What is zero trust? All you need to know
February 25, 2021
7 minute read

As we enter a new era of remote work, companies are increasingly adopting Zero Trust to bolster the security of their newly distributed workplaces.
But what exactly is Zero Trust? And what do you need to implement it? In this post, we’ll explore all those topics and more.
Zero Trust doesn’t exist as a product
First, let’s clear up a common misconception. Zero Trust is not a product or platform.
“Attempting to buy Zero Trust as a product sets organizations up for failure,” according to Forrester Research. “Vendors enable Zero Trust; they are not Zero Trust itself.”
So, if it isn’t a specific product you can buy, then what is Zero Trust?
Zero Trust is best defined as a security framework focused on securing applications and data, rather than securing the network. According to NIST, Zero Trust operates on the premise that trust is never granted implicitly but must be continually evaluated.
It’s a new paradigm in security thinking, certainly.
And while you can’t buy Zero Trust, you can (and should) rely on existing technologies to build a Zero Trust architecture. We’ll dive into more detail on this later, but examples of technologies include microsegmentation, identity and access management (IAM), multi-factor authentication, configuration management database (CMDB), and an access proxy.
It’s important to note, though, that Zero Trust is more than just implementing individual technologies. As TechRepublic puts it, it’s “a web of connected policies, practices, software, and hardware that create an entire Zero Trust ecosystem . . . It’s a total commitment to a process that alters large swaths of an organization’s structure.”
Is “Zero Trust” a misnomer?
Some have expressed criticism that “Zero Trust” is a misnomer, since some level of trust must exist, or no data would ever be accessed or shared. Jim Richberg, Chief Information Security Officer of Fortinet, states, “Zero Trust does not mean people or assets are untrustworthy— [it’s] more that trust is transactional, that it has a half-life, to use NIST’s language, even within a given connection or operating session.” Richberg added, “I do think this label, at one level has not been helpful, because it starts implying either paranoia or my people are not trustworthy.”
It’s best defined as, “No trust by default.” Now that we’ve made that distinction, let’s move on to how this security framework gained momentum and how it all works.
Growth of Zero Trust security framework
Zero Trust is a concept that was largely created by and first implemented in government. As stated in NIST Special Publication 800-207, “Zero Trust assumes there is no implicit trust granted to assets or user accounts based solely on their physical or network location (i.e., local area networks versus the internet) or based on asset ownership (enterprise or personally owned).”
In Zero Trust, security is no longer defined based on where you’re connecting from. The NIST Publication continues, “Zero trust focuses on protecting resources (assets, services, workflows, network accounts, etc.), not network segments.”
The old approach relied on networks having a trusted perimeter. Like a moat around a castle, everyone inside was considered “good” and everyone outside was considered “bad.” However, this is no longer relevant. The perimeter has been eroding for years as organizations give access to remote users and partners, as well as cloud-based assets and bring your own device (BYOD). Trusting, by default, anything within the security perimeter is an outdated approach.
On the other hand, Zero Trust security is an approach that trusts no user, device, workload, or system, either inside or outside the perimeter. No one and nothing should be trusted by default, regardless of the location in which it is operating from. In addition to securely enabling remote work, Zero Trust architecture helps organizations comply with numerous regulations.
Security without the perimeter
Zero trust is the answer to security without a perimeter. Policy enforcement must be done at the point of access. When people are the new perimeter, identity becomes a foundation of the Zero Trust strategy.
Modern access management is about making sure that the right people have the correct level of access only when they need it—and that access is managed on a continual basis, all while providing a frictionless experience for the end user.
Implementing Zero Trust
Building a Zero Trust architecture
Zero Trust is an operating principle, a philosophy and, according to NIST, a set of paradigms. The best way to architect and implement a new security framework is to start with a “no trust, but verify” model. In other words, every service request made by any user or machine is properly authenticated, authorized, and encrypted end to end.
Identity is critical
Zero Trust network access is an identity-based security model. The model has to take into account a user’s corporate identity, which is a combination of the user plus the device used to request the service at a point in time. Context-based authentication that considers multiple data points is known as Adaptive Access. Access is provided only after identity is verified by a trust broker. Identity-aware authentication sources must span the plane of technologies.
Zero Trust requires authenticating identity, authenticating the health of each device, and then making the decision in real time to allow access. One device doesn’t have to trust another one just because they exist in the same network, VLAN, or control plane. Additionally, Zero Trust network access hides the network location (IP address) and instead, relies on identity-based authentication to establish trust.
Make trust transactional, dynamic, and context-based
As a model, Zero Trust can be implemented in different ways. But the baseline is to have no trust, and only grant trust to users and devices:
- Dynamically
- As needed in each role
- For whatever they’re doing at that time
Implementing Zero Trust requires a unified approach to avoid the security gaps and complexities that result in attempting to use disparate technologies. Instead, Zero Trust requires you dynamically understand who your users are and dynamically permission them based on their credentials.
Decisions to grant trust must extend the binary “grant access or not,” and instead secure their interactions within those resources once access has been granted. With this positive trust, every type of connection is for a specific need of that individual, entity, or device, based on a risk profile. Securing your interactions is an important part of mitigating your insider threats. SaaS security best practices take a similar approach by following the user and securing user activity, such as file sharing and file downloads, inside of SaaS apps.
