What are the 4 types of access control
Access control is vital for securing SaaS applications. It ensures only authorized users access specific resources. Understanding access control types is crucial for IT managers. It helps in managing user permissions effectively.
There are four main types of access control systems. Each has unique features and applications.
- Discretionary access control (DAC) offers flexibility. It allows resource owners to decide access permissions.
- Mandatory access control (MAC) is more rigid. It is used in high-security environments.
- Role-based access control (RBAC) simplifies management. It assigns permissions based on user roles.
- Attribute-based access control (ABAC) provides fine-grained control. It uses attributes for access decisions.
Choosing the right access control type is essential. It should align with organizational needs and security policies.
Understanding access control: The foundation of SaaS security
Access control is a cornerstone of SaaS security. It protects sensitive information by regulating user access.
Strong access control systems prevent unauthorized data exposure. They are integral to any robust security strategy.
In SaaS environments, precise access management is critical. It ensures compliance with organizational policies.
Key components of effective access control include:
- Defining clear access policies
- Implementing appropriate control types
- Regularly auditing access permissions
By implementing these components, IT managers can reduce risks. Secure access management improves overall SaaS security posture.
Overview of access control types
Access control types are essential for managing user permissions in SaaS. They define how access is granted or restricted.
Four primary access control types exist, each with unique characteristics:
- Discretionary access control (DAC)
- Mandatory access control (MAC)
- Role-based access control (RBAC)
- Attribute-based access control (ABAC)
Selecting the appropriate type depends on organizational needs. Each type offers different levels of flexibility and security. Understanding these differences is crucial for effective access management.
Discretionary access control (DAC)
Discretionary access control (DAC) empowers resource owners with the authority to determine access. This control method grants them the flexibility to set permissions based on their discretion. It's favored for environments requiring adaptability.
However, DAC requires careful management. Without oversight, it can lead to security gaps. Users with shared access may alter permissions, sometimes unknowingly. This can result in unauthorized access if monitoring is lax. BetterCloud offers tools for monitoring super-admin privileges to address such concerns.
DAC is user-centric, allowing personalized control levels. It's beneficial in environments where collaboration is a priority. Key features of DAC include:
- User-defined access permissions
- Flexibility in sharing resources
- Potential for permission overlap
While DAC is adaptable, it necessitates strong auditing processes. Without these, potential risks increase. Centralized oversight, as described in our SaaS operations management guide, can help minimize such risks. Regular reviews are critical for maintaining security within DAC setups.
How DAC works in SaaS environments
In SaaS settings, DAC mirrors its general principles. Resource owners within the organization manage access privileges. This setup allows SaaS application users to share resources easily.
However, it's crucial to oversee permissions. Mismanagement can lead to unauthorized access. A defined framework helps establish boundaries. Here are key points to implement DAC effectively:
- Owners set access rules for their resources.
- Monitoring ensures compliance with security standards.
- Centralized audits help detect irregularities.
Integration with identity management tools is beneficial. These tools provide an extra layer of oversight. They help ensure that DAC's flexibility doesn't compromise security. For SaaS environments, a balance between flexibility and control is essential.
Pros and cons of DAC
DAC offers clear benefits, including enhanced flexibility and user autonomy. It's ideal for fast-paced and collaborative environments. Yet, there are downsides to consider.
- Pros:
- User-controlled access
- High flexibility
- Cons:
- Risk of unauthorized changes
- Requires diligent oversight
DAC's pros make it a viable choice for many. However, its potential risks necessitate thorough management. Properly implemented audits and reviews are crucial. They help mitigate the risks associated with DAC's flexibility.
Mandatory access control (MAC)
Mandatory access control (MAC) is a more rigid framework compared to DAC. It's ideal for environments requiring stringent security. MAC restricts user capability in modifying access permissions. Instead, a central authority dictates these rules.
In MAC, access policies are predefined and enforced organization-wide. This minimizes the risk of inconsistent permissions. Users are assigned security labels, matched against access requirements. Such measures ensure controlled data distribution. Learn more about enforcing access privileges in SaaS.
