We Let 300 IT Professionals Ask Our Cloud Security Expert Any Question They Wanted, These Were the Best
October 21, 2016
6 minute read

Before we jump into the security Q&A, we have an exciting announcement to make. In our continued efforts to provide you with the best IT resources possible, we are excited to announce our latest endeavor: a brand-new Slack community called BetterIT.
BetterIT is a Slack community exclusively for leading IT professionals who are creating SaaS-powered workplaces all around the world.
We wanted to create a place where our audience (of more than a thousand IT professionals) could connect during our online event, Cloud IT Live (which kicks off today!).
But why limit the community Cloud IT Live? Why not create an active community of like-minded and forward-thinking IT professionals? Why not give IT professionals a place to continually share ideas, discuss best practices, and talk about the solutions they use every day?
For the past few weeks, we’ve slowly invited IT professionals from leading organizations around the world. As of this writing, there are already around 350 of the brightest minds in IT in the community.
You can join and contribute to the conversation today by visiting: bettercloud.com/slack-community. You do not need a Slack license to join. It’s totally free.
The First-Ever BetterIT Slack AMA
On Oct. 15th, we hosted the community’s first-ever AMA (Ask Me Anything) with our Sr. Application Security Engineer Austin Whipple. Austin has an expertise in social engineering, application security, phishing, and penetration testing. Prior to joining BetterCloud, Austin worked as a security consultant at Bishop Fox, a leading IT security consulting firm.
Below are some of the highlights of the AMA, edited for clarity.
Q: What are the go-to steps admins should do when evaluating and introducing new cloud apps to a company?
Austin Whipple: Here are the questions you need to answer: How much will company data be exposed? Have they had a security assessment/penetration test within the last year from a respected firm? How transparent/easy is the onboarding process for the domain? Do they allow OAuth or does everyone need to manage a separate password?
Q: What is the most common (and easy-to-fix) security mistake that people often overlook?
Austin Whipple: Don’t trust (and echo) user input in websites, and don’t take code off of the internet and plug it in without checking for introduced vulnerabilities.
Q: What is your approach for balancing security with freedom, and where are you willing to make compromises for convenience?
Austin Whipple: I try and make security as transparent as possible, and non-intrusive where possible, but I am unafraid to throw down and make certain things hard requirements if there’s no way around it. A good example is our rollout of using LastPass.
Provide a product that can solve a pain problem, and start rolling it out just requiring them to sign up and enable two-factor, but then later on we incentivized them putting passwords into LastPass and showing us their challenge score to receive cookies (or donuts). When necessary, we’ve gone to the top and gotten hard requirements on things where we felt people wouldn’t make the smart choice for themselves. There have been times when I’ve eased up off due to seeing how difficult it would be to implement.
Q: What are your favorite security-related websites?
Austin Whipple: https://reddit.com/r/netsec, wechall.net, http://carnal0wnage.attackresearch.com/, https://www.trustedsec.com, https://room362.com, https://www.christophertruncer.com, and irongeek.com to name a few.
Q: Have you attended DEFCON and would you recommend attending?
Austin Whipple: Many times, and no. Pick a smaller conference. DEFCON is too big and too watered down. Go to DerbyCon or a more local bsides or CactusCon.
Q: What things are you exposed to at the smaller cons that you aren’t exposed to at DEFCON?
Austin Whipple: You get the ability to get into the talk you want to see. Also, after-talk chats with big stars in the security industry. You’re not really competing for attention and you can actually sit down with them and discuss their work in greater detail. Better networking, less counter-culture (not that there’s anything wrong with counter-culture, it just happens at the expense of quality at DEFCON)
Q: What is the most important thing IT professionals need to know about phishing?
Austin Whipple: Not to spread FUD (fear, uncertainty, doubt), but that it is going to/already happening to individuals in your organization. This is a pretty good watch if you haven’t already seen it. Also, there’s a good BetterCloud Monitor article about how to get started with prevention.
Note: BetterCloud Director of IT Tim Burke’s post on SPF, DKIM, and DMARC is relevant as well.
Q: What were the most common weaknesses when you pen-tested organizations at Bishop Fox?
Austin Whipple: They are lined up pretty much exactly with this owasp list. I saw XSS more than any others and next was authorization bypass. I think SQLi and other forms of injection are higher because they often had greater impact.
Q: Any views on using “-“ (dash) vs “~” (tilda) for SPF/DKIM records in DNS. Google’s recommendation is a tilda.
Austin Whipple: ~ is basically “I don’t care what happens.” Go the extra mile to put in -all instead of ~all. I consider ~all to be only halfway fixed. It is non-trivial though, especially in this day when everyone has Mailchimp, Marketo, WordPress, or whoever that needs to email on your behalf.
Q: What is practical difference of the “dash”?
Austin Whipple: ~all means soft-fail, meaning that even if it fails, it isn’t counted automatically as a “reject this email.” -all is a hard fail, which means that if it fails, it fails. ~all means “I’m not entirely confident”
Q: To confirm, DMARC rule would only be a way to get confirmation of rejected emails?
Austin Whipple: A DMARC rule of “reject” or “quarantine” would be needed for the receiver server to actually do something about it.
Note: DMARC is the only good way to get reporting on [rejected emails], you can turn up a DMARC policy that only does reporting with very little risk. I use a tool called dmarcian.com to store, query, and present the DMARC reports.
