Closing the Gap in SaaS Security
March 27, 2019
5 minute read

You don’t know what you don’t know. This colloquialism is especially true when it comes to SaaS security and management. Because SaaS is still relatively new, and the management of it is mostly uncharted waters, it can be hard for IT managers to know where to begin.
David Politis, our founder and CEO, recently hosted a webinar in collaboration with Daniel Lu, Okta’s product marketing manager, in order to discuss security risks born of SaaS adoption and the Zero Trust model of access management that has emerged from it.
Click here if you want to watch the webinar now, or read below for a quick recap of what you missed.
TL;DR (or watch, apparently)
What are our main takeaways from this webinar?
1. Negligent but well-meaning users pose one of the most difficult insider threat challenges today.
2. Closing the gap in SaaS security requires solving for both first order (connections) and second order (interactions) challenges.
3. If you’re happy with Okta, you will love Okta + BetterCloud (using both in combination is the key to effectively closing the gap).
Before we dive in, what is Zero Trust?
Zero Trust is a popular concept and something more and more IT and security professionals are thinking about. The old approach relied on a trusted network that had a trusted perimeter—everyone inside was good and everyone outside was bad. However, this is no longer the case. We’ve been poking holes in the perimeter for years to give access to contractors, interns, partners, etc.
So how do you secure your network and know that it hasn’t been compromised?
This is where Zero Trust comes in. Policy enforcement must be done at the point of access. People are the new perimeter, and when people are the new perimeter, identity becomes a foundation of the Zero Trust strategy.
Modern access management is about making sure that the right people have the correct level of access only when they need it—and that access is managed on a continual basis, all while providing a frictionless experience for the end user.
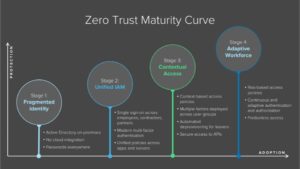
Okta has created a handy Zero Trust maturity curve:
Evolving challenges
The challenges around securing your environment are rapidly evolving. In the early 2000s, it was about securing devices. Then, as the rise of SaaS apps and the cloud came around, the challenges became about securing the identity, access, and user in the perimeter-less environment. Cue Okta, who came in to solve this identity problem.
To quote our guest Daniel Lu, “Moving beyond authentication, what happens when the user gets access to that specific application? What kind of interactions are they having within that app or those resources? Secure connection is the first step. Secure interactions are equally important.” Daniel’s right of course; the newest challenges are activity and entitlement inside your SaaS applications.
Securing your interactions are an important part of mitigating your insider threats. In fact, 91% of IT and security teams feel vulnerable to insider threats according to our new insider threats report.
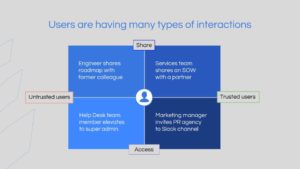
User interactions: Who are they interacting with, and how much should you trust them?
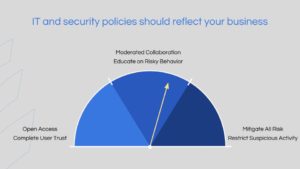
Your IT and security policies should reflect your business needs. Not every business requires or wants the same level of access/restrictions for its users.
Day in and day out, your users are interacting with countless other users, both trusted and untrusted, internally and externally.
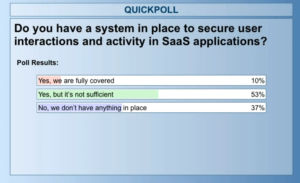
POLL: How secure are your user interactions in SaaS applications?
Ninety percent of poll respondents either don’t have a system in place to secure user interactions and activity in SaaS applications, or they don’t feel that their current system is sufficient. This is a fairly normal distribution because the need to secure SaaS applications is a new problem. Many people don’t feel the need to act until there is a security breach.
IT and security policies need to reflect your business philosophy. The left-hand side of the spectrum represents companies that believe their employees can be trusted with all data and do not need to be monitored. The other end of the spectrum represents people who want to “lock it all down” and enforce their IT and security policies with brute force. Most companies land in the middle of the spectrum. This represents a more moderate stance that includes flexible remediation steps and end user education.
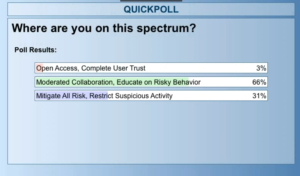
POLL: Where do you land on the spectrum?
More than half of respondents report that their company falls in the middle of this spectrum. Increasingly, companies are adopting SaaS applications and collaboration tools. While they want to encourage collaboration, it is important that companies find the right fit for enforcing their IT and security policies, giving their employees enough access while still protecting their data.
BetterCloud X Okta
There are 400 customers that use both Okta and BetterCloud.
Why? In short, because it just makes sense—they complement each other and help you take control of your SaaS environment.
Below are three common use cases for using BetterCloud in conjunction with Okta.

BetterCloud will listen to lifecycle changes made in Okta, and BetterCloud will trigger workflows in order to complete the offboarding process across SaaS apps.

BetterCloud listens to Okta and other connected SaaS applications, ingests activities, then creates policies in BetterCloud to remediate any policy violations.

BetterCloud also acts as a policy remediation engine. Users can connect security insights to BetterCloud, which automates policy enforcement across SaaS applications.
To learn more about how BetterCloud can complement Okta and secure user interactions, request a demo.