Manage every app, every user, every dollar
Finally, a complete and insights fueled platform for end-to-end SaaS management for IT. Track your applications and expenses, automate user permissions and access, and secure your cloud files.
Why BetterCloud?
Thousands of companies have run millions of workflows using BetterCloud
With the ability to streamline and automate critical work like SaaS access and day-to-day operations, learn why BetterCloud's customers enjoy greater operational efficiency and employee productivity.
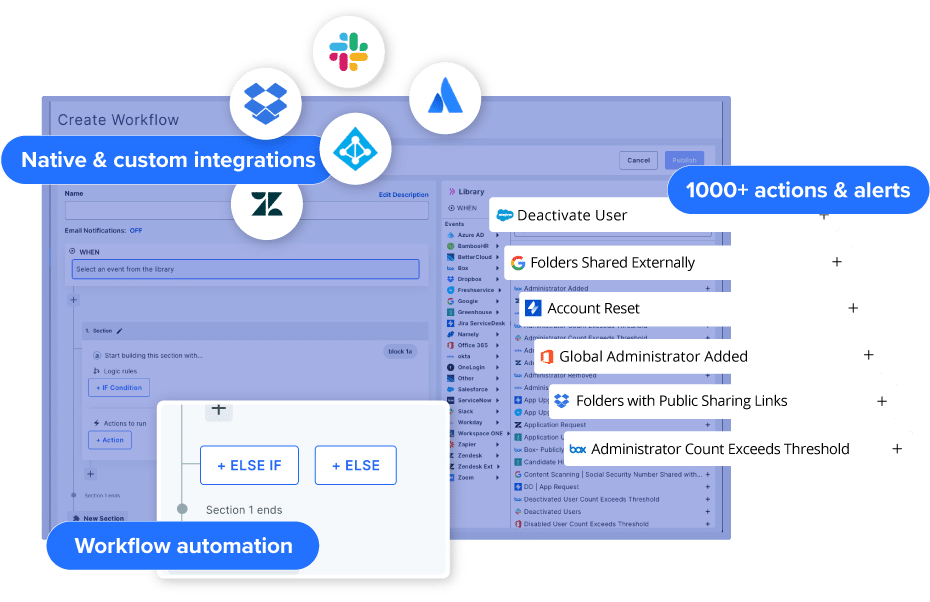
Set up new workflows and automations in minutes
We built BetterCloud with every IT employee in mind. Our SaaS management platform is quick to implement and easy to use. The work of IT is important and the company depends on you; a SaaS Management Platform should enable that work, not add to it.
- Configure automations with a no-code drag and drop workflow builder
- Automate employee onboarding and offboarding with dynamic workflow decisioning and workflow scheduling
- Access a library of hundreds of workflow actions, triggers, and templates

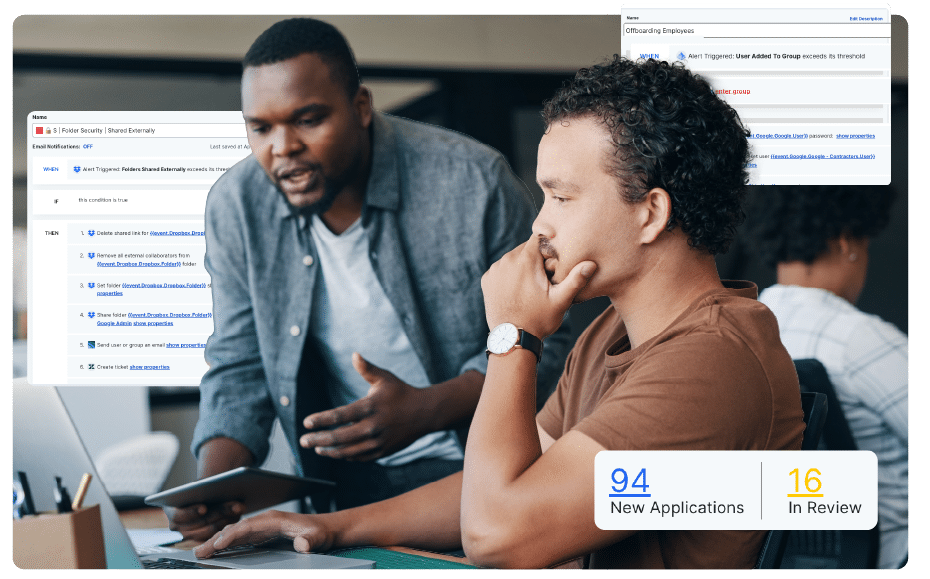
A better help desk console for IT
Give your Help Desk the tools to resolve more tickets, faster - and automate the rest.
- Centralize the management of user permissions and access for each SaaS application
- Change admin access in bulk or automatically
- Automate responses and resolution to common help desk tickets
Manage expenses and reclaim licenses
Simplify renewals, manage licenses, and eliminate shadow IT.
