Blind spots in Dropbox: 5 things you didn’t know your end users & admins could do
February 14, 2025
6 minute read

Dropbox is a beloved cloud storage platform and for good reason. Enabling better employee productivity and more efficient collaboration, Dropbox undoubtedly boasts massive business benefits. However, the very act of sharing documents digitally opens doors to security threats, making it crucial to understand their nature and origins.
One of the most important security issues to be aware of is sensitive data exposure. In a recent study that analyzed 63 million documents stored within cloud apps, researchers found that some 23 percent of the documents analyzed were shared publicly, allowing anybody with a link to access them. Additionally, 1 in 10 broadly shared files in cloud apps exposed sensitive and regulated data.
In fact, Dropbox even patched a vulnerability back in 2014 for all shared links after some users’ sensitive documents (including tax returns and bank records) ended up on Google.
Therein lies that fundamental trade-off: productivity vs. security. SaaS apps like Dropbox give users plenty of flexibility to collaborate with others, but this kind of freedom can also create security issues unbeknownst to IT. Knowing about the biggest blind spots can minimize security risk and exposure. Here are five things you should be aware of:
1. End users can create public links to files
End users can easily create public links to files in Dropbox. This means anyone with the link can view the file.
Unless a user clicks on “Link settings” and specifies otherwise, anyone with the link can view it, comment, and download the file indefinitely (i.e., without an expiration date).
While this feature can be helpful for collaboration (e.g., sending files to clients who don’t have a Dropbox account), it also creates a risk for data exposure.
This is a blind spot for IT. If an end user creates a link to a file that contains sensitive or confidential information, then that data is accessible by anyone with the link—and IT might not be aware of it.
2. End users can create public links to entire folders
Similarly, end users can easily create public links to entire folders in Dropbox. This means anyone with the link can view all the contents of the folder.
In just a few clicks, a user can create a public link to a folder:
When you copy and paste the link into a new Incognito window, here’s what it looks like:
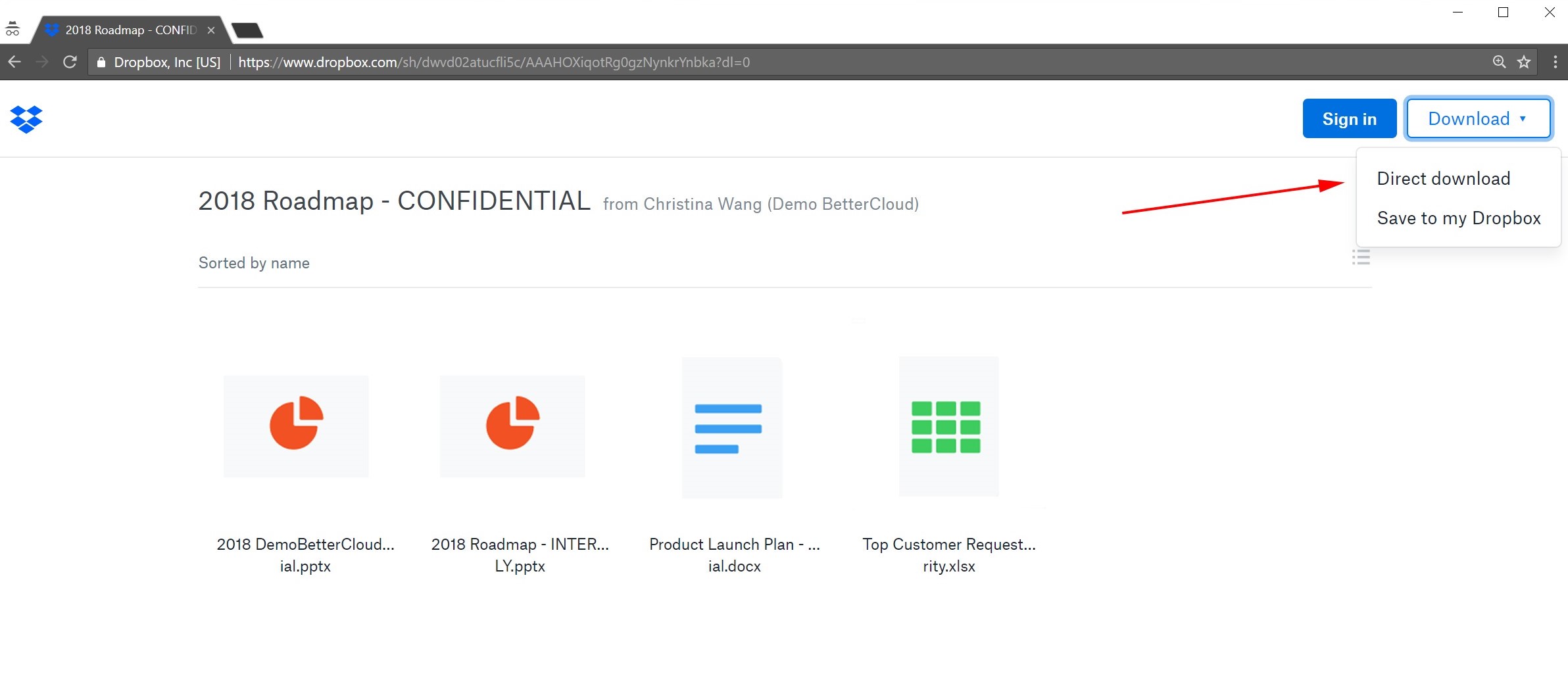
Everything inside the folder is there, publicly, along with the user’s full name and organization they belong to. Anyone can open the files and download them (either directly or by saving it to their Dropbox). As you can see from the “Sign in” button, you do not need to be signed into a Dropbox account to access the files.