MAC is prevalent in high-security domains like military and government. It offers a structured and predictable security model. Key characteristics of MAC include:
- Centralized access policies
- Consistent and enforced access rules
- Reduced user flexibility in permission settings
MAC significantly limits users in customizing access. Although it lacks flexibility, it ensures robust security. Organizations must carefully design security policies. Such planning is essential to maximize MAC's benefits while minimizing rigidity.
How MAC works in SaaS environments
In SaaS environments, MAC offers a centralized security approach. It ensures strict access controls on sensitive data. SaaS providers enable MAC to enforce policy-driven access across various applications. Organizations benefit from consistent security enforcement.
A central security officer typically manages these policies. MAC's structure suits compliance-heavy industries. Key strategies for implementing MAC in SaaS include:
- Predefined security policies govern access control.
- Users assigned labels that align with security policies.
- Regular policy updates accommodate evolving needs.
Security labels and classifications are critical. They determine access eligibility for SaaS resources. Regularly updating policies is crucial. This practice ensures alignment with current organizational needs and compliance requirements.
Pros and cons of MAC
The structured nature of MAC offers distinct security advantages. It creates a predictable and controlled environment. However, its rigidity can be a double-edged sword.
- Pros:
- Strong security consistency
- Central policy enforcement
- Cons:
- Limited flexibility
- Complex implementation
MAC is suitable for environments with high security demands. Although it provides robust security, it can hinder user flexibility. Adopting MAC requires understanding its limitations. Proper planning ensures organizations can leverage its strengths effectively.
Role-based access control (RBAC)
Role-based access control (RBAC) simplifies access management by assigning user roles. Each role has specific permissions aligned with job functions. This approach reduces complexity in managing individual permissions.
RBAC is particularly effective in dynamic SaaS environments. It supports large-scale user management effortlessly. Roles are predefined, requiring thoughtful design to ensure appropriate access levels. Once set, roles streamline user onboarding and changes. For more insight, visit our fundamentals of RBAC article.
Organizational roles dictate what resources each user can access. This method aligns access with business objectives. For SaaS, RBAC facilitates scalable access management. Its application helps maintain a balance between security and usability.
Key characteristics of RBAC include:
- Defined roles aligned with organizational needs
- Streamlined access management
- Scalable for growing user bases
RBAC is widely adopted due to its practicality. It provides a structured, efficient way to manage permissions. With it, organizations can quickly adapt to changes while maintaining control.
How RBAC works in SaaS environments
In SaaS environments, RBAC is integrated into identity management systems. It allows administrators to set roles and permissions upfront. This setup reduces the need for constant manual permission adjustments.
Roles such as “admin” or “viewer” define access scope. When a user is assigned a role, they inherit pre-defined permissions. This system can scale easily as new roles are added or altered.
Key elements for implementing RBAC in SaaS include:
- Establishing clear role definitions
- Mapping roles to necessary permissions
- Automating role assignments based on user responsibilities
By automating these processes, RBAC ensures efficient and consistent access across SaaS applications. It aligns with both security protocols and operational needs, making it a favored choice.
Pros and cons of RBAC
RBAC brings several advantages to access management. However, it also presents some limitations. Understanding these helps organizations optimize its use.
- Pros:
- Simplifies large-scale user management
- Efficiently aligns with organizational roles
- Cons:
- Requires careful role planning
- May need regular updates to roles
RBAC's scalability and simplicity are appealing. Yet, it demands upfront effort in defining roles and permissions clearly. Organizations must regularly review roles to ensure they reflect current operations and security needs.
Attribute-based access control (ABAC)
Attribute-based access control (ABAC) offers granular control by evaluating attributes. These attributes can belong to users, resources, or environments. ABAC is highly flexible and context-aware, adapting to complex access needs.
In ABAC, access decisions are made dynamically. Policies consider multiple attributes, including roles, user locations, and time of access. This depth allows organizations to enforce nuanced security policies.
