Prevent Data Leakage and Save Money with BetterCloud’s Apps Explorer
October 22, 2014
2 minute read
Earlier this year we announced the general availability of BetterCloud’s Apps Explorer feature, which allows IT administrators to monitor, whitelist, blacklist and set policies for the use and installation of third-party applications. These applications can be installed by end users from the Chrome Web Store, Google Play, the Apple App Store and most recently via the Google Apps Marketplace – previously restricted to domain super administrators.
While third-party applications undoubtedly enhance the overall Apps experience – a recent Cloud Alliance for Google Apps white paper found a relationship between the use of third-party products and overall satisfaction with the Apps suite – they can in certain cases put your domain’s security at risk. Often times the most heavily integrated applications are the most useful and popular, but the access these applications gain to user information might extend beyond what your company deems reasonable from a data security perspective. Unfortunately, native Google Apps functionality does not provide the means for administrators to enforce granular policies surrounding the use and installation of third-party apps. Enter Apps Explorer.
Set Policies with Apps Explorer
Apps Explorer allows IT professionals to review the applications in use by every employee in the domain, as well as the data access those applications request. Admins can then decide if certain applications should be prohibited for the entire organization, remain accessible for only certain Organizational Units or perhaps give access only to a handful or even just one user. To streamline this evaluation process, IT admins can utilize Apps Explorer’s powerful Apps Policies feature, the only feature of its kind offered to Google Apps customers. Using Apps Policies, admins can enforce acceptable use policies based on the level of data access requested by a third-party application (e.g. read/write Gmail, read/write Drive, etc.), as well as a permission score.
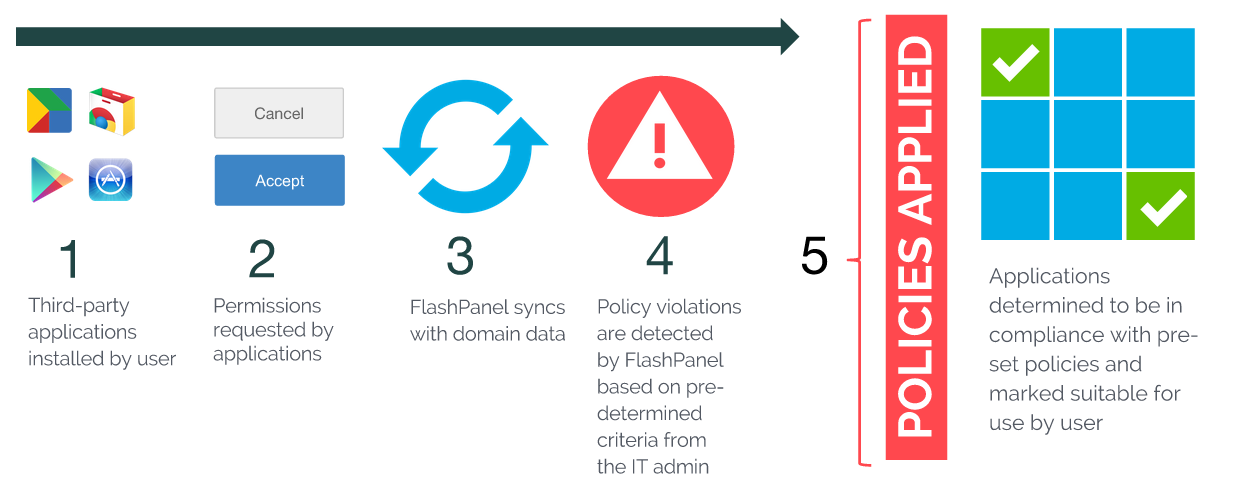
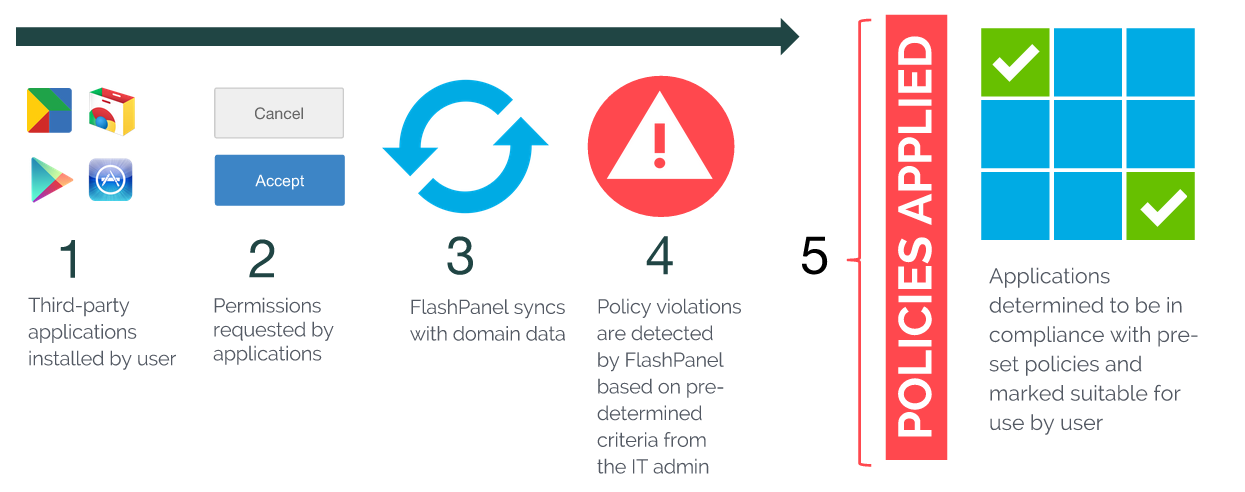
Automatically enforced policies will screen applications installed by end users, which then, according to your policies, will be allowed or denied access. Automating such policies saves you and your IT department valuable time.
Consolidate the Use of Third-party Applications
While a primary focus of Apps Explorer has to do with the protection of sensitive domain data, there’s another powerful benefit. By viewing every application that’s been installed by users, it’s possible to evaluate popular and commonly used applications. In instances where applications are being used by the majority of your company or the members of certain teams, it may make sense to purchase licenses through the IT department thereby consolidating billing and likely earning your organization a per license discount.
Explore the Benefits – Join us for a Webinar
Apps Explorer has myriad benefits beyond even those discussed in this post. To learn more about how your organization can take advantage of Apps Explorer’s powerful auditing and compliance features, be sure to join us for a webinar.
Leveraging Apps Explorer
Tuesday, October 28, 2014
1:00 – 2:00 PM EDT
Register Here