This feature adds an additional layer of risk to what we discussed in the first blind spot. Now it’s not just one single file being shared with a public link—it’s an entire folder and all of its contents exposed publicly. The magnitude of risk increases.
And just like the example in the first blind spot, unless a user clicks on “Link settings” and specifies otherwise, anyone with the link can view it, comment, and download the files indefinitely (i.e., without an expiration date).
3. Admins can sign in as any user, allowing them to see and download the user’s files
Note: This sign in feature is only available to Dropbox Business teams on an Advanced or Enterprise plan.
Dropbox team admins can sign in to the account of anyone on their team. As Dropbox explains on their website, admins can do this to:
- Organize a new employee’s Dropbox account before they start
- Troubleshoot issues
- Keep a project moving while team members are away from the office
This type of access can be helpful to facilitate onboarding and streamline work. But there are security implications that you should be aware of. By signing into a user’s account, admins have access to all of their files. They can view, access, share, and download any of them.
Here’s an example of how an admin can sign in as a user and view their files:
This becomes a security concern if the user has confidential information, such as sensitive HR or financial files, stored in their Dropbox account.
In general, it’s a security best practice to follow the principle of least privilege and keep the number of super admins to a minimum. And since organizations often have more admins than they think they do, it’s wise to (at the very least) know what your admins can do and see. Do you want all of your admins to be able to view all of your users’ files?
4. Admins can control the default sharing settings for the entire company
Dropbox team admins have the ability to set limits on how widely company files can be shared:
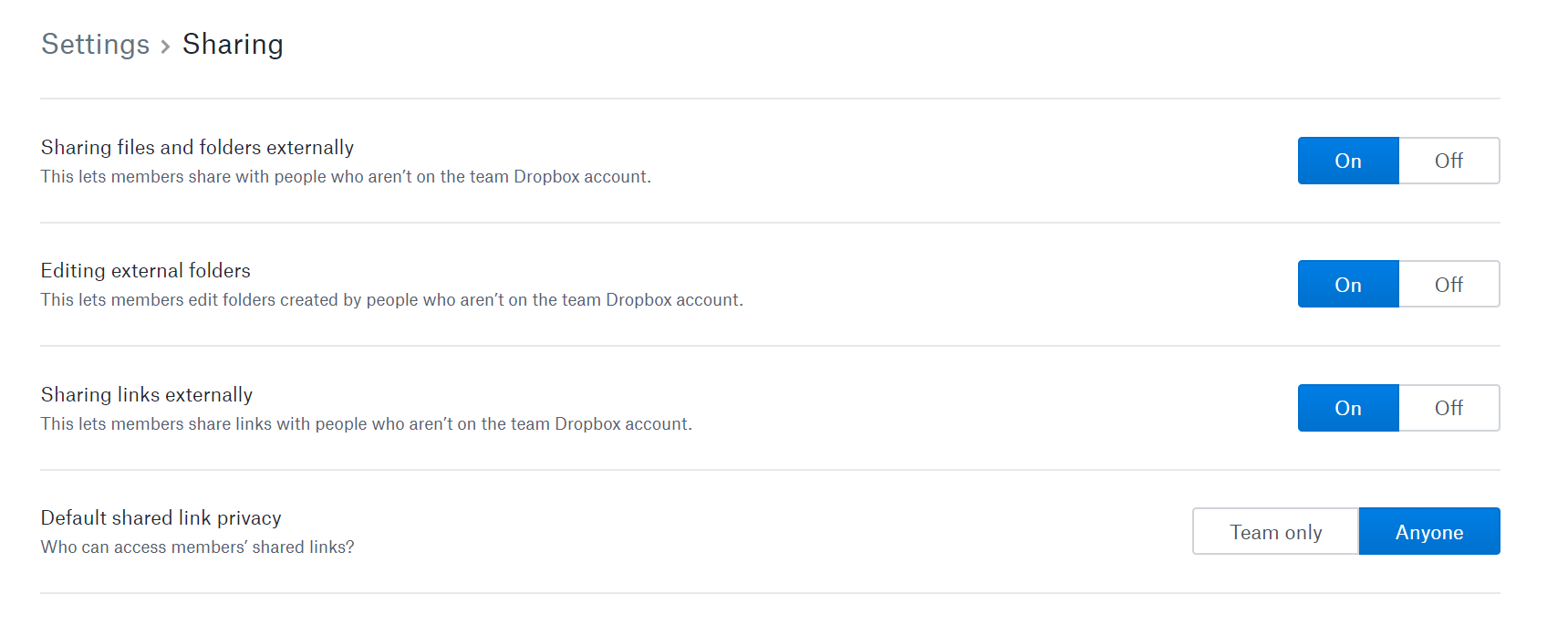
These settings allow users to share files, folders, and links externally (i.e., with people outside your Dropbox team). But the last setting, default shared link privacy, is particularly important. This means: By default, who can access shared links created by users? Can only people on your Dropbox team access them, or can anyone access them? That’s a big difference.
Any admin can, with a quick toggle, change these default settings org-wide—potentially giving end users way more freedom than intended. It’s easy to change these settings by accident (or do so without fully understanding the implications).