ABAC's flexibility is particularly beneficial in SaaS environments. It offers tailored security, aligning with organizational policies and compliance mandates. Companies can respond to evolving security threats effectively.
Key features of ABAC include its adaptability and precision. It provides thorough control over resource access. However, managing ABAC requires robust policy development and oversight.
Attributes form the core of ABAC decisions. Examples include:
- User identity (e.g., department)
- Resource classification (e.g., sensitivity level)
- Environmental factors (e.g., time of day)
These components work together to establish sophisticated access policies. ABAC allows organizations to safeguard their SaaS resources dynamically and efficiently.
How ABAC works in SaaS environments
ABAC operates within SaaS by integrating with identity management systems. These systems evaluate numerous attributes to determine access rights. The decision-making process happens in real-time, enhancing security.
Policies are crafted considering various attributes, ensuring finely-tuned control. These policies adapt to changing contexts, ensuring continual compliance and security. In SaaS, ABAC can support diverse user bases with differing requirements.
To implement ABAC in SaaS, organizations should:
- Identify relevant attributes
- Develop comprehensive policies
- Maintain up-to-date attribute data
ABAC's capability to manage complex scenarios makes it invaluable. It supports custom rules that prevent unauthorized access, even as variables change.
Pros and cons of ABAC
ABAC provides precise control over access permissions. It accommodates complex, dynamic requirements in SaaS environments. Despite its advantages, managing ABAC can be demanding.
- Pros:
- Highly flexible and dynamic
- Supports detailed access policies
- Cons:
- Complex setup and management
- Requires extensive policy formulation
While ABAC's strengths lie in its flexibility, complexity is also its challenge. Successful implementation depends on thorough understanding and strategic policy development. Organizations can achieve higher security assurance by employing ABAC effectively.
Comparing the four access control types
When comparing access control types, each has unique attributes. Discretionary access control (DAC) offers flexibility but carries risks. It allows resource owners to dictate permissions, which may lead to inconsistent security policies.
Mandatory access control (MAC) provides stringent security measures. In MAC, access policies are centrally managed, ensuring compliance but at the cost of flexibility. It suits high-security environments best.
Role-based access control (RBAC) simplifies access management by aligning permissions with organizational roles. It's efficient but requires careful role definition to avoid overlaps and gaps in permissions. Combine RBAC with the principle of least privilege for best results: PoLP vs RBAC.
Attribute-based access control (ABAC) excels in its adaptability. It uses diverse attributes for precise control, albeit demanding complex policy management.
Summary of access control types
- DAC: Flexible but owner-dependent
- MAC: Highly secure, less flexible
- RBAC: Simplifies management, needs defined roles
- ABAC: Highly adaptable, complex policies
Choosing the right type involves balancing security needs with operational efficiency. Understanding each type's capabilities assists in crafting an effective access control strategy.
Choosing the right access control system for your organization
Selecting the appropriate access control system is crucial for your organizational security. Consider your specific business needs, regulatory requirements, and the environment in which your SaaS applications operate.
Before deciding, assess your organizational structure. An enterprise with clear role definitions might benefit most from role-based access control (RBAC). On the other hand, industries with dynamic and complex environments might lean towards attribute-based access control (ABAC).
Identify potential security threats and operational challenges. Understand each access control type’s strengths and limitations. This understanding is essential for aligning security with organizational goals.
Factors to consider
- Organization size: Larger organizations may prefer RBAC for structured roles.
- Security requirements: High-security needs might necessitate MAC.
- Complexity of environment: Dynamic environments could benefit from ABAC.
- Flexibility vs. control: Balance between adaptability and strict policy enforcement.
Careful evaluation ensures the chosen system meets your security needs effectively while supporting operational goals.
Best practices for access management in SaaS applications
Effective access management in SaaS applications is essential for maintaining security. It also helps ensure compliance with industry standards and regulations.
Begin by conducting regular access reviews. This practice helps identify and revoke unnecessary permissions. It maintains the principle of least privilege, minimizing risks.
