SAAS COST CONTROL
Control SaaS costs with intelligent SaaS spend management software
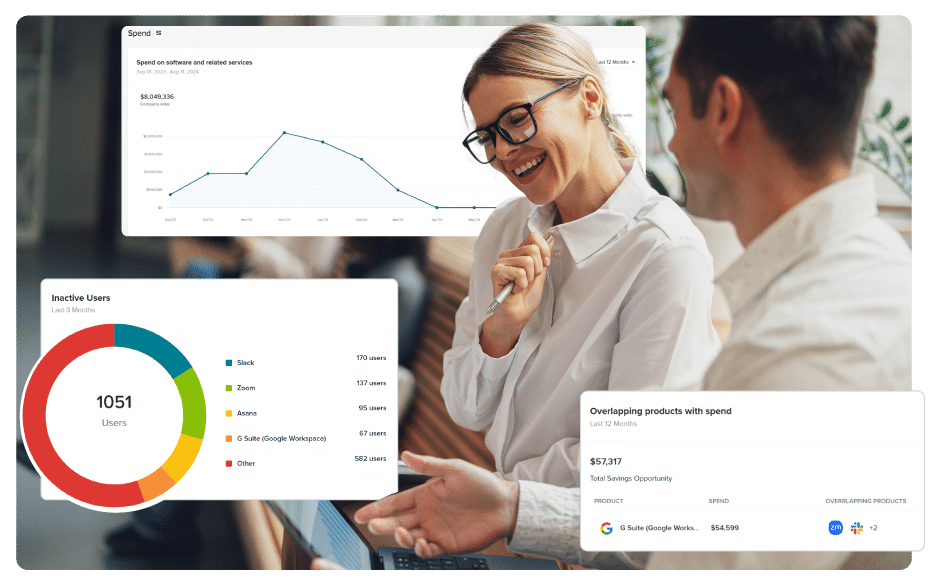
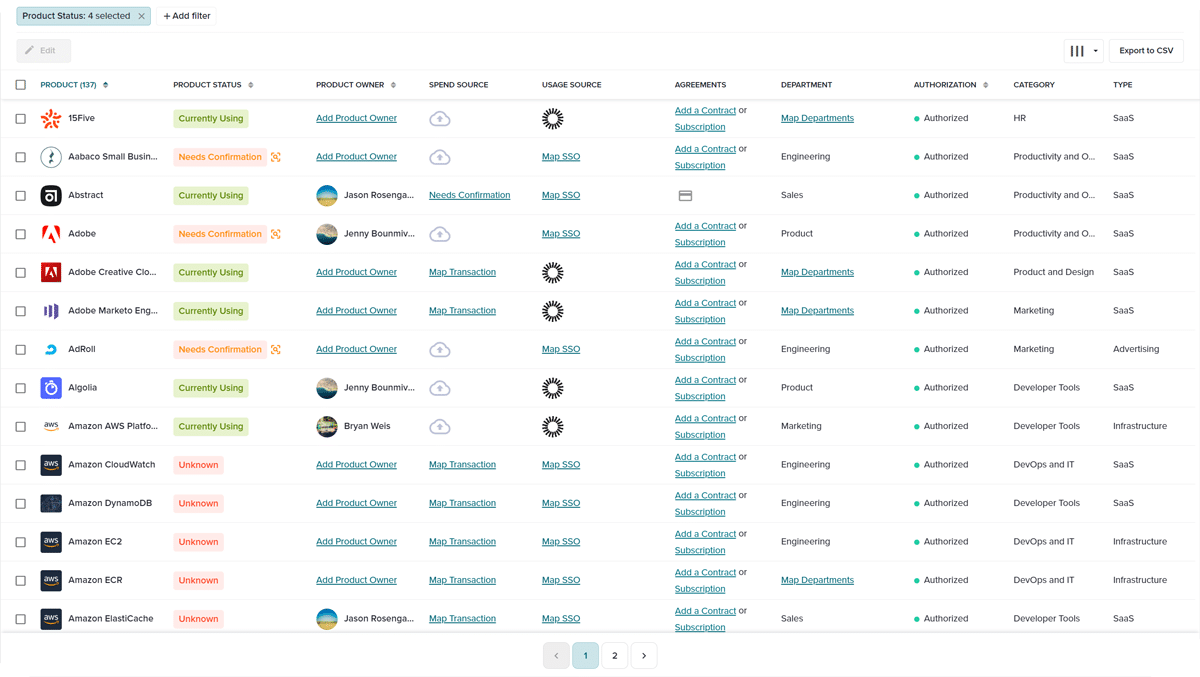
Say goodbye to slow, manual audits and hello to SaaS cost control and budget savings. Automate your SaaS spend and app management using intelligent software that discovers all apps, tracks SaaS spend, manages vendors, stores contracts, and highlights overlapping apps and accounts, as well as unused or underutilized licenses. All to ensure you pay only for what you need.
