Security without Administrative Controls is Only Half the Solution
October 23, 2014
4 minute read

Kyle Quinn is Senior Product Evangelist at BetterCloud.
As more and more company data is moved to the cloud, IT professionals and executives maintain a strong focus on security. And, when speaking more specifically about Google Apps, the area of concern usually centers on Google Drive and how organizations should and can control information stored in and shared via the cloud collaboration tool. In fact, many products have cropped up to assuage these fears, like BetterCloud for Google Apps solution.
But, while IT security professionals are certainly taking the right actions to protect data stored in the cloud, they’re also missing other areas of the Google Apps suite that need added security.
Organizational Units
Many companies correctly use Organizational Units to segment permissions granted in Google Apps. For instance, your company might put more strict controls on your HR department than your Marketing group. By creating various OUs for different departments, IT administrators are able to easily apply distinct security policies to users based on their job roles.
However, in most enterprises it’s not uncommon for users to transition between departments. Employee movement from one company department to another can have grave security consequences if the user is not reassigned to their new Organizational Unit.
To ensure users are reassigned after moving departments, put a checklist in place for IT professionals to follow. This checklist should include reviewing a user’s group memberships, third-party applications, Drive policies and Google+ policies.
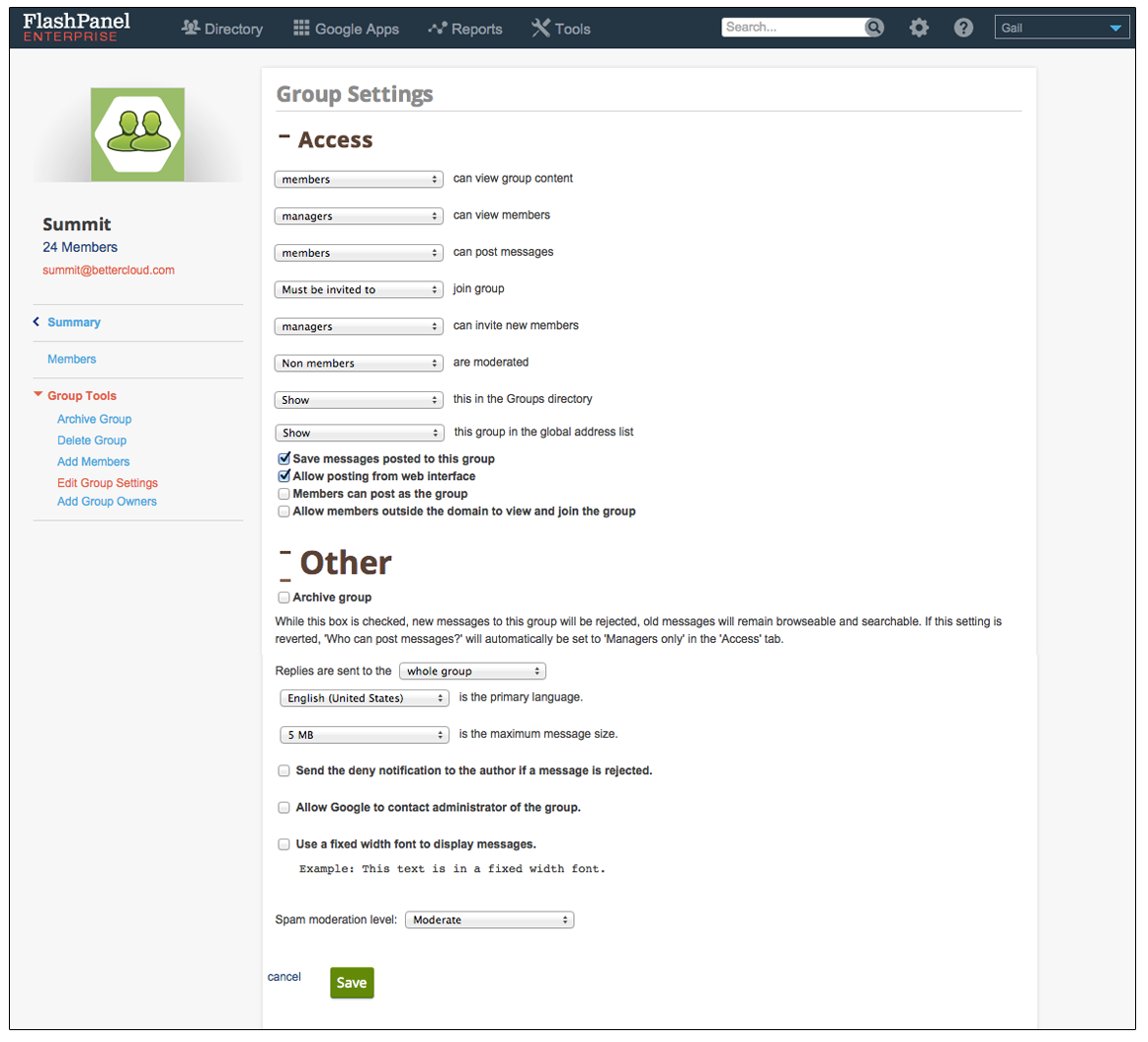
Google Groups
Google Groups is a great team collaboration tool for both internal and external use. However, several Groups administration settings may allow data to either escape beyond the confines of your company walls or allow data to be stored beyond an acceptable retention period.
