3 Real Phishing Attacks Your C-Suite Needs to See
August 11, 2016
4 minute read
Phishing is a term that brings dread to every executive–or at least it should.
In 2015, CEOs lost $2.3 billion from phishing scams, according to the FBI, and the “biggest government hack ever” was reportedly a malware attack likely delivered via a phishing email.
Below you’ll find three real examples of phishing attempts and how to identify them.
The Imposter: Spoofing
The phishing attempt below was unknowingly sent from a customer of ours in a common practice called spoofing.
You can learn more about how to prevent spoofing here.
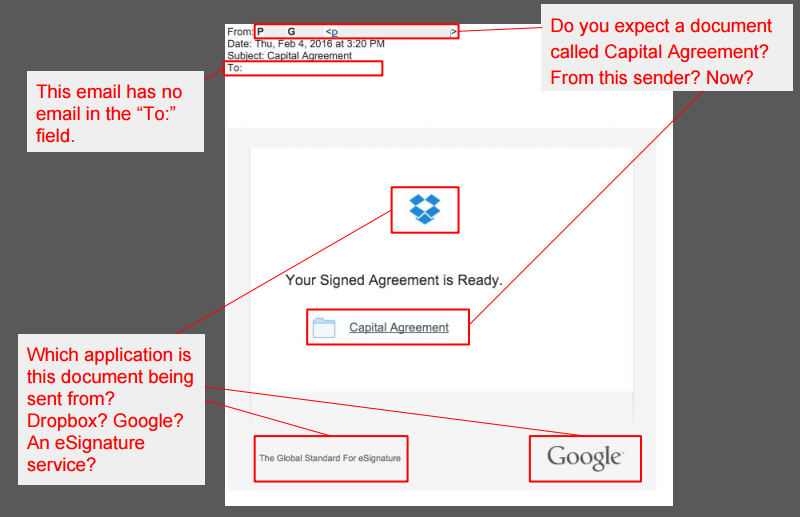
Always hover over links to see their true destination. In this case, hovering over the “Capital Agreement” link points to a suspicious URL. You can see this URL at the bottom of your browser window.
If you click on this link by accident, you may be directed to a “Google Docs” sign in page seeking to steal your email and password.
The image on the left is a real phishing attempt; on the right is Google’s real sign in page.
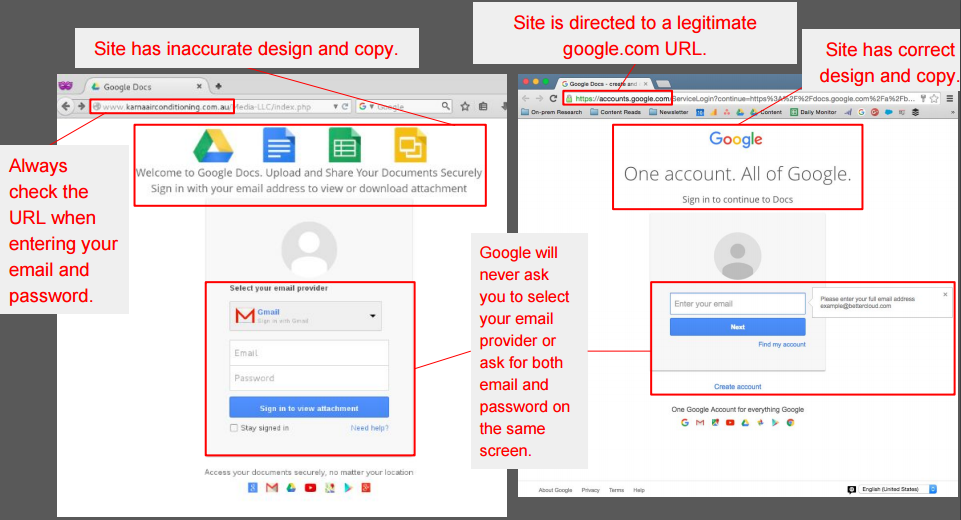
Never provide your Google account credentials if the domain is not clearly google.com. Also, this connection is not over a secure HTTPS (TLS/SSL) link–there is no secure padlock indicator in the address bar.
Hackers may use similar URLs with misspellings (i.e. qoogle.com) on these phishing pages and even take the time to implement HTTPS. Keep in mind that there are many other applications that require your email and password, so Google is not the only site that can be replicated.
The Sharp Shooter: Spear Phishing
Spear phishing is when attacks get more concerning. With spear phishing attacks, hackers are actively seeking out a single individual. For executives, this type of attack is called “whaling” and can be extremely effective (from a hacker’s point of view).
