12 Vital Answers to Cloud IT and Google Apps Security Questions
July 16, 2015
8 minute read

Over the course of the last two months, we’ve had more than 1,000 people attend our two webinars: How to Overcome the Top 7 Security Flaws of the Google Apps Admin Console and Risk vs. Reward: A Framework for Evaluating & Implementing Cloud Apps. We answered a ton of great questions during the webinars, but we didn’t have time to answer them all. So we rounded up the best of the unanswered questions and turned them into an in-depth Q&A blog post.
For many, the cloud is a clear path to better performance, cheaper upfront costs, and greater productivity. For others, it’s uncharted territory. We recently set out to create a new type of webinar series with a simple goal: assist business leaders in their move to the cloud and help them better understand cloud IT.
Our cloud IT webinar series features BetterCloud Founder and CEO David Politis and BetterCloud Director of Strategic Accounts Kyle Quinn. Combined, they bring vast knowledge and experience in the world of enterprise cloud IT.
Below we’ll answer the best questions we received from our first two webinars. Let’s get to it.
1. What are some things to look out for when it comes to cloud application security?
- You should always understand the scope of the application installed. Is the application available domain-wide or is it only available to a single individual? If an admin installs an application domain-wide and it has full access to your domain’s data, you’re potentially putting your entire organization at risk.
- Applications change over time. They add functionality and may evolve to request more access as they grow. You need to actively monitor and review applications to ensure they are being used as originally intended.
- The software vendors you choose to work with should take your privacy extremely seriously. Make sure that you work with cloud application providers that are doing all they can to safeguard your data (see question #6). This takes time and research, but in the long run it’s well worth it.
- Ask yourself if the app is actually worth installing. For example, many schools blacklist games so that students won’t play them during school hours. Though this may not relate directly to security, it can have an impact on productivity.
2. To what extent can BetterCloud monitor Google Drive sharing?
BetterCloud offers extensive Google Drive security through “Drive Policies” and “Drive Audits.” These monitor the sharing settings of your Drive throughout your entire environment.
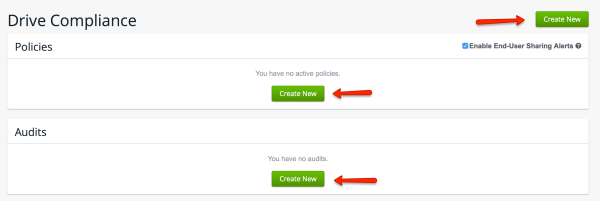
From the BetterCloud dashboard, you can set the conditions of a policy or audit that will help to secure your organization’s Google Drive. Policies can be created around the following:
-
- Sharing settings of documents
- With whom the documents are shared
- The content of the documents
- Note: Currently, only documents that are shared externally, publicly, or with the entire domain will be found.
A single policy can contain multiple conditions that can be applied in two ways: The policy will apply if it meets all of the conditions that are set, or if ANY of the conditions is met. Policies that are triggered when ANY of the conditions is met are stricter. You can select who (individuals, everyone, a specific subdomain, or an org. unit) a policy will be applied to and create exceptions that exclude certain individuals or org. units. A policy can even be given a start date, meaning it will only apply to documents created after the date you set.
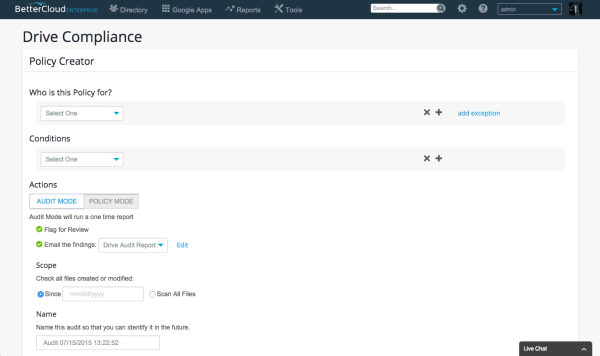
Actions can be taken when a user violates a policy, whether it’s related specifically to sharing, or another policy that you’ve set it up. The following actions can be taken when a policy is violated:
- Flag as violation
- Change sharing settings
- Change editors to viewers
- Transfer document ownership
- Send customized email to owner of the document
Multiple actions can be taken on when a violation in triggered. Think of policies and actions as an “if this, then that” scenario. If a violation is detected, then BetterCloud will automatically perform any actions you have set up.
