what do we mean here? Basically, if you neglect these two things, you’re shooting yourself in the foot. You’re doing this absolutely at your own risk. With a SaaS-powered workplace, everything is just sitting out on the public internet, so your network is by far one of the most single, most valuable capital expenditures and investments that you can make. Having a backup, at least one backup WAN, having a failover scenario that you’ve actually tested to make sure that it works, because if your office goes completely offline, what’s your DR plan? You probably send everyone home.
I know at least myself, I’d be very embarrassed and wouldn’t want to have to do that, and so all of our offices have a primary and a secondary WAN connection with diverse pass and diverse providers, and they’ve saved my butt on quite a few occasions. Sometimes these backups are a really hard sell to make to executives and to management, and so you quantify how much it costs for every single hour that network is down. Just as an example, if you have 10 employees and you average it out that they’re getting paid $50 an hour, for every hour of downtime, just on payroll, you’re losing $500 an hour, let alone customers and image and everything else.
Even for a small office like that, if you can find even if it’s just a DSL circuit or a business class cable connection, if you’re spending $100 a month for backup internet and that saves you even one hour of downtime, it’s already paid for itself. Now, backups. If you ever think you’re ever going to need it again, back it up. Even if you don’t think you should back it up, you should back it up. There’s this old IT joke, “What’s my backup strategy? Three backups, two locations, and one bottle of whiskey for when it all goes wrong.” I actually had a recent story. I was working on some infrastructure for our data team in our data warehouse, and a software upgrade when completely wrong, blew everything away.
I was sitting there, thinking to myself that I just deleted about three man years of work. Blood, sweat, and tears went into all of this analytics. Now of course, I had a backup and I had a backup for that. Those backups had been tested, and so I knew the process to restore from them, restored them, and we were back up and running in less than an hour, but I think everyone can relate when you have that feeling in the pit of your stomach where something goes wrong and you’re thinking about quite possibly the worst fear as an IT professional, causing data loss to your end users.
Thoroughly Evaluate Your Vendors
One more bonus commandment. Thou shall thoroughly evaluate thy vendors. Now, this is even more important in a SaaS world because you are ceding some of the control of the operations of this service to the SaaS vendor. You should know what you’re getting into by establishing success criteria. You refine that, depending on the product, the department, and the needs, involve your power users, involve your management. Run pilots, test with your most technical user and your least technical user, your power users, and your regular users. Collect honest feedback before you purchase.
Then, one thing that I always do when I’m evaluating any sort of new product is I challenge their support. Even if I don’t have an issue or if it’s a really inconsequential issue, I’ll raise one. I’ll open a ticket or I’ll do live chat or I’ll call their support team, and I raise an issue just to see how it’s handled, to see the response time, to see the professionalism of the support team, and I’ve looked at products before where the support was a black flag that absolutely just caused us not to purchase. With a SaaS application, especially one of the core ones, you need to have 24/7 support that needs to answer in five or 10 minutes or less, and be knowledgeable and be able to fix it. While a lot of companies claim to be able to provide that, I would actually rather see them provide it in real life before I write the check, before I sign the PO.
Questions and Answers
Remote Worker Engagement
All right, let’s look at some questions. Let me start from the top. All right. “How do you ensure that your employees are making the most of the platforms that you offer, especially if they work remotely?” Well, first off it never hurts to actually ask them. Looking at usage data definitely really does help, and having conversations with the department heads and the managers about whether the tools that you’re providing are actually providing productivity or not I think are all really important, but without a doubt, it definitely is more difficult when they do work remotely. It’s much more difficult when you can’t walk over and stand over their desk and see what they’re doing.
Deprovisioning Tactics
On deprovisioning, “Any magic time saving tricks when it comes to shutting down user accounts across many services?” If you’re looking just at terminating access and not worrying about transferring and everything else, single sign-on definitely does make it really easy, but we do have BetterCloud that solves a lot of those challenges, but it’s something that we’re still working on, it’s still a pain point both internally and I think in the general market. We have some cool stuff coming up there that you guys should stay posted for. Colin McCarthy likes how Slack, you can provision everyone but you only get charged for active users.
Eliminating Costly Unused Licenses
A lot of other services don’t provide that, and Colin’s wondering how you can deal with overpaying for unused licenses and trying to get other vendors to adopt the subscription model. I mean first off, it doesn’t hurt to complain about it. I think a lot of the more traditional enterprise SaaS companies are going to take a long time to come along on that because for them, someone’s paying and not using the service, that’s just money in their pocket. I definitely love how Slack does that, but I think it’s definitely an uphill battle to get a lot of other vendors to do that, even though I agree, it’s an awesome idea.
Data Loss Prevention and SaaS Proliferation
One more from Colin, “How do you do effective DLP on your corporate data when it’s 101 different SaaS services?” Well, we have the core services covered and we both train and audit where data does end up. A lot of these little auxiliary niche services are not going to be holding financial data or customer data. You identify them for a single purpose, you train your users on that single purpose, and you make sure that they stick to that single purpose. Now, we have things like Salesforce and Google Drive covered with DLP and those are our systems of record where most of that data should live, and then in other services, whether it’s an automated or manual process, we do make sure that data is not leaking into those services, but we’re not as proactive as we could be with some of the core.