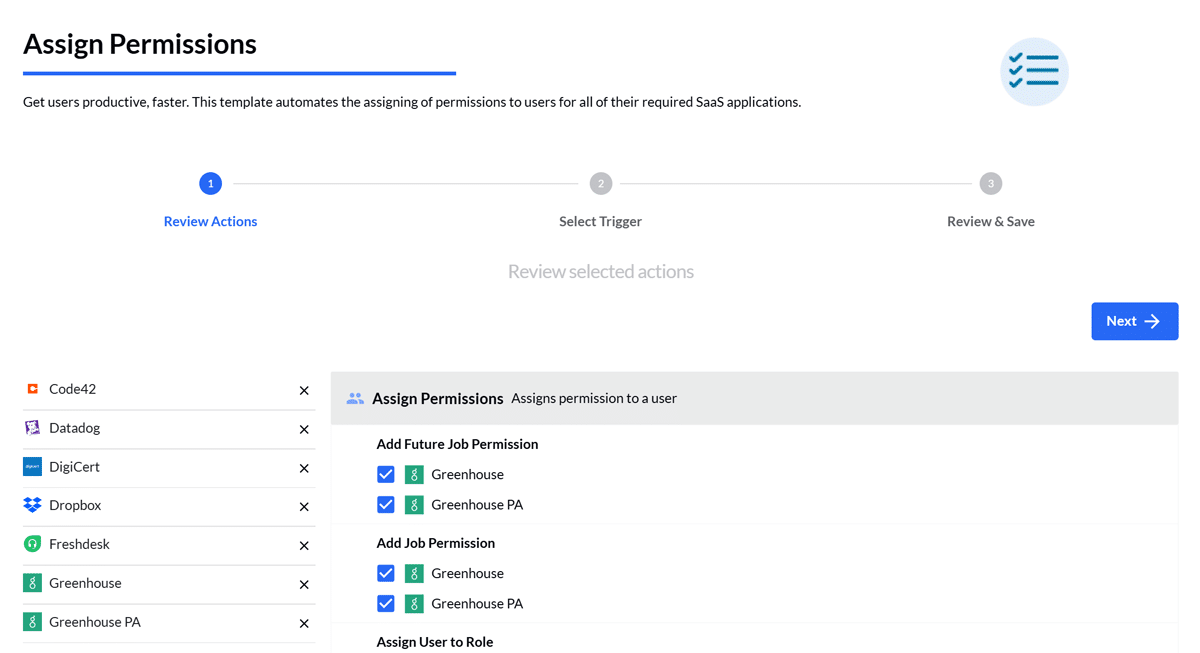
Employ automation tools for user provisioning and deprovisioning. Automated processes reduce human error and enhance efficiency. They also ensure consistency in access management.
Integrate access control with identity and access management (IAM) solutions. Such integration provides a unified view of user access across all platforms, enhancing security oversight.
Key best practices
- Regular access audits: Conduct frequent reviews of user permissions. Learn more.
- Automation: Use tools to streamline access changes.
- Integration: Combine access control with IAM for holistic security.
- User training: Educate users on security best practices.
- Policy documentation: Clearly define and communicate access policies.
By following these best practices, your organization can achieve robust security while supporting operational efficiency.
Conclusion: building a secure and flexible access control strategy
Adopting a robust access control strategy is vital in today's dynamic SaaS environments. By understanding and implementing the right access control types, organizations can protect sensitive data while ensuring seamless operations.
The balance between security and usability is key. Tailor your access control approach to meet the specific needs and risks of your organization.
Continual adaptation and vigilance are essential. As threats evolve, ensure your access control measures remain aligned with your security objectives and organizational goals.
BetterCloud strengthens access control
BetterCloud’s unified SaaS Management Platform empowers organizations to implement and maintain any access control model—DAC, MAC, RBAC, or ABAC—while aligning with least-privilege principles, automated provisioning, and granular oversight. This ensures your chosen access control framework delivers both security and operational efficiency.
Need help implementing these controls? Request a BetterCloud demo today to see how our platform simplifies access control, compliance, and security.