5 Takeaways from “Securing G Suite and Beyond: Tales from the Trenches” (Google Cloud Next '18)
July 30, 2018
5 minute read
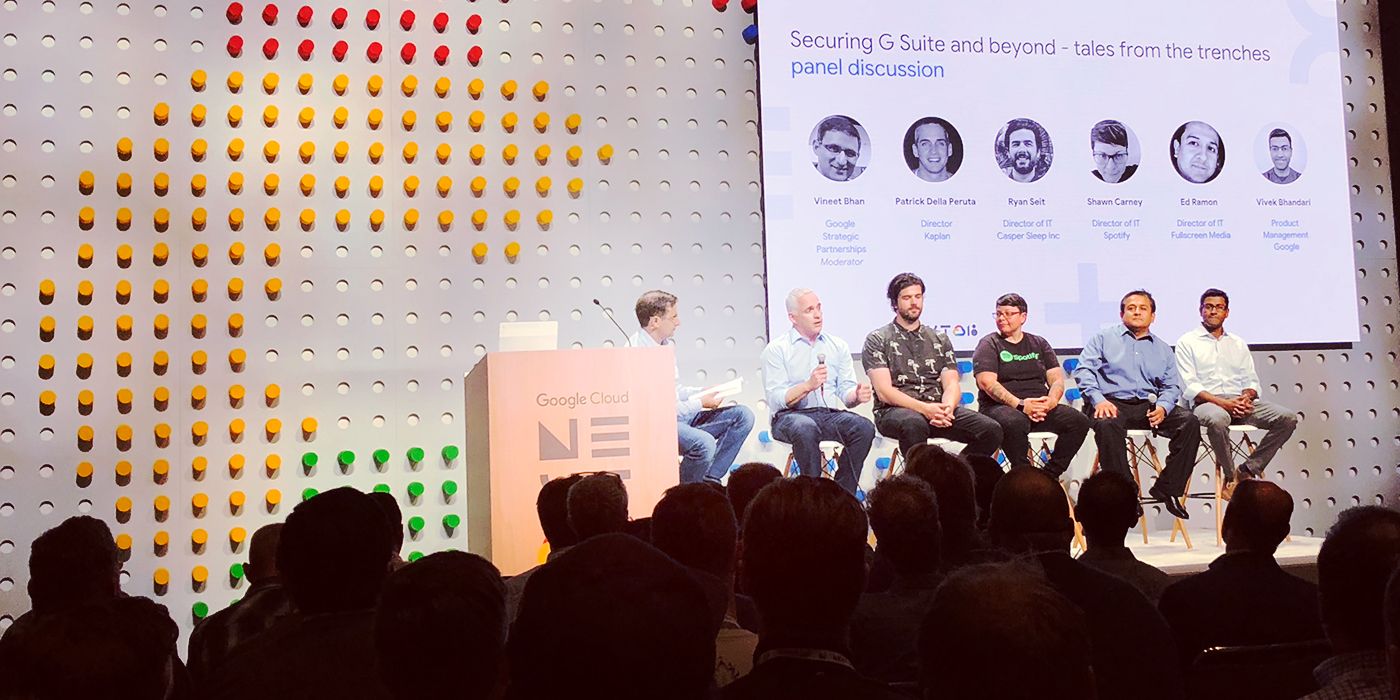
Well, Google Cloud Next ‘18 is a wrap! If you missed it last week, here are some highlights from a panel called “Securing G Suite and Beyond: Tales from the Trenches” that we thought would be particularly relevant to our audience.
The panel featured four BetterCloud customers (Patrick Della Peruta, Director of Enterprise Collaboration at Kaplan; Ryan Seit, Director of IT at Casper; Shawn Carney, Director of IT at Spotify; and Ed Ramon, Director of Information Technology at Fullscreen Media). It explored security topics that are top of mind right now for many modern IT professionals: How have security needs evolved, and what are the biggest concerns moving forward? What important lessons have people learned?
Here are five key takeaways, along with some tips and best practices the panelists shared.
1. IT must find that “happy balance” — secure the environment, but also let users have flexibility.

(We’ve cued up the clip for you – time code: 09:01)
When asked, “What are your security requirements and concerns?”, many of the panelists brought up data security.
“A lot of the out-of-the-box security settings around collaboration and sharing data just don’t work for us, and we need to be able to get in there and really think how do we want to share data, with whom, and why and when?” says Carney.
And a big part of data security is striking the right balance. This was a common theme that both Carney and Seit touched on: IT must secure the org, but it can’t do so in a disruptive, rigid way.
Carney noted that as attacks become more sophisticated, a lot of the efforts they make to block those attack vectors result in decreased productivity for employees.
“So the real challenge moving forward is how we become more secure and at the same time become more flexible to allow everyone to be more productive — and really rethinking that,” says Carney. “It’s more about thoughtfully deciding where our riskiest areas are and focusing on plugging those security holes.
“And by building these secure paths of least resistance for our employees, what we do is enable buy-in for them in the risky areas that we care about.”
Seit echoed that sentiment. With lots of workers in multiple offices using multiple devices, you need to have security measures in place to identify the type of device, the location of the device, and the user who’s logged in. The alternative is “just completely locking it down altogether, which is not the approach we want to take,” he says.
Rather, the approach is more about “enabling the user to use the device that they want, but get the security that we need, a) so I can sleep at night, but also b) so we’re not worried about an attack or a breach.”
2. “There’s a lot of love for BetterCloud. That’s very clear.”