Properly managing these settings, including moderation, access and group permissions, across all Groups in your organization is a huge step forward when securing your Google Apps environment. While these settings are vital, configuring them for potentially dozens or even hundreds of Groups within your domain can be time consuming. Using a third-party solution like BetterCloud allows IT professionals to standardize Groups settings in bulk, saving countless time and systematizing a potentially troublesome area.
Google Groups also create an administrative headache since Group owners have the ability to adjust and change Group settings at will. This level of control could lead to additional risk since owners may not be fully aware the impact changing Group settings has on the organization’s overall security.
To prevent Group owners from changing settings at will, your company should establish a process to monitor Group settings throughout the year – in fact this should be a key component of your organization’s security plan. Better still is to allow only certain administrators to create Groups. This may create more work for your IT in the short term, but will keep things secure and up to company standards in the long run.
Deprovisioning Users
When an employee leaves an organization, most companies look to leverage tools available in the Google Admin Console. The process of deprovisioning users via the Admin Console allows IT admins to lock a user out of their account and transfer ownership of their Google Docs to an authorized user. While these steps are important, they’re only part of the security puzzle.
For instance, the departing users may have enabled certain mobile apps, browser extensions and other Chrome Web Store and Google Apps Marketplace products during his or her tenure at the company. While deprovisioning the user in the Admin Console locks the account, these third-party products are still accessing portions of the deprovisioned user’s Google Apps account. It is therefore paramount to ensure these third-party apps are blocked from accessing Apps data. As part of a deprovisioning workflow in BetterCloud, administrators can blacklist or sever ties with third-party applications authorized by the user by invalidating the products’ OAuth tokens. (For more, see the below section on third-party apps).
There is also potential for data exposure through other Google services, including Sites and Calendars that need to be addressed and secured as a user exits an organization. Again, BetterCloud can provide an organization with a robust deprovisioning workflow to ensure data access is terminated completely across the Google Apps domain.
Third-Party Applications
As mentioned above, users have the ability to install many third-party applications at will. While these products provide users with a wide array of functionality, giving users access to install these solutions can cause immense headaches for the IT security team.
The prevalence and access gained by third-party apps is only growing – and now end-users can even install Google Apps Marketplace applications. With every new application installed, the threat of data leakage grows. It’s therefore imperative that your organization put in place the proper monitoring tools to not only see what apps users have installed, but to also understand the type of access those applications have to data on your Google Apps domain.
Email Forwarding
Another area of concern lies around email forwarding. While there are certainly legitimate reasons why an employee would forward their email (like if they’re on vacation), you should be wary of any employees forwarding work email to a personal address.
Leveraging BetterCloud can allow the IT team to report on and address instances of unsanctioned email forwarding.
Final Thoughts
As companies move to Google Apps they must review and determine if their administrative policies are indeed suitable for life in the cloud. As these policies are reviewed and updated, companies should also take into account that third-party tools may be required to maintain these new processes. Once both processes and tools are in place, IT professionals will be able to properly implement, report on and monitor security across the entire Google Apps suite.