Why IT Needs a Framework to Help Navigate Uncharted Territory in the Age of SaaS
October 25, 2017
5 minute read

Below is an excerpt from our new book, Controlling Your SaaS Environment: A Six-Part Framework for Effectively Managing and Securing SaaS Applications. The framework addresses the main challenges SaaS creates for IT organizations and outlines ways to solve them, helping IT gain control and clarity over their SaaS environments. Get it here: https://www.controlyoursaas.com.
On a brisk fall day in October 2015, an administrator at a midsize company enabled an option in Slack.
The option was innocuous; all it did was allow Slack to automatically generate document previews when employees shared Google Drive documents and items in Slack. This was extremely common; many companies enabled this option for their Slack and Google Drive instances.
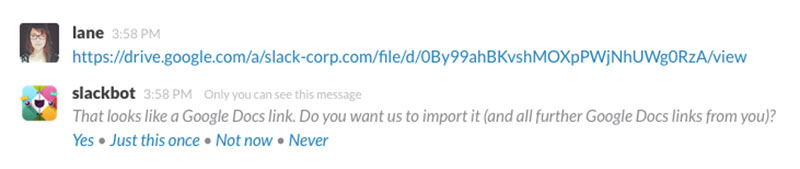
Example of the Slack/Google Drive integration
In March 2016—five months later—a supervisor discovered that this option was active.
By then, 100 employees had enabled this connection. And by then, senior security officers were alarmed.
Why?
Unbeknownst to the administrator, sharing links to Google Drive files in Slack also put those documents on Slack’s databases. In order for the previews to be created and made searchable, Slack automatically indexed and stored them for easy searching and reference purposes. By integrating the two applications with a single click, the administrator had exposed 100 Drive accounts and caused a potentially disastrous data breach. To make matters worse, this midsize organization was 18F, a prominent digital services team that is part of the General Services Administration (GSA).
As part of the federal government, they needed to exercise extra caution when connecting applications and securing sensitive data.
The inspector general’s office swiftly released a report about the data breach, stating that “Over one hundred GSA Google Drives were reportedly accessible by users both inside and outside of GSA during a five month period, potentially exposing sensitive content such as personally identifiable information and contractor proprietary information.”
Almost a year later, a follow-up report read: “As a result of our alert report, GSA has since confirmed that content containing personally identifiable information (PII) was exposed to unauthorized users as a result of this breach.” Jason Chaffetz (R-UT), House Oversight and Government Reform Committee Chairman at the time, called the incident “alarming.”
He released a statement lambasting the administrators, saying: “While we appreciate the efforts to recruit IT talent into the federal government, it appears these ‘experts’ need to learn a thing or two about protecting sensitive information.”
But in this era of SaaS, “learning a thing or two about protecting sensitive information” is not as easy as it sounds. The administrators should have been able to prevent this from happening, but they couldn’t.
The problem wasn’t that they were inordinately lax or inept. The problem is that IT is encountering new, unprecedented challenges with SaaS, and IT professionals lack the appropriate tools to solve those challenges.
Likewise, they also lack knowledge. They don’t know what operational security entails; how data spreads, overlaps, interacts; where it lives and where it’s exposed; how applications operate with each other. They do not have a framework that explains how to think about their SaaS environments—until now.
To learn more about the book, visit https://www.controlyoursaas.com.
A Framework for Thinking About the Runaway Train That Is SaaS
This story about 18F does not describe an isolated incident. It is happening everywhere.
As such, IT needs to get a firm grasp on the ins and outs of SaaS management and operational security. SaaS is a runaway train, a pure juggernaut in the cloud computing market. The largest public cloud market in 2017 will be SaaS, which is forecasted to reach $75.7 billion by 2020. SaaS adoption is on the rise—companies use 16 SaaS applications on average today, up 33% from 2016—and isn’t slowing anytime soon.
For almost every business unit or use case, there now exists a SaaS solution or vendor. While SaaS increases productivity, its rapid adoption also makes IT environments increasingly fragmented and unwieldy. As a result, the SaaS explosion is changing how IT professionals must think about SaaS going forward.
But what should that shift in thinking entail? That’s a bit murkier. In the absence of established, demonstrable best practices around SaaS management and operational security, IT is entering uncharted territory.
What’s missing currently is a structured, comprehensive way to think about managing enterprise SaaS software in order to keep up with a rapidly evolving workplace. There is no framework that outlines a modern-day approach to SaaS management nor are there guiding principles that help IT professionals achieve their security goals and requirements in SaaS environments. As environments shift from being homogeneous to heterogeneous, IT’s management and operational strategies must also shift accordingly. The shift to SaaS is driving a need for new frameworks and tools to manage, secure, and support mission-critical applications.
This framework—the first first of its kind—was created by synthesizing insights from interviews, surveys, and conversations with thousands of IT professionals over the last three years.