Spear phishing attempts may be short and hope to spark a conversation between an executive and your CFO. The image below features two real examples:
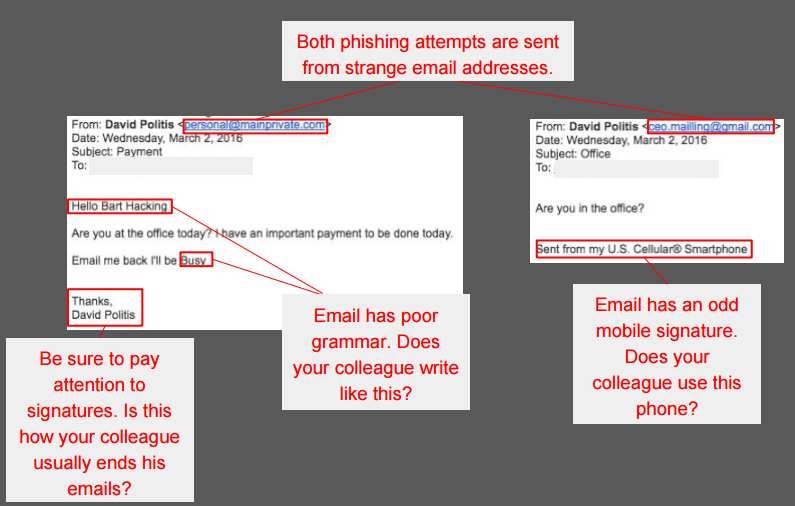
Always expand the “From:” field as many hackers will seek to hide a shady email address.
You also want to be exceptionally careful when you check email on your smartphone; it takes extra work on your part to identify the true sender (as well as the true destination of a link).
Note: Always keep spoofing in mind as phishing attacks can come from legitimate email addresses.
When receiving an email from another executive, always ask yourself: Does this sound like my colleague? And am I expecting this email? If not, pick up the phone and call them. Never make any significant payment without a phone call or a face-to-face conversation.
You should always have verification of more than one authorized person when dealing with wire transfers over a certain threshold.
The Scorch the Earther: Generic Phishing
These are the easiest phishing emails to catch. They’re sloppy and usually offer zero context. He or she was lazy. There are some obvious warning signs.
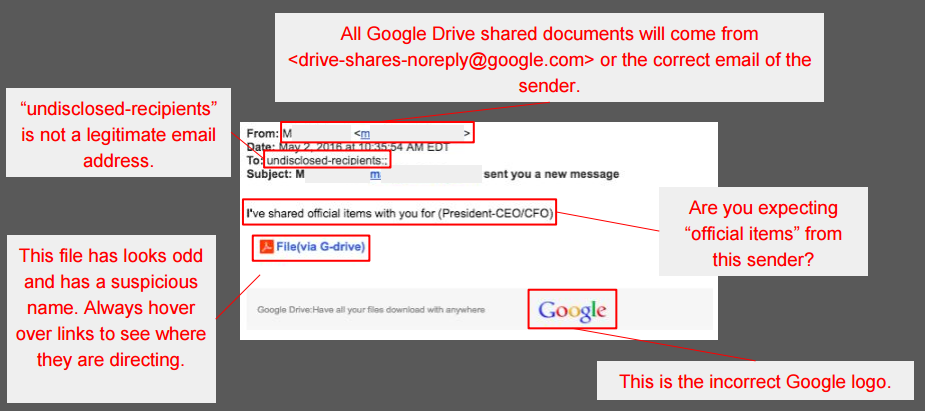
This document directed to a suspicious URL (another clue this email was malicious).
Again, ask yourself: Am I expecting this document? Probably not.
Stay Vigilant: Tips to Protect Yourself
- Be careful before clicking on an email or any content in it, including links and attachments. Think before you click! Take note of any irregularities in the sender, recipient list, subject line, message, etc. Inspect the destination of a hyperlink (hover over the link with your mouse pointer or long-press on a mobile device).
- Invitations to view shared documents are a common attack vector right now, so beware of any such emails.
- For Google Docs, legitimate sharing messages will come from either drive-shares-noreply@google.com or the email of the person sharing the document.
- Never enter your Google account credentials on anything other than the actual Google login page. Look closely at the URL bar.
- Click the Report Phishing (when available) or Report Spam options in Gmail to alert Google of the mail so they can block it for other targeted users.
- Don’t reuse your Google account password on other sites. 2-Step Verification on your Google accounts makes it harder for an attacker to access your account but doesn’t prevent them from using that password to access other accounts where you have used the password.
To help your employees identify phishing, check out our tips for Google Apps and Office 365 users. To learn more about protecting your entire Google Apps domain, check out BetterCloud.