BetterCloud Spend Optimization by the numbers
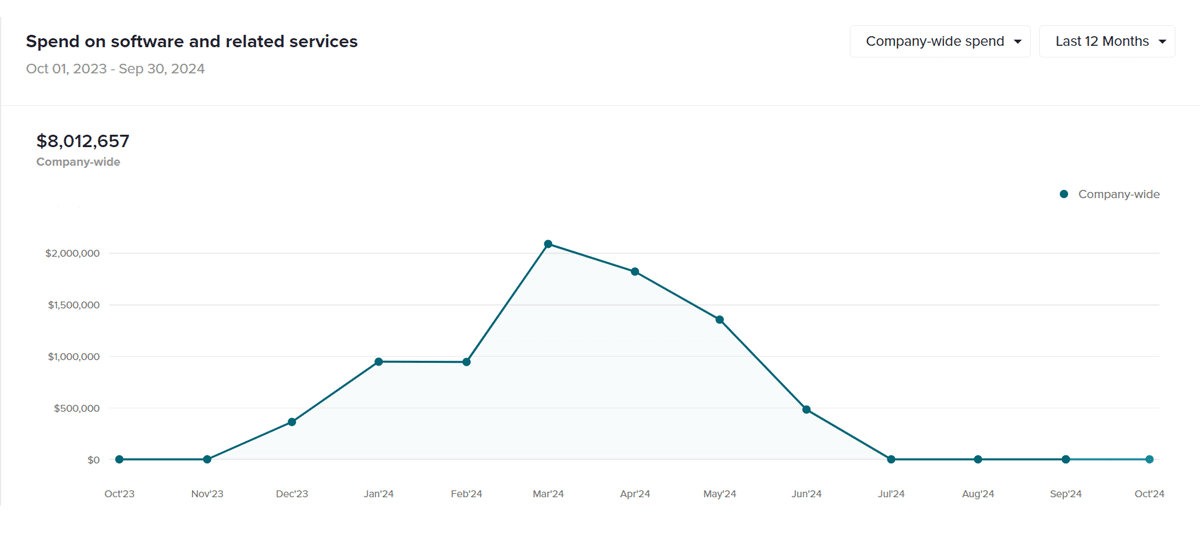
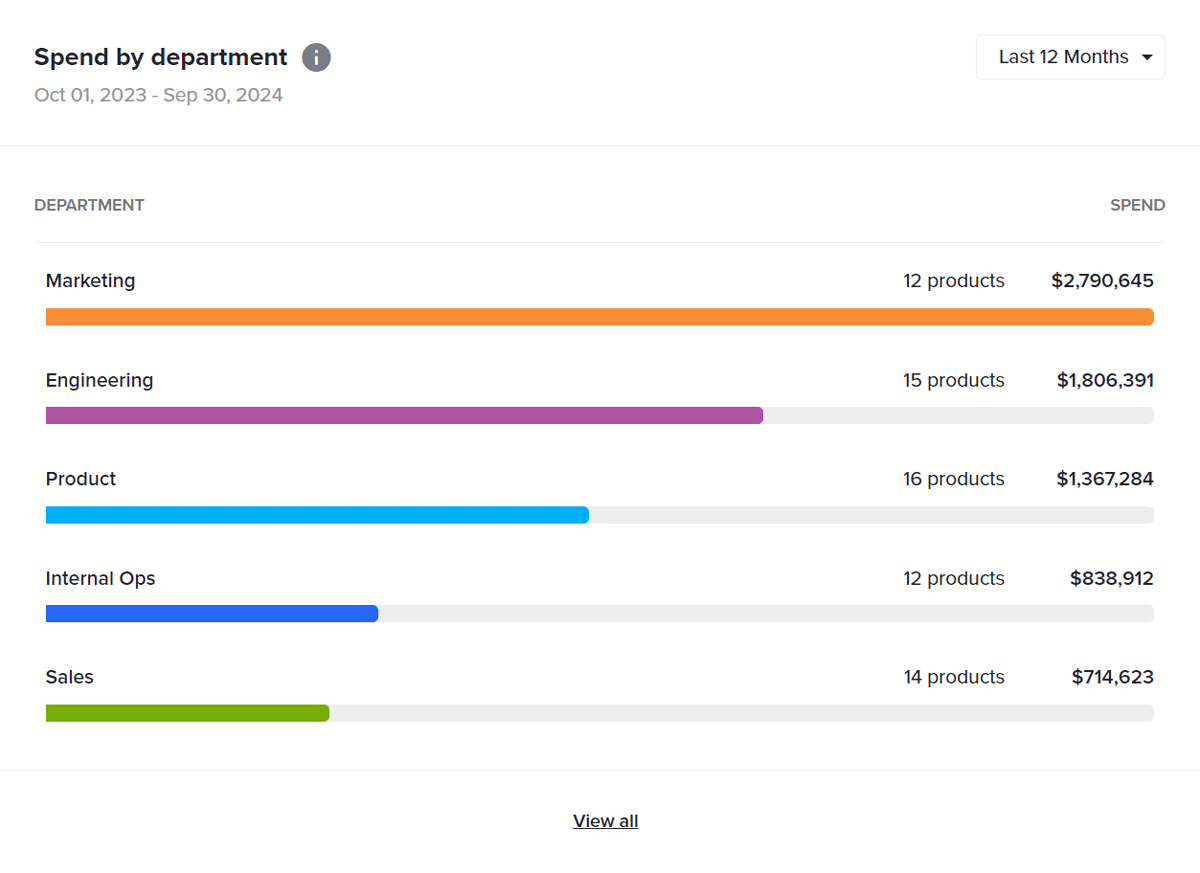
View apps, licenses and spending per employee or department
Through seamless integration into your financial and accounting platforms, discover the software tools used across departments and how much