The BetterCloud Platform
The Platform built for Lean IT, no coding experience required
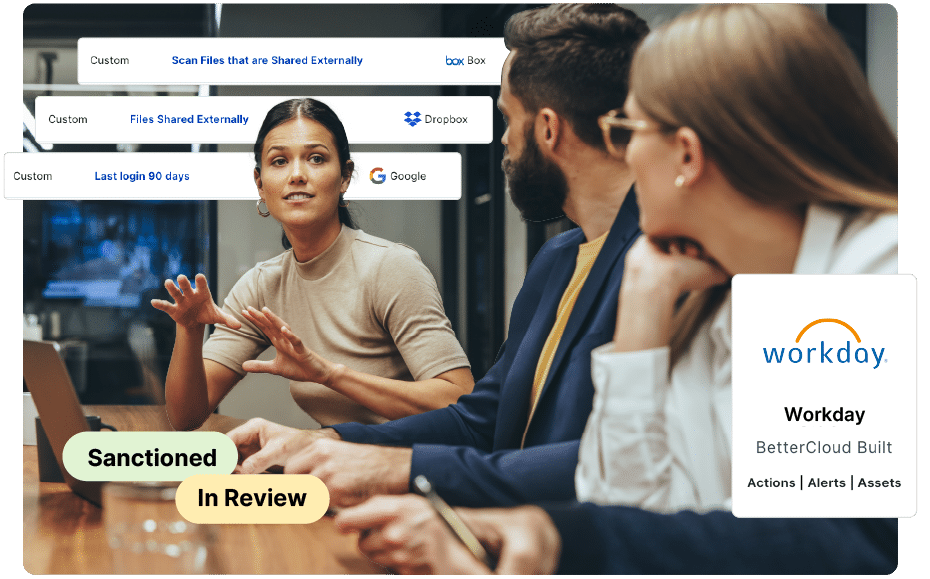
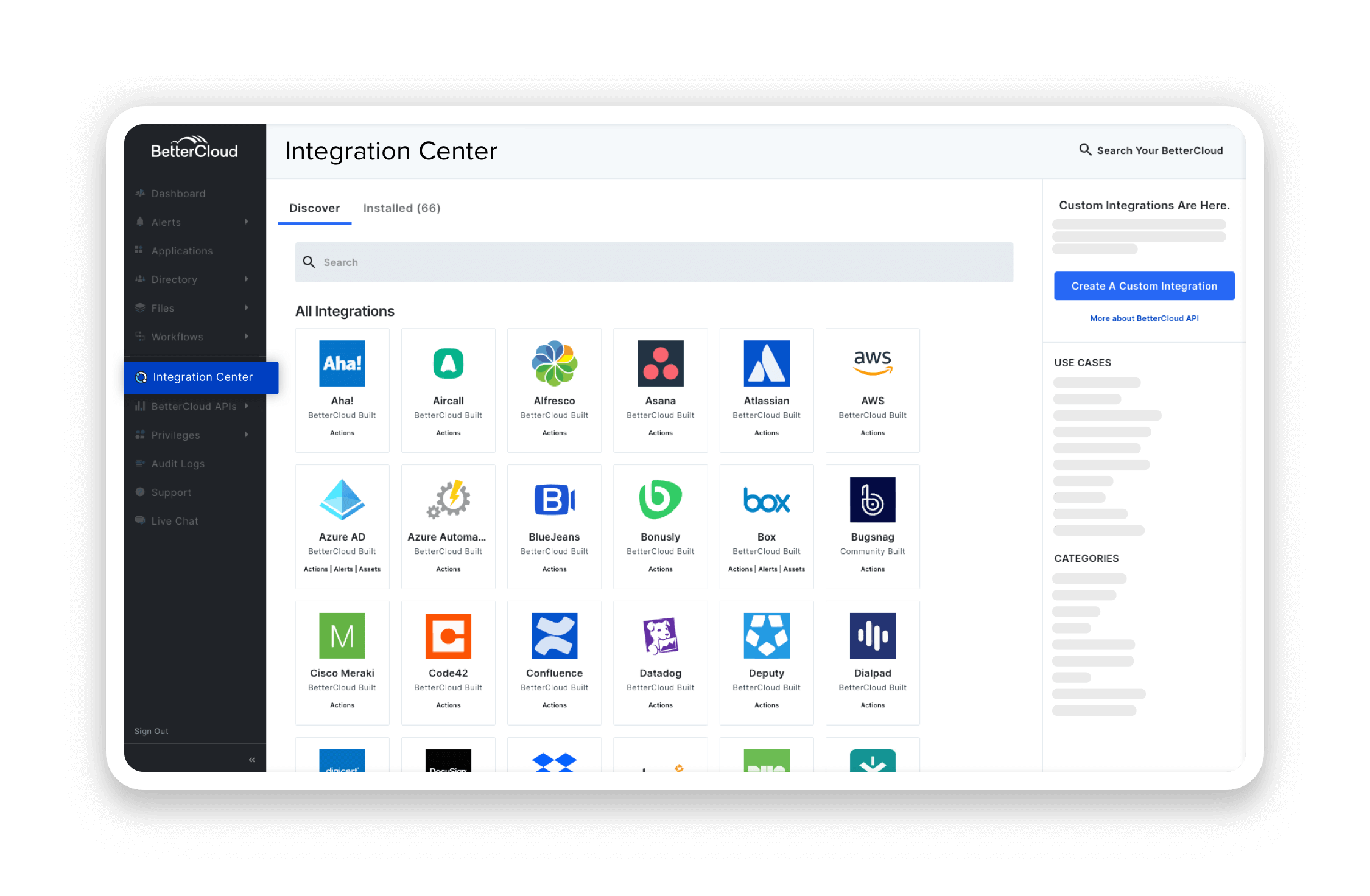
The first comprehensive SaaS Management Platform that gives IT control over applications, licenses, users, and contracts. Vendor intelligence and advanced automated workflows combined elevate SaaS management and elevate IT.