Q: Have you ever hacked anyone?
Austin Whipple: Yes, according to the US justice department. Corporations are people, so yes I have, and I can provide evidence that I was permitted to do so at the time.
Q: What books would you recommend to those who are looking to learn more about how hackers think or how to harden their environments?
Austin Whipple:
To know how hackers think read, “Ghost in the Wires” by Mitnick.
My 5-star books:
- Ghost in the Wires: My Adventures as the World’s Most Wanted Hacker
- Gray Hat Hacking the Ethical Hackers Handbook, 3rd Edition
- Metasploit: The Penetration Tester’s Guide
- Professional Penetration Testing: Creating and Operating a Formal Hacking Lab
- SQL Injection Attacks and Defense
- Web Application Obfuscation: ‘-/WAFs..Evasion..Filters//alert
My 4-star books:
-
- 24 Deadly Sins of Software Security: Programming Flaws and How to Fix Them
- Ajax Security
- Hacking Exposed Web 2.0: Web 2.0 Security Secrets and Solutions
- Hacking Web Apps: Detecting and Preventing Web Application Security Problems
- The Tangled Web: Securing Modern Web Applications
- The Web Application Hacker’s Handbook: Finding and Exploiting Security Flaws
Q: Who are some security experts that you admire and that you think IT professionals should follow?
Austin Whipple: I actually don’t follow specific people. I am not on Twitter, so I couldn’t give any recommendations there. reddit.com/r/netsec is a pretty good resource for the security-minded IT professional who wants to keep up to date. Good curated content.
Q: Do you have any concerns about the government being able to intercept email messages and being able to scan them? *ahem* YAHOO for example.
Austin Whipple: If they want to, they’re going to be able to. Largely unlikely, though, I think? Yahoo in particular just sort of rolled over when it got the request, as opposed to Google fighting back. I’m sure there are more details to it, but even if you’re going totally on-prem with emails, they are sophisticated enough to get it. I think it’s one of those things where there are much more pressing concerns to deal with.
Q: How do you deal with vendors that don’t take your security concerns seriously?
Austin Whipple: Demonstrate need, whether that’s spoofing an email from their CEO or just straight up threatening to go with a more security-conscious company.
Q: What do you think about that iOS Zero-day a month ago? An Israeli startup named NSO Group sent a text and managed to remote jailbreak an iPhone.
Austin Whipple: For one, I hope everyone realizes that when jailbreaking your iPhone, you seriously have no idea what is being put on there as the base loader after that. It’s a *terrible* idea from a security perspective, especially when you start looking into the different players and who they are and how much they’re paying for iOS zero-days.
Q: What is your opinion on the “Internet of things”?
Austin Whipple: The big problem is patch management and proper network segmentation, neither of which are being taken seriously by many people. It’s a big research area right now among security professionals–I know that Bishop Fox is dedicating time to looking at it.
I love the idea of home automation though. You just have to be smart about putting everything on its own VLAN and realizing that in large part, you’re putting a bunch of Linux boxes around your house.
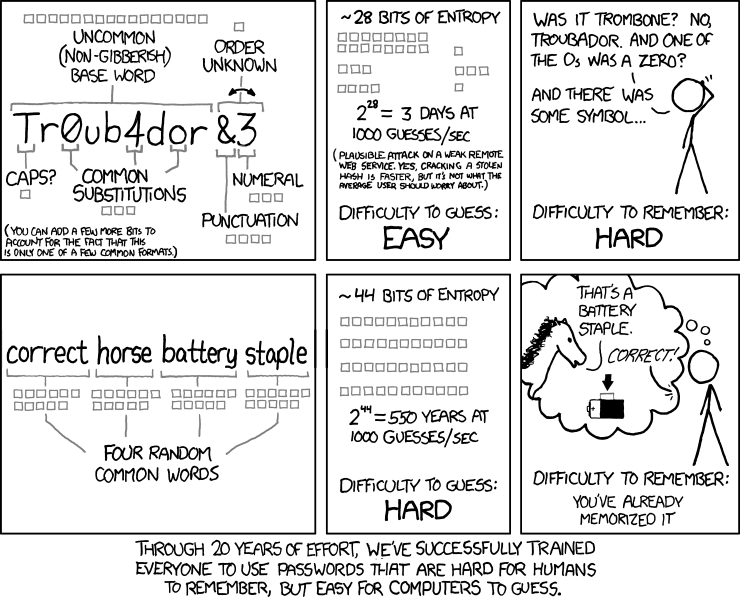
Q: What are the top things high school and middle school students should be taught to keep their data (relatively) safe?
Austin Whipple: Password usage, not putting their data/personal information on the internet without very good cause, being smart about apps installed on their phone and computer. If they want to learn about security, https://picoctf.com/ is a good place created just for high schoolers to dive in.
Q: Pineapple on pizza: An abomination, or taste revelation?
Austin Whipple: Eh. It has its place. I used to get it a lot when I was younger–have since switched to sausage+ham. Big fan of cream cheese substituting the tomato sauce.
Join the BetterIT Community
The BetterIT community brings together like-minded, forward-thinking IT professionals and enables them to communicate like never before. Topics of conversation range from G Suite and Office 365 to security, Google Apps Script, Chrome, BetterCloud, general tech talk, and even industry-specific discussion.