ONBOARDING & OFFBOARDING AUTOMATION
Zero touch employee on and offboarding
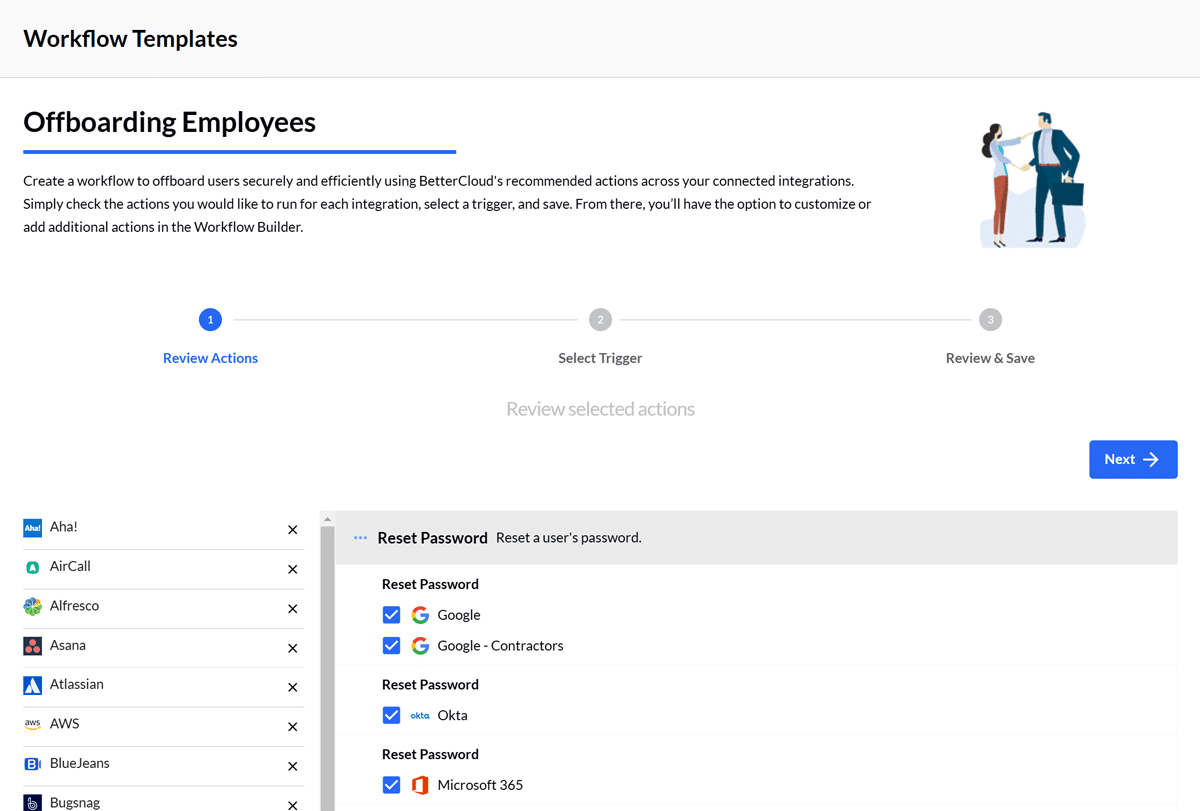
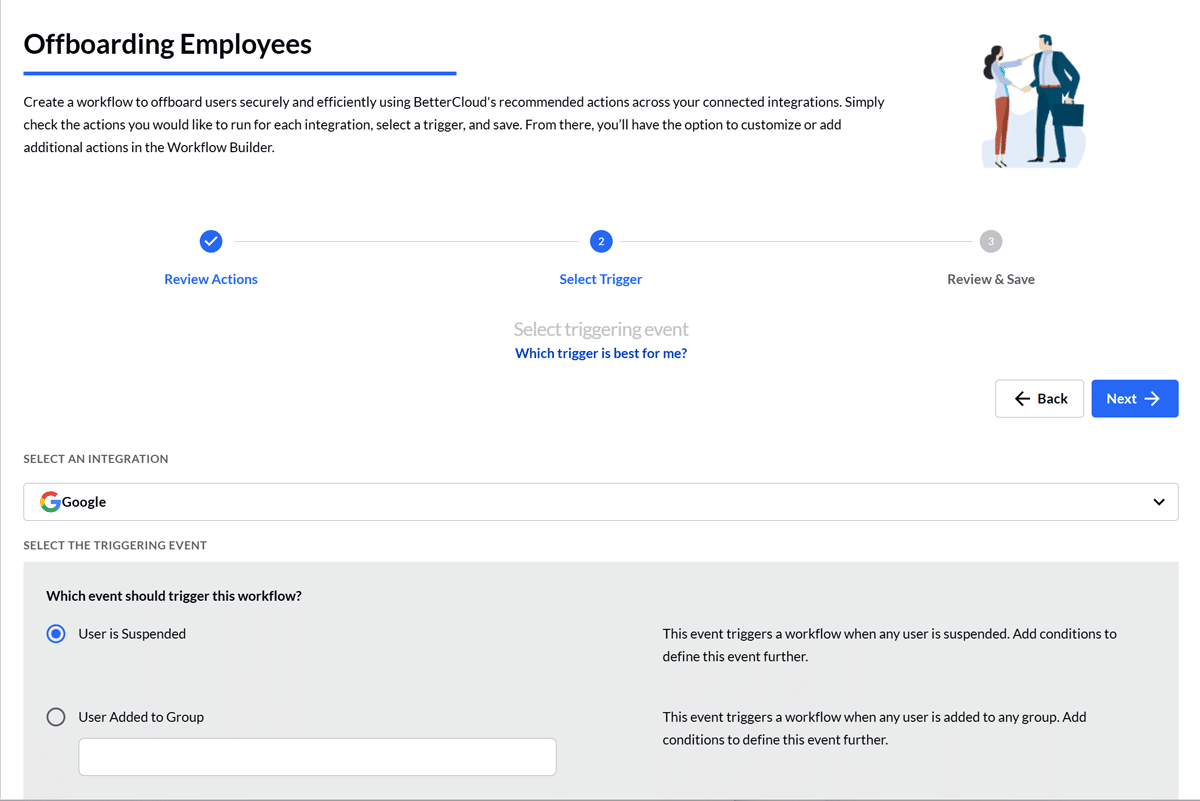
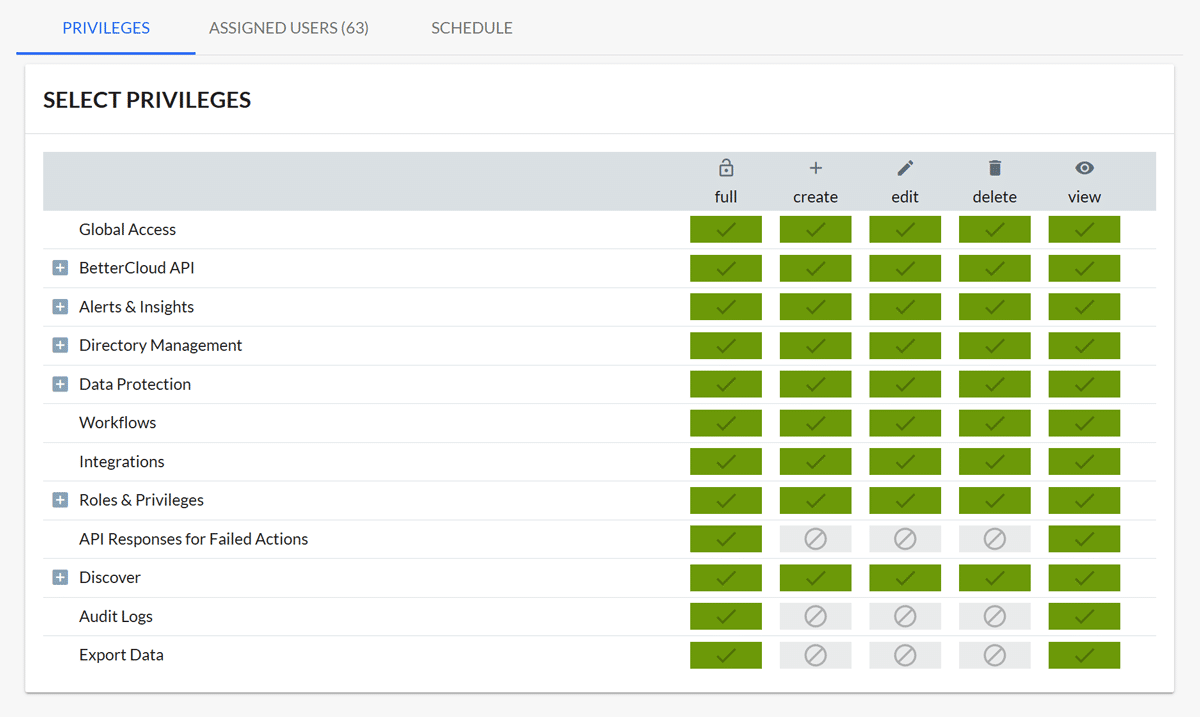
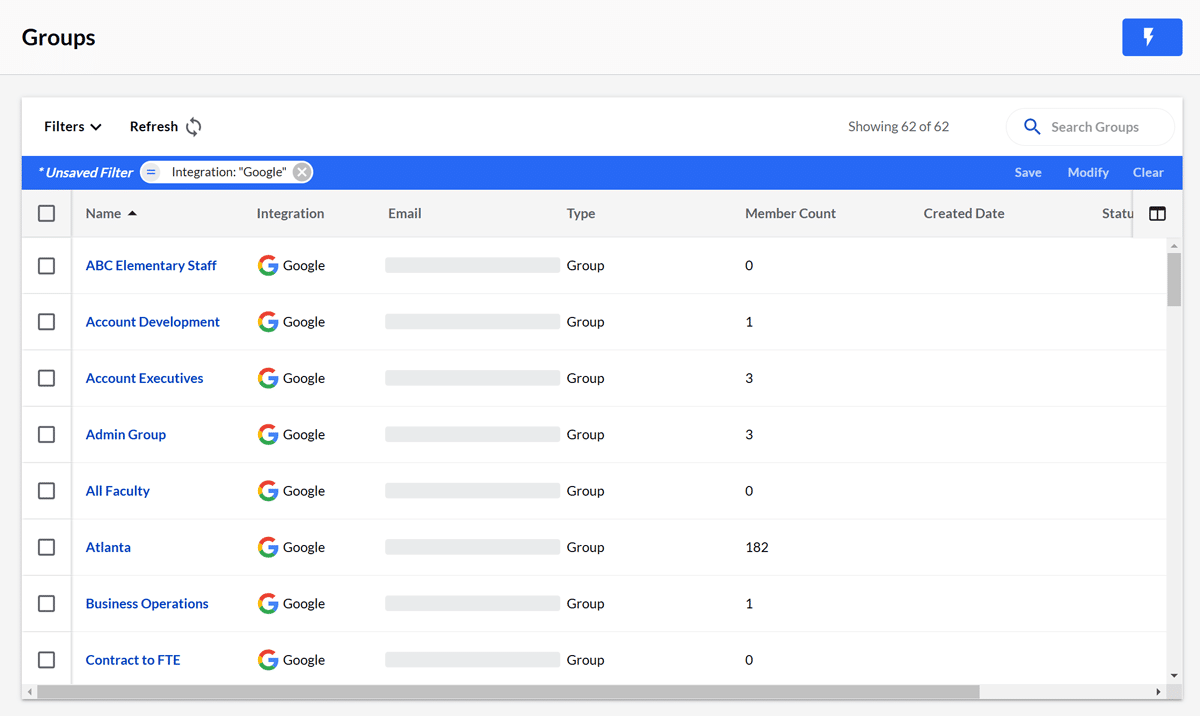
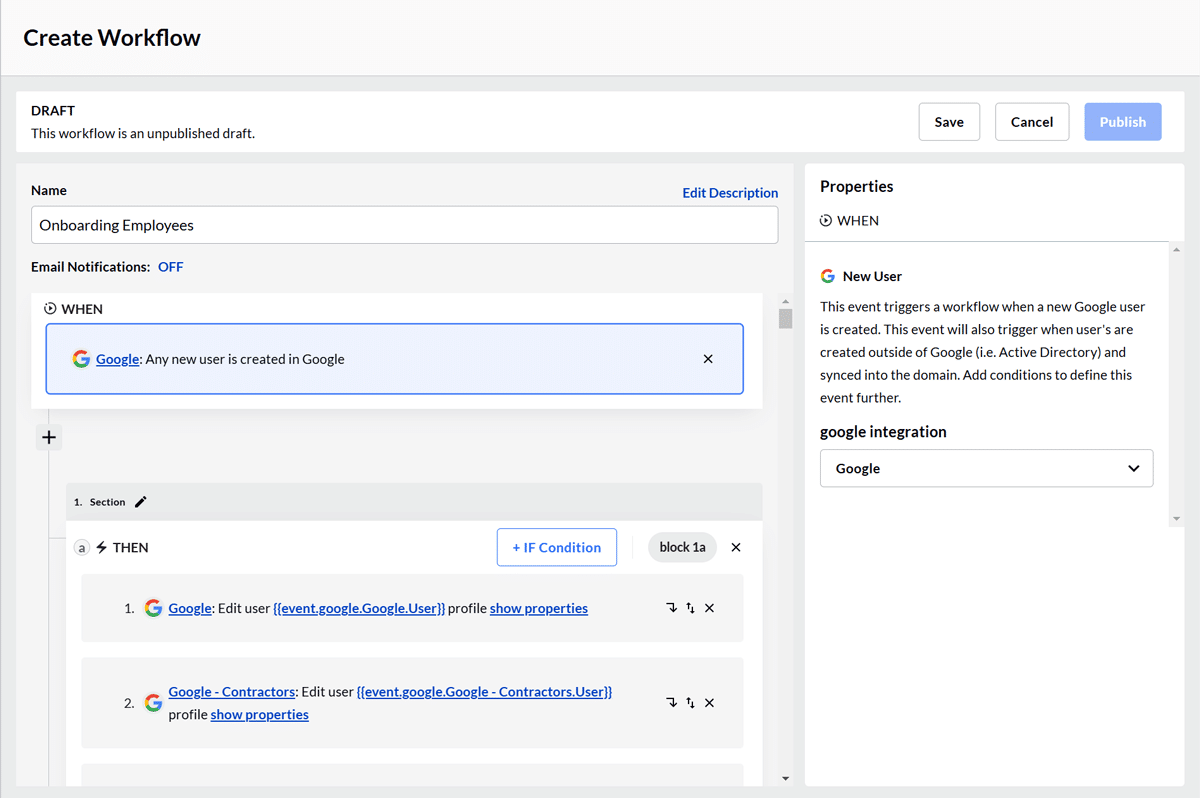
Never manually on or offboard an employee again. BetterCloud's Workflow builder automates routine user lifecycle management tasks with conditional operators and a library of pre-built actions and alerts. Reduce IT work, while creating great employee experiences.
“
Our offboarding is very streamlined. Previously, an IT member was dedicated to systematically removing access, whereas now you can rely on BetterCloud workflows to perform these tasks automatically. Overall, we've reduced IT's offboarding procedure by 70%"
— Monroe Smith, Automation Engineer at Sprout Social
Easy user lifecycle management
New hires will be ready to go on day 1 with the access and privileges they need to hit the ground running. HR will love you.

Green Dot Public Schools automates 10,000+ students onboarding and offboarding
BetterCloud handles the complexities of student and faculty onboarding, so Valencia and the Green Dot IT team can concentrate on more strategic projects.
See what else BetterCloud can do for you
IT teams chose BetterCloud: Leader in the G2 Spring 2026 Grid Reports
Recognized as a Leader in 30+ categories in the G2 Spring 2026 Grid Reports, including SaaS Management, SaaS Spend Management, and Data Loss Prevention, BetterCloud helps IT teams reduce manual work, strengthen security, and get more value from every SaaS app.