Microsoft outlines a Zero Trust approach based on six foundational pillars of critical resources to be defended:
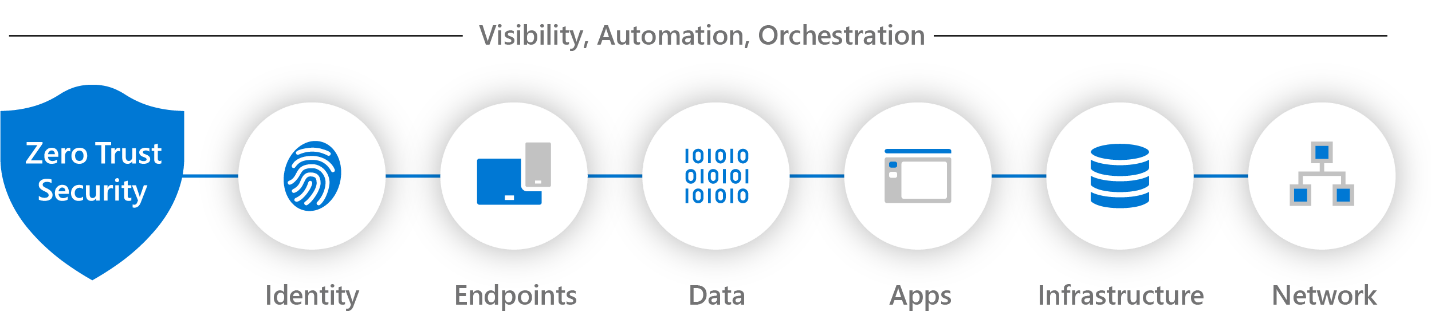
The security elements of Zero Trust (Microsoft)
Limit lateral movement
A Zero Trust architecture also aims to limit internal lateral movement, resulting in a reduced blast radius. Because trust is granted dynamically as needed, Zero Trust can stop the lateral movement that often accompanies network penetration, thus mitigating the impact of any successful attack. This approach is threat agnostic and will effectively reduce risks of attacks from insider and outsider threats alike.
Continuous assessment and data protection
Your Zero Trust architecture must protect the data while it’s shared continuously between workstations, application servers, databases, mobile devices, SaaS apps, and across public and private networks.
Risks should also be calculated in real time on an ongoing basis. While you may be trusted to access an asset in your role, if you reach a threshold that indicates you’re doing something risky, access could be limited or rescinded entirely. Continuous monitoring with telemetry can provide broad, but granular visibility and enable real-time risk assessment.
Securing and managing data also requires categorizing and developing data classification schemas and encrypting data both at rest and in transit. Ideally, data will be protected throughout its lifecycle as it flows through the network among various assets and users. Data must be protected in some sort of encryption or separation from other traffic. While you may do the “handshake” to validate a connection, you should also know what’s riding back in that SSL encrypted pathway.
Workloads, particularly those running in public clouds, must have Zero Trust controls such as policy-based API inspection and control, container file and active memory protection, and guest host firewall. Additionally, security and network operations need to align and strive to avoid increases in latency. When security and convenience clash, convenience is always going to win.
Microsegmentation
Microsegmentation isolates workloads from one another and secures them individually by way of distinct zones in data centers and cloud environments.
As described in Security Boulevard, “Microsegmentation minimizes the damage that hackers can do if they gain access, by isolating servers and systems into separate zones to contain intruders or malware, as well as insider threats—much like the segmented watertight compartments of large ships. Moving to virtualized data centers using software-defined networking (SDN) enables more advanced, granular zoning, allowing networks to be divided into hundreds of microsegments.”
With the proliferation of virtual machines, a single server can host hundreds of workloads, each with its own security requirements. Microsegmentation provides the granular security at the workload level that such environments require. Identify valuable assets and define microsegments around them, and create multiple junctions and inspection points that block malicious or unauthorized lateral movement.
Additionally, moving to a microsegmentation architecture streamlines policy management by enabling you to simplify firewall policy management.
Zero Trust helps tackle blind spots
Distributed environments create dangerous blind spots, just like shadow IT. Blind spots conceal security threats that many IT and security professionals don’t even know exist. Organizations don’t know what’s going on in their remote workers’ home environments. Even the workers may not know.
Security Boulevard writes, “While [most enterprises] seek to gain from cost savings and efficiencies in adopting these new accelerated, highly automated cloud models, enterprises struggle with the ensuing sprawl and the numerous blind spots and increased complexity that come with the territory. Modern reality means the true threat has little to do with the perimeter and everything to do with defending against these new blind spots.”
Identify malicious or unusual behavior
Your security architecture might include flags for suspicious behavior, such as attempts to download large quantities of data. However, a certain activity can be a suspicious anomaly in one situation and entirely innocuous in another. Ideally, requests should be viewed with the added insight of context, which increases the accuracy of such flags, reducing both false positives and negatives, helping avoid alert fatigue.
In order to mitigate risk, cybersecurity solutions must accurately identify risks, which is challenging, particularly at scale. Context is vital to improving risk identification and effectively detecting malicious activity. For example, rather than taking a single request and assessing it in isolation, examine users’ behavior across all requests in a single session to generate a far more accurate risk score.
Getting started with Zero Trust
Zero Trust is a popular concept and something that more and more IT and security professionals are thinking about. Many have already progressed along a Zero Trust journey without even realizing it, for example, by implementing IAM. Steps for getting started include:
- Create a detailed roadmap outlining your main workstreams
- Conduct a Zero Trust assessment of your current infrastructures
- Set goals, identifying next milestones and priorities along with technologies
- Look at targets of opportunity. Think big but start small.
- Build an interdepartmental team including security, IT, and business leaders
- Identify interdependencies, including existing security, IT, and business projects
Want to learn more about Zero Trust? Check out these additional resources:
- Data Protection and SaaSOps on Your Zero Trust Journey
- Taming SaaS Security Challenges with the Zero Trust Security Model
- Rolling Out a Zero Trust Security Model? Here’s What You Need to Think About
- The Essential Steps, Tools, and Technologies for Achieving a Zero Trust Security Model in Your SaaS Environment