You can have the results emailed to you or others in your organization if policies have been set up as an audit. Audits detect violations over a certain period of time.
You can learn more about Google Drive compliance and sharing settings in the BetterCloud for Google Apps help center.
3. Are external Marketplace apps installed by the users or installed by the company?
Google Marketplace Apps can be installed be either the users themselves or the company. This is your choice. There are restrictions that you, as an admin, can place on apps to limit which ones are available to download.
As mentioned in a previous post about maximizing Google Drive productivity, admins can help ensure their users are using apps that are appropriate for their domain.
To summarize, you can enable—or disable—the ability to use third-party Google Drive apps through the Google Apps Admin Console, create a custom Chrome Web Store for a domain, or pre-install Chrome extensions and certain apps to your domain.
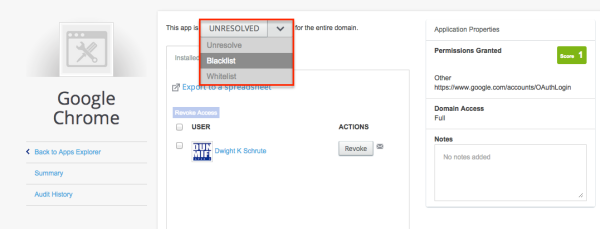
BetterCloud for Google Apps goes a step beyond, allowing admins to whitelist or blacklist certain apps.
4. What is BetterCloud’s philosophy on cloud application downloads?
At BetterCloud, we allow our employees to install or request apps, then we retroactively evaluate the application. Because of our security-focused culture and young and tech-savvy employee base, we find this to be a low risk, high reward approach; however, it requires more work on the part of IT.
This is the best approach for our organization, and it may not necessarily be the approach that your organization decides to—or even should—take. Different types of organizations require a different framework for application evaluation, but we find that our approach is a good middle ground for BetterCloud employees and IT.
5. What apps should I be disabling or limiting access to? What apps are the most common/serious offenders and where can I view what the app has access to?
Disabling or limiting access to certain apps is at your discretion and is different for all domains. However, malicious applications, Chrome extensions, and Android apps should always be blacklisted. BetterCloud provides an easy way to quickly surface this information.
BetterCloud assigns what’s called a “Permission Score” to apps, ranking (on a scale of 1 to 10) the amount of access the app has to your domain. The higher the score, the more things within your domain the app can access. Permission Score is calculated by determining if the app can read and/or write to certain areas of your Google account.
With BetterCloud, you can see if an app can read or write to the following:
- Drive
- Directory
- Domain
- Account
- Other
Apps with higher permission scores should be scrutinized to make sure they are only accessing what’s necessary, and not acting maliciously.
BetterCloud can perform what’s called a “Third-party App Audit.” The audit allows you to approve or revoke access/authorization to third-party apps installed on your domain. Third-party apps are put into one of three categories:
6. What standards should Independent Software Vendors (ISVs) be held to?
There are certain standards like SSAE-16, which is designed for service organizations and helps to provide customers with “complete confidence” when working with certified companies. TRUSTe, another standard, is dedicated to ensuring companies are committed to customer privacy.
Organizations can also choose to self-certify with U.S.-E.U & U.S.-Swiss Safe Harbor Frameworks. The frameworks “prohibit the transfer of personal data to non-European Union countries that do not meet the European Union (EU) ‘adequacy’ standard for privacy protection.” The U.S. and Swiss government also worked to develop “a separate ‘Safe Harbor’ framework to bridge the differences between the two countries’ approaches to privacy and provide a streamlined means for U.S. organizations to comply with Swiss data protection law.”
BetterCloud adheres to all three standards.