(We’ve cued up the clip for you – time code: 22:13)
One of the topics the panelists addressed was the role of third-party products. The four panelists — all BetterCloud customers — brought up BetterCloud and the benefits they’ve experienced:
- Reduction in offboarding time (from 35 minutes per person to a few seconds). Ramon’s team has used BetterCloud to automate their offboarding process, and they’re working on “putting more love” into their onboarding process.
“What I’ve really realized with BetterCloud is: The more you give it, the more you’re going to get out of it. And it’s a great tool.”
- Productivity gains from BetterCloud’s teams and the product itself. “The customer service, the technical support, the [expert advisory] teams who come and actually help us build these automated workflows — that’s huge! It’s like having another team helping us. And then the tool itself helps automate away the processes that my teams were stuck doing for a very long time,” Carney says. “It’s brought productivity into my teams as well as productivity to our employees.”
- Improved working relationships with other departments. Seit admits he initially wanted to use BetterCloud to only manage his G Suite groups and create users. “Once I started digging into it, it’s one of those things where there are so many features, you probably need a BetterCloud person to really know everything about the product. There are a ton of features, which is fantastic,” he says. BetterCloud has reduced the amount of time his team takes to onboard, offboard, and manage user lifecycle changes. But it’s also allowed them to communicate critical lifecycle changes across departments very quickly so that everyone knows what’s going on.
“[The BetterCloud workflow] notifies the managers, HR, legal, finance, everybody basically. It’s just made our interactions and our working relationships with those teams so much better,” says Seit.
3. As security evolves over the next few years, here are the challenges IT should be thinking about.

(We’ve cued up the clip for you – time code: 29:30)
The panelists were asked, “Where do you see security evolving in the next couple of years? What will be the needs, and what should people think about?”
Here’s what’s on their minds:
- Security keys. Last week, Google announced that not one of their 85,000+ employees had been phished since 2017, thanks to the use of physical security keys. “That’s something I’m going to go back to my management team [about],” said Della Peruta. “We are very focused on phishing, we do phishing campaigns quarterly, but the end user’s always the weakest link. Looking at security keys is big for us going forward.”
- Getting control over tools that users want to use. Seit says that given the amount of services out there that users want to use, adding tools seamlessly into your IT infrastructure will be a challenge. “Conversely, making sure those security features and functions are in place — but also as unnoticeable or transparent to the user as possible — is going to be key,” he says.
- Being more secure and more flexible at the same time. “How do we become less prescriptive about just blocking everything?” says Carney.
“How do we become smarter about blocking the things that actually matter, and enabling people with these paths of least resistance that you want them to take?” she says.
- Adopting governance. “The biggest tip I would say is adopt some type of governance. I’m a big fan of ISO 27001. Why reinvent the wheel? Just follow the shadows of giants,” says Ramon.
4. Trends like AI and machine learning will continue to influence the direction G Suite takes.

(We’ve cued up the clip for you – time code: 34:55)
According to Vivek Bhandari, a product manager on the G Suite team, Google wants to continue to leverage AI and machine learning to combat the evolving threat landscape. Though MDM has existed for a while, he says today nine out of 10 devices are unmanaged, and one in four devices do not have passcodes. Google wants to make things simpler for IT admins by investing in automation. “Automation will be key,” he says.
5. The most important lessons learned? Overcommunicate. Explain the “why.” Follow the principle of least privilege. Know your metrics.

(We’ve cued up the clip for you – time code: 37:35)
All four panelists shared fantastic advice, tips, and lessons learned:
- Overcommunication is key. Both Ramon and Seit mentioned this as critical lessons. “When you think you’ve communicated too much, continue making sure you communicate even more. Don’t be scared. People will appreciate that more than be upset by it,” says Seit.
- Explain the why. “People tend to follow behaviors when they understand why it’s important. That’s when you get people engaged and motivated,” says Carney.
- Have an incident response plan. This is “100% critical,” says Seit. He recommends creating incident response plans outlining potential issues you could run into, who’s owning what at each time, and creating email templates ahead of time that will go out to users, leadership, etc.
- Think about the principle of least privilege. “People shouldn’t have access to any more than they absolutely require for 90% of their day,” said Carney.
- Understand your metrics. According to Seit, you want to understand questions like: How many tickets are you fielding? Who’s taking care of those tickets? What kind of tickets are they? What’s the priority level? What’s the CSAT score? All that information helps improve your team, but it also helps leadership get deeper insight into IT’s achievements and value. “Always look out for yourself. You’re your own best advocate. You are the PR team for IT, so make sure you’re communicating that out,” he says.