These IT practitioners have varying tenure and hail from a wide range of industries, geographical locations, and organization sizes, but they have one quality in common: all are directly involved in core IT management and operational security.
What emerged was a clear, consistent portrait. These IT practitioners all spoke of nascent challenges around SaaS management and security that they are encountering unilaterally as their organizations adopt SaaS applications.
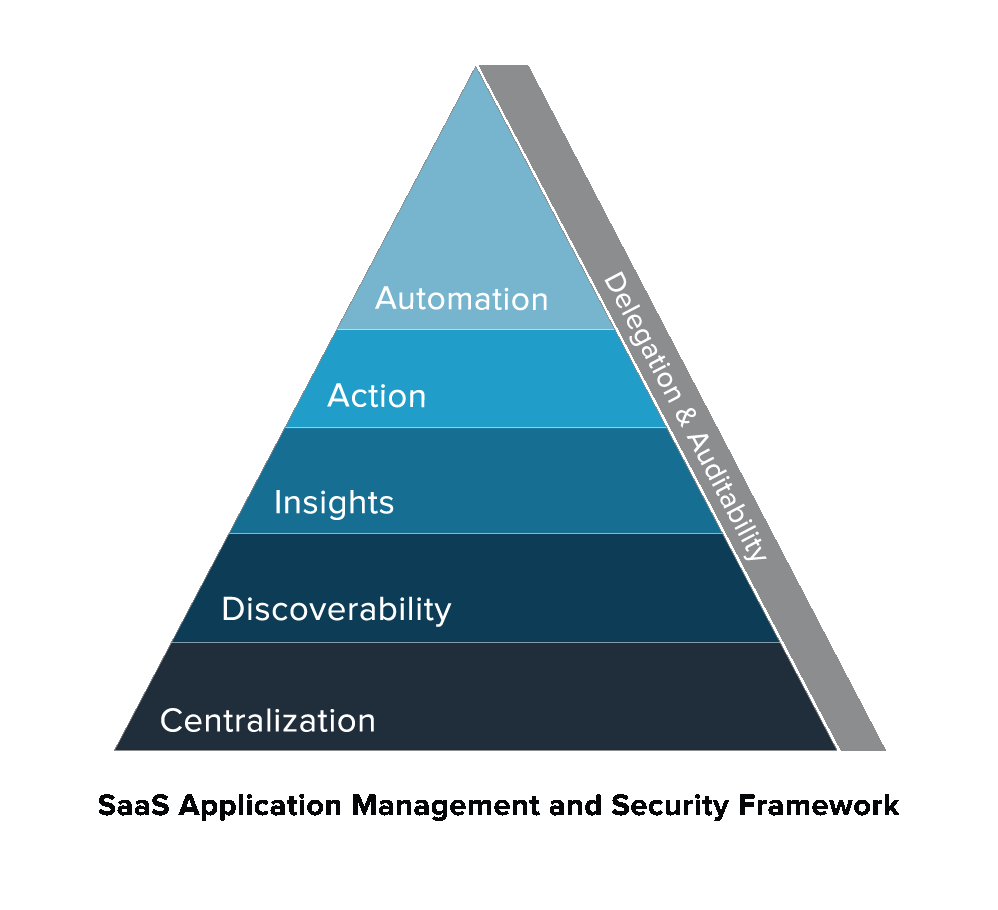
The SaaS Application Management and Security Framework will address those challenges at length, as well as the strategic elements IT needs to solve them. It will also describe the costs and risks of operating outside the framework. More broadly, it teaches IT professionals how to think about the way data interacts, whether it’s in a single SaaS, multi-instance, or multi-SaaS environment. These concepts are equally relevant to IT professionals who manage one SaaS application or dozens.
Visualized above, the framework illustrates how IT professionals should think about engaging with their SaaS applications. It operates on the assumption that IT is treating SaaS platforms as the systems of record for its company’s data, either in one or two areas of the business or across the entire business. Each element builds upon the previous one and each is key to managing, securing, and supporting a SaaS environment. Collectively, the elements in this framework form a playbook on operational security and management in the SaaS era.
By reading Controlling Your SaaS Environment, you will:
▲ Understand the key challenges faced by modern IT professionals, and why the status quo for SaaS application management and security cannot continue
▲ Learn best practices for IT on managing, securing, and supporting modern workplace technology
▲ Envision what an “enlightened” state for IT would look like when the framework is fully executed
▲ Connect the framework to real-life news stories and data that illustrate the potential risks and costs of failing to manage and secure SaaS applications more holistically
▲ Visualize how all six elements of the framework build upon each other to create a high-performing IT environment
▲ Explore the range of solutions for executing the framework, including different vendors’ advantages, disadvantages, and functionalities
Stay tuned for the next post in this series, where we’ll dive into the first element of the framework, Centralization.
To learn more about the book, visit https://www.controlyoursaas.com.