API Limitations with Free Services
Jeremy was wondering what time the pizza arrives. I actually had sushi for lunch, Jeremy, but pizza does sound great. All right, Jay Kim was wondering, “When a SaaS product doesn’t support an API, because you’re in the free tier, what are some other options to make changes to the account through coding?” Well, there’s always the really hacky approach of screen scraping, not that I’d really recommend it because whenever they do a redesign, your screen scraping breaks, but back in the day, when G Suite, back then Google Apps, didn’t have all of the APIs that I needed, I worked with a team that basically delivered some Selenium scripts, kind of a browser automation framework to do certain things, but very hacky, and kind of a last resort.
Unsanctioned Application Identification
Mike Lynch was wondering, “On that estimate of nearly one SaaS app per employee, how much of that was discovered and kept as a result of the shadow IT exploration?,” and for those that were not, what sort of process we had in place for a user or team to advocate for a new SaaS platform. You know, we’re small enough that we don’t really have a formalized process. We just have continuing discussions with all of the departments in the business, and we make sure that they’re free and comfortable to raise all of that.
One of the things that we did do to really help identify all of the shadow IT was sitting down with the finance team, looking at the personal expense reports, and seeing what sort of SaaS services we had on personal credit cards. That was a really easy way to target and then also using the app’s audit functionality in BetterCloud, we were able to look at every single app that had any sort of OAuth permissions to our G Suite domain, and tracked down the users there, figure out why they were installed and what they were doing. Do we have teams that advocate or use competing products? In certain cases, yes, but I generally put my foot down on that unless there is a very good reason. Sometimes you will have to do duplication. It’s kind of unavoidable, but I think it should be reserved only for very special cases.
BetterCloud Workflows
“Are all the offboarding tasks all automated through BetterCloud workflows?” Almost all of them, and almost everything else will be coming up in workflows. Outside of that, other tools or methods that we use, there is a checklist and a formal process that engages the security team and HR to make sure that all of the different aspects of the offboarding tasks are covered, and then the only other real tool is just having single sign-on, being able to revoke that access. One account for multiple apps definitely makes it really interesting.
Log Centralization
Mike Lynch was wondering, “Do you leverage anything to centralize your logs across SaaS apps?” Yes, we do. We use the ELK Stack that we host and run ourselves, that’s Elasticsearch, Logstash, and Kibana. We’ve written some connectors to take in things like syslog, netflow to suck in, logs that are stored in S3 buckets and Google buckets. We have an nginx proxy that can kind of format the logs, authorize them, and then send them to the ELK cluster.
That is our one single source for all of our logs. It’s been interesting building it out. It’s something that’s actually shared between my team and the security team, and it’s an incredible resource that we’ve just started leveraging, and I think is something that we’re going to really grow to in the future, but already we’re ingesting the logs of probably about 25 SaaS apps automatically, and then a couple manual imports. All right.
SaaS Adoption and Executive Buy-in
Nicole was wondering, “How do you get a leadership to engage in the idea of SaaS and tech in general? I’ve worked at large enterprises that use SharePoint 2007.” First off, Nicole, I’m sorry. I’m sorry about SharePoint in general. SharePoint was actually one of my first jobs.
You know, it is tough but I do feel like CEOs and CFOs are becoming more digitally aware. I think they’re starting to feel a little bit their feet being held to the fire and the idea that if their business isn’t transforming and adopting with all of this, their business is going to be obsolete. There are sells that you can make on efficiency, productivity, on reducing capital expenditures and transforming them into operational expenditures, and in general, just showing them really cool new tools that may excite them, but overall, I think it’s definitely worth challenging your leadership on it. Not every IT person is going to be lucky enough to have their CEO do a cloud first remit or anything like that, but I think with time, with pestering, and with a lot of effort, I think almost any leadership, even really old school leadership can come around.
You just need to show the benefits and be fairly non-technical about it. You sell it more in a business sense than a technical sense, you talk about the value, not just how cool the technology is. All right, scrolling through to see if we have any last questions.
Training End Users
All right, “Any advice on training?” Lunch and learns, try to meet regularly with the teams, but one of the challenges Jeremy faces is when software interfaces change. Absolutely, Jeremy. Something that we struggle with. First off, getting the IT team and maybe even your power users on early access or trusted tester will get them and will see those UI changes hopefully at least a couple weeks before they get rolled out to end users, and that’s the time to test them and to update the documentation, but not every one of your services is going to support that.
At times, sometimes it just is a mad scramble to update the documentation, to change the graphics and the instruction steps as Jeremy said. Especially for the smaller apps, they’re not as great about that, but as we said earlier, staying up to date with newsletters and communities and Twitter feeds and all of that definitely will help, but that’s one of those things that I feel like is a never ending battle.
Helpdesk to End User Ratio
Then finally, the last question we’ll take today from Jay Kim, “What’s the usual ratio for each team or each help desk person to regular users?” That’s a tough one. I mean, I hate to say it, but in many ways it kind of depends. What I would say is I’ve seen anywhere from about 50 users to one help desk employee, to about 500.
It depends on how technically literate your organization is and their employees, how efficient your help desk is, how many automated processes that you have in place. I think there’s probably a sweet spot somewhere in the 75 to 150, but without knowing specifically the actual area of business and the size and all of that, that is a real tough one. I wish I could give you a better answer on that, Jay Kim, but I would say somewhere between 50 to one, to 500 to one, all depending on in many ways that digital maturity of the organization.