“
Bettercloud answered the most problems for us. It was the solution that could save our team time and effort. It aligned with the way the IT team was looking to automate and streamline processes."
— Steve Foley, Senior IT Automation Engineer at Seismic
Features of BetterCloud
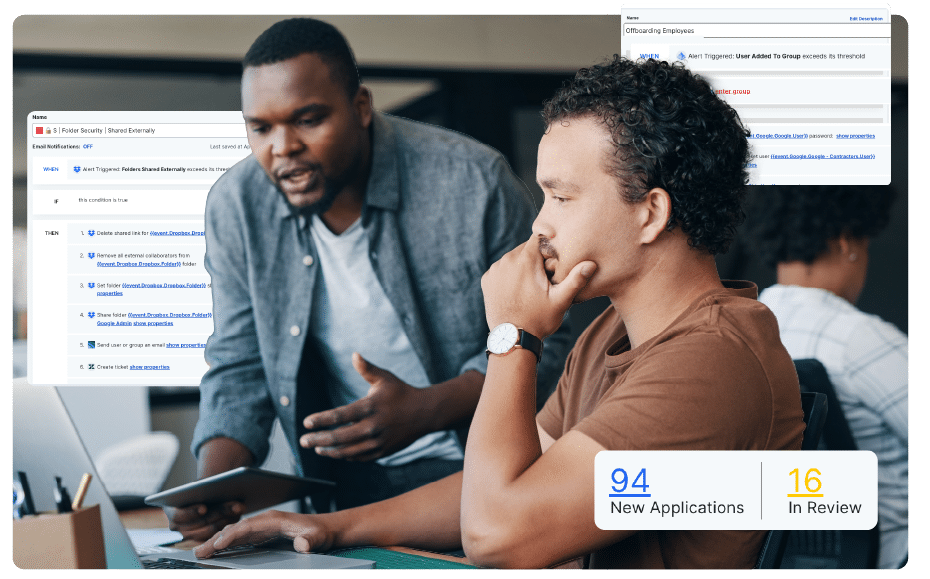
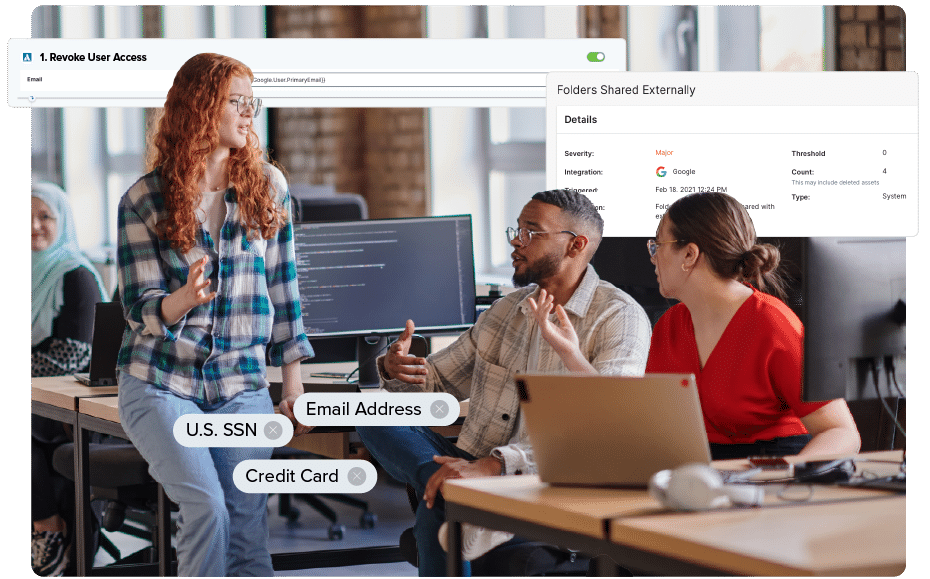
IT teams run tens of thousands of automated workflows each day in BetterCloud, eliminating thousands of hours of manual work. With our no-code workflow builder, Lean IT teams can automate dozens of tasks in a matter of hours. The easy things should be automated, so you can get back to the important things.
We built BetterCloud with every IT employee in mind. Our SaaS management platform is quick to implement and easy to use. The work of IT is important and the company depends on you; a SaaS Management Platform should enable that work, not add to it.
- Configure automations with a no-code drag and drop workflow builder
- Automate employee onboarding and offboarding with dynamic workflow decisioning and workflow scheduling
- Access a library of hundreds of workflow actions, triggers, and templates

Knowledge-share with fellow IT experts using BetterCloud
Join our Slack community of 6,000+ IT professionals to learn about trends and get help with your daily tasks. Check out our library of case studies when you need even more automation inspiration.
With a strong commitment to automation, FIRST learned how to harness the full potential of Bettercloud and within a few weeks build out the necessary workflows to address recurring pain points within the business.
The IT team at Bark is using their new free time unlocked from automating manual work to uplevel their skill sets and improve security with automated IT controls.
Sprout Social used to manually onboard and offboard each employee. They are using their reclaimed time to focus on improving user experiences.
See what else BetterCloud can do for you
Trusted by IT: BetterCloud is the highest rated and most complete SaaS Management Platform on G2
G2 rated BetterCloud a Leader in 30+ of its Spring 2024 grid reports, including SaaS Operations Management, Data Loss Prevention (DLP), Data Security, User Provisioning and Governance (UPG), and Cloud File Security, among others.