Technical software as a service (SaaS) standards also exist. For instance, application programming interfaces (APIs) and single sign-on are both technical SaaS standards that have been developed by the industry over time.
There are also numerous industry-related security standards in the U.S. like HIPPA (Healthcare), PCI DSS (Retail), CIPA (Education), CJIS (Criminal Justice) and many more throughout the U.S. and around the world. Organizations must remain compliant with these standards or else be subject to fines and possible additional penalties.
7. How can I track or alert admins when there is a suspicious login?
To be immediately notified of suspicious activity on your domain, you can set up account activity alerts within the Google Admin console. This will allow you to receive an email each time an unusual event is detected.
Though Google does provide a suspicious login alert, without additional information it becomes difficult to determine if an account is truly compromised or if it’s simply a false alert. As an admin, it’s important that you identify what account actions were taken after a suspicious login was detected.
BetterCloud’s Domain Health and Insights Center helps surface critical information and security risks for all users in your domain, a key measure in preventing data loss from a compromised account.
8. Is there a way to make my company’s login more secure? Right now, I require a certain password length, but that’s it.
It’s critical to make sure your employees’ passwords are secure. In 2012, 80% of security incidents were due to the use of weak passwords, according to a Trustwave 2012 Global Security Report.
So what can you do?
Adding 2-step verification for your employees is one of the simplest and most effective password security measures you can take. You can also require your employees to reset their passwords after a certain number of days with BetterCloud.
9. Where do we take training to become a Google Apps Certified Admin or a Google Apps Deployment Specialist?
Follow the links to find more information about training for the Certified Admin and Certified Deployment Specialist exams.
You can also learn more about the Google Apps Certification Exam by watching the video below.

10. Can you give an example of an app that an organization would install domain-wide?
Many Google Marketplace Apps can help improve productivity, collaboration, communication, security and management, and much more. Security and management apps like BetterCloud, project management tools like SmartSheet or CRM tools like Insightly are commonly installed domain-wide.
11. Does BetterCloud have automation to remove application-specific passwords when deprovisioning a user?
Yes! This is a built-in feature of BetterCloud.
Application-specific passwords enhance security for users that have turned on 2-step verification. They are only required for applications that cannot require 2-step verification. Common applications that need application-specific passwords are:
- POP and IMAP email clients such as Outlook, Mail and Thunderbird
- Gmail and Google Calendar on smartphones
- Youtube Mobile
- Adwords Editor
- ActiveSync for Windows Mobile and iPhone
- Picasa, 3D Warehouse, Sketchup, and installed applications
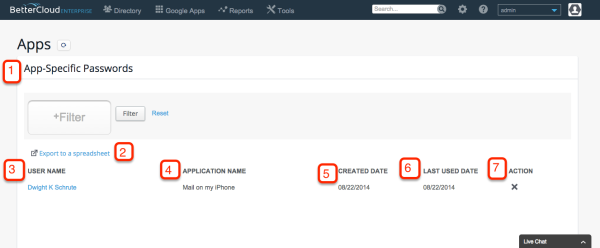
BetterCloud can view and perform the following actions on application-specific passwords.
- Filter by user’s name (1)
- Export to spreadsheet (2)
- View user who installed the app/password (3)
- View application name (4)
- Note: When users create an application-specific password, they must title it. The title they choose can be whatever they choose and may not be a true representation of the application.
- View the date that the password was created (5)
- View the date that the app was last used (6)
- Remove authentication (7)
- Note: Admins can only delete a password; they cannot create one.
12. What will the next webinar cover?
The next webinar will discuss ways (and tools) that will help you reduce the amount of time you’re spending on routine maintenance and updates.
It will cover the following:
- How to configure your directory in a way that optimizes for long-term efficiency
- Tips to becoming proactive about security and automating policy enforcement
- Tricks to empowering other departments, like HR or marketing, to manage their related IT tasks
- How the role of IT is changing as a result of focusing on non-routine work
Update: This webinar has passed, but you can view a recording of it here: 5 Ways to Automate Routine Tasks & Focus on Higher-Value Work.