you’re spending on each. Integrations with idP or SSO vendors can show how much they’re used and by who.
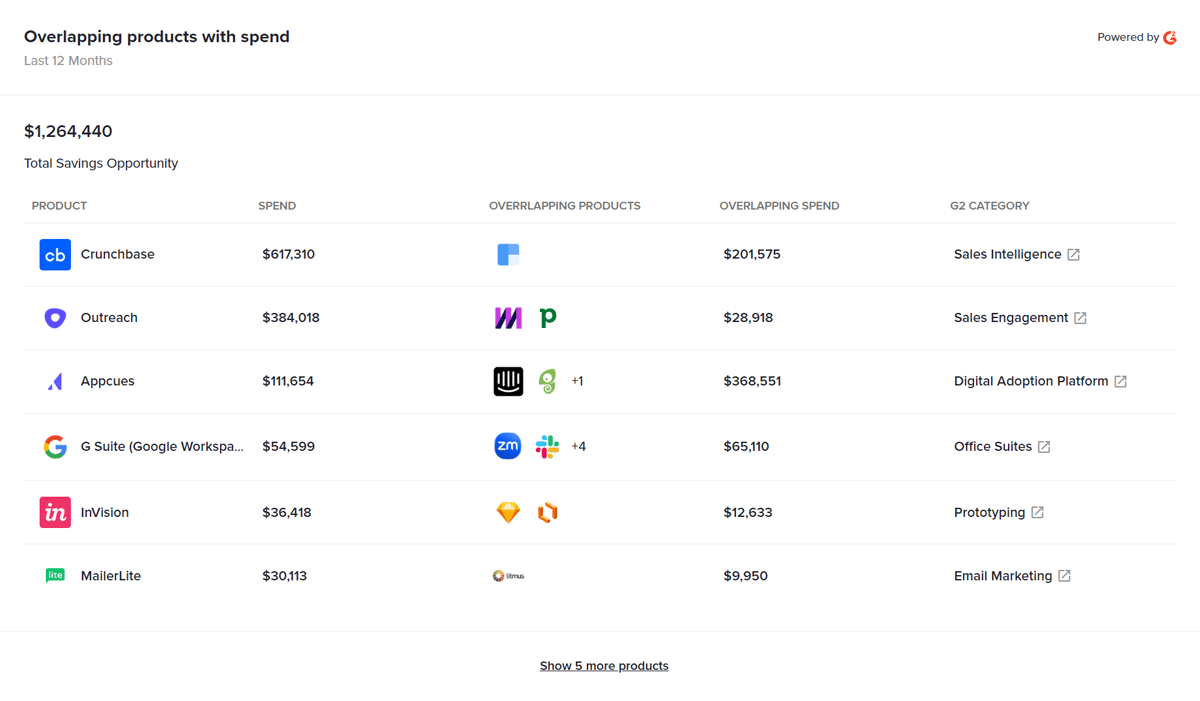
Highlight overlapping SaaS spend instantly
No one wants to pay for multiple software tools that do the same thing. Eliminate duplicate software and accounts to free up spend for new apps.