When it comes to data security, it’s a good idea to at least be aware that your admins can change all these sharing settings. Are you comfortable allowing all your current admins to have the power to change sharing settings org wide?
5. If users take actions that are potentially risky, there are no alerts to notify you of this behavior
To some extent, Dropbox’s native admin console does provide visibility into user activity. They explain on their website: “As an admin, you can monitor who’s sharing, who’s logging in, and more. You can quickly glance at the activity log, create full reports for specific time ranges, or even pull reports on a specific member’s activity.”
This is a solid start. However, it’s only part of the battle for visibility. Yes, IT admins can see many types of actions, but the onus is on them to proactively monitor their users’ activity, filter by specific criteria, create reports, etc. You essentially have to know what you’re looking for (or spend a lot of time browsing aimlessly).
Thus, IT is still left with a blind spot. How do you know if something risky happens? In the native admin console, there’s no way to receive alerts or notifications for risky user behavior. For example, if a user shares a confidential folder with a public link, how would you know right away? Unless you’re monitoring user behavior regularly, it might take you days, weeks, or even months to discover this action in the activity log.
Ultimately, you can’t fix what you don’t know is wrong. Being aware of everything users and admins can do and see in Dropbox is the first step to eliminating blind spots. Armed with awareness, you can start gaining visibility and control over your SaaS environment.
BetterCloud eliminates Dropbox blindspots
While Dropbox facilitates seamless collaboration, its inherent flexibility can inadvertently expose sensitive data. To effectively mitigate these risks and eliminate the identified blind spots, consider integrating a comprehensive SaaS management platform like BetterCloud.
By providing granular visibility, automated security policies, and real-time alerts, BetterCloud empowers IT teams to proactively manage Dropbox, ensuring that sensitive data remains protected without hindering user productivity.
With BetterCloud, you can gain control over sharing permissions, monitor user activity, and receive immediate notifications of potentially risky behavior, transforming Dropbox from a potential security liability into a secure and efficient collaboration tool.
Book a demo to see how BetterCloud can help your Dropbox instance be more secure.