“
One of the best things I like about this software is its ability to reveal shadow IT and potential savings. With BetterCloud, I can easily track down all the unsanctioned applications and software that my team might be using without my knowledge. This feature alone has helped me keep my organization's technology stack in check, and has also helped me save some money by eliminating unnecessary subscriptions.”
— Miglen E, Verified G2 Review
Intelligent SaaS spend management from BetterCloud
- Detects and accurately categorizes all SaaS apps in real-time – via the world’s largest SaaS taxonomy (G2.com). All commercial SaaS apps are accurately and completely detailed and categorized into a unified dashboard.
- Allocates expenses of company-wide apps across departments, as well as monthly or quarterly.
- 360 degree SaaS visibility inside and outside your SSO with multiple discovery methods
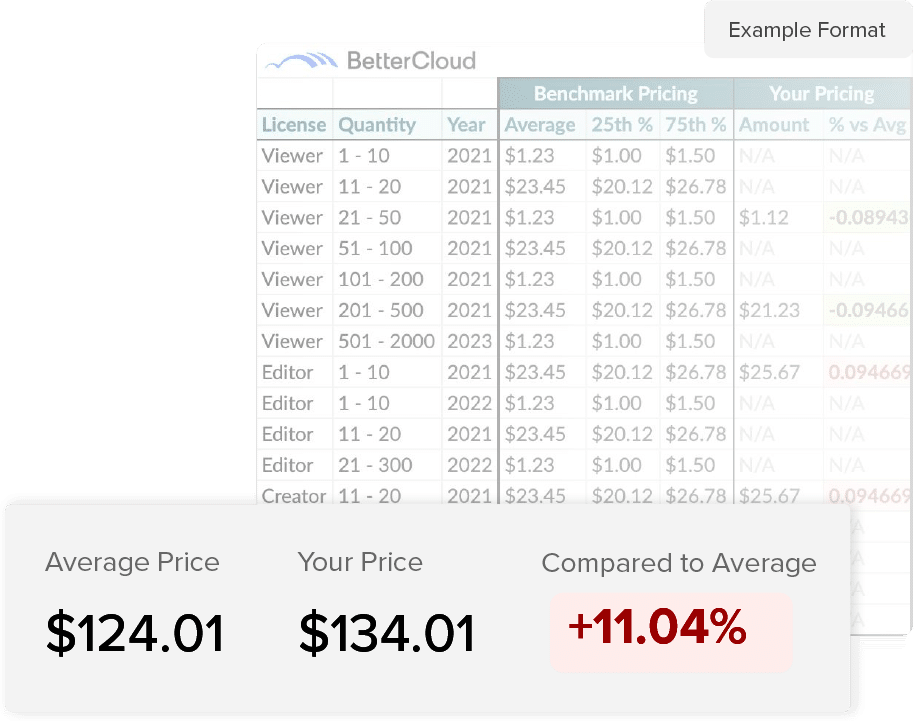
Save big with BetterRenewal
Leverage in-depth pricing data to understand how your software contracts compare to industry benchmarks. Start negotiating your contract renewals with confidence.
SaaS cost control resources
Reign in SaaS costs and optimize your tech stack with BetterCloud. Our CFO shares how we saved big by gaining visibility and control over software spending.
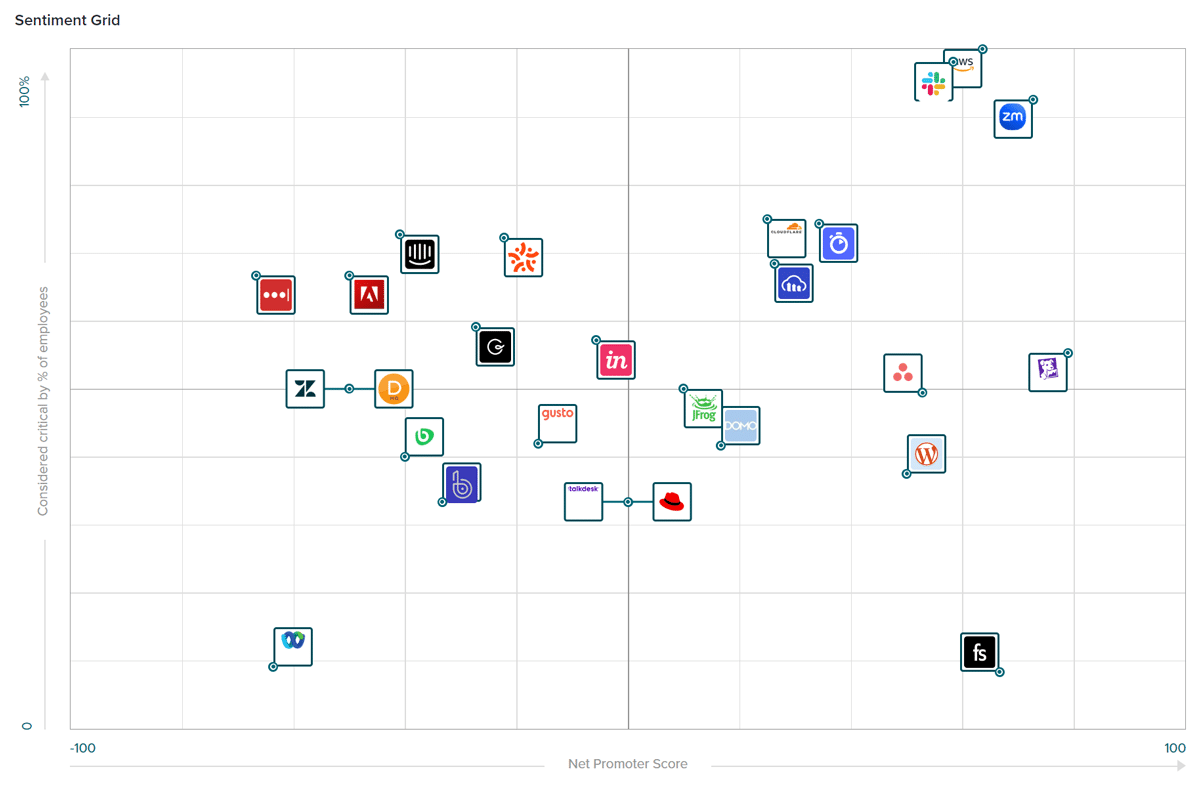
Discover how CFOs are using SaaS spend management software to gain control of software expenses. IT teams and CFOs can work together to eliminate Shadow IT, reduce software overlap, and leverage employee sentiment to make smarter cost-cutting decisions.
Feeling overwhelmed by software subscriptions? Learn how to create a smart SaaS budget and make your tech stack work for you. This guide covers budgeting steps, common mistakes to avoid, and how BetterCloud can simplify the process.
See what else BetterCloud can do for you
IT teams chose BetterCloud: Leader in the G2 Spring 2026 Grid Reports
Recognized as a Leader in 30+ categories in the G2 Spring 2026 Grid Reports, including SaaS Management, SaaS Spend Management, and Data Loss Prevention, BetterCloud helps IT teams reduce manual work, strengthen security, and get more value from every SaaS app.