- Manage software licenses and contract renewals with industry benchmarks
- Prevent overlap in subscriptions and drive spending efficiency
- Identify underutilized resources and cut your expenses

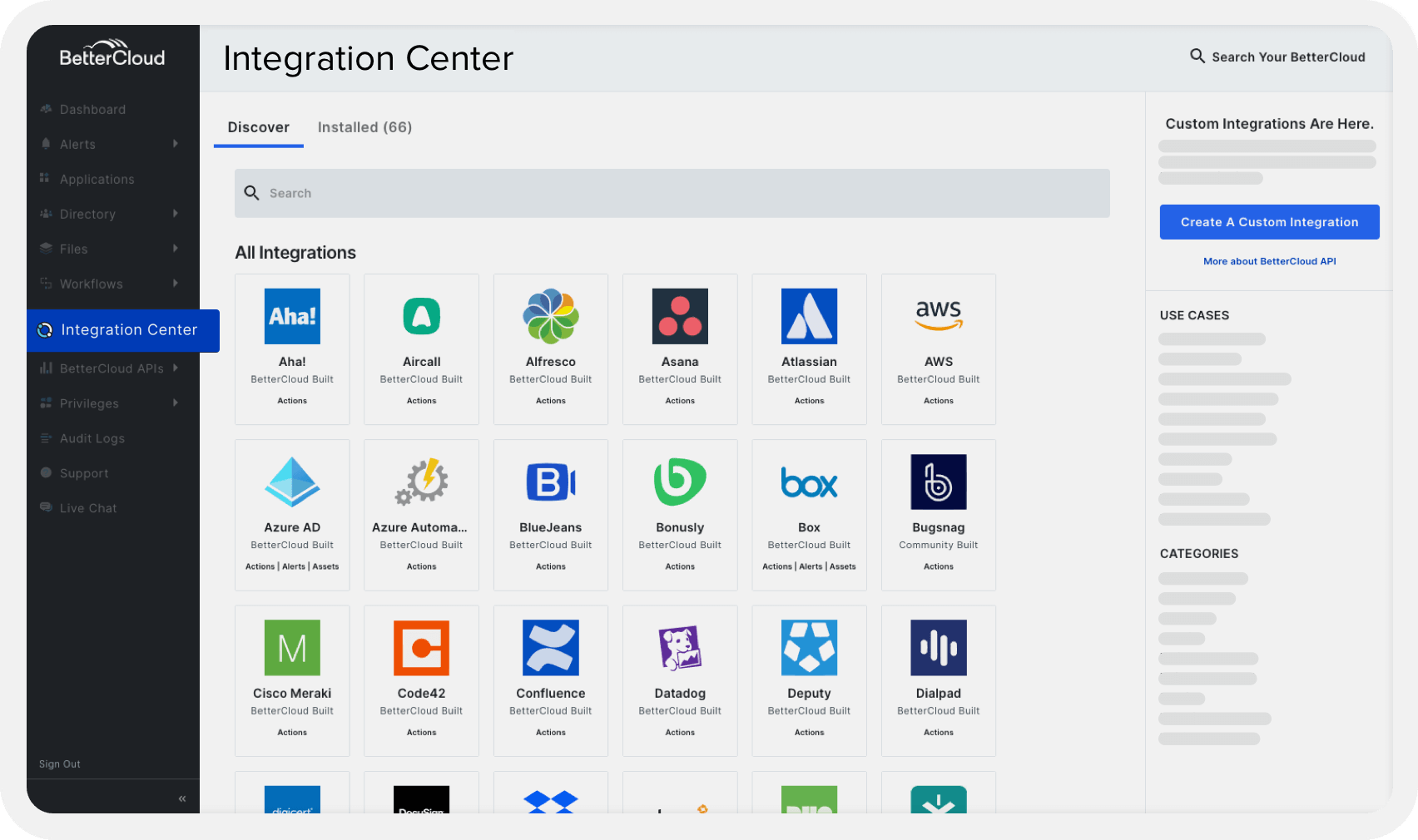
70+ integrations and 1000+ actions provided out-of-the-box
Get control over your apps, data, and users roles to ensure that all your compliance and security standards are being met.
- Build custom integrations to start automating more tasks for your IT team
- Configure workflows with thousands of actions and alerts across dozens of apps
- Access the continuous updates and extensions BetterCloud adds to existing integrations
See what else BetterCloud can do for you
How quickly is SaaS adoption still growing, and what are the most urgent challenges facing IT today? Why does SaaS security continue to keep IT up at night? Which SaaSOps processes are organizations automating the most, and how critical is automation? (Spoiler alert: Very.) We’ll cover all of this—and more.
Driving business outcomes with BetterCloud
See how thousands of IT teams are using our SMP solution to increase efficiency, enhance visibility and reduce security risk within your SaaS environment.
With a strong commitment to automation, FIRST learned how to harness the full potential of Bettercloud and within a few weeks build out the necessary workflows to address recurring pain points within the business.
When Elliot Grossman started at BARK as the Director of IT, he was the only member of the IT team. Being the sole person responsible for all IT tasks, like onboarding, offboarding, and mid-lifecycle changes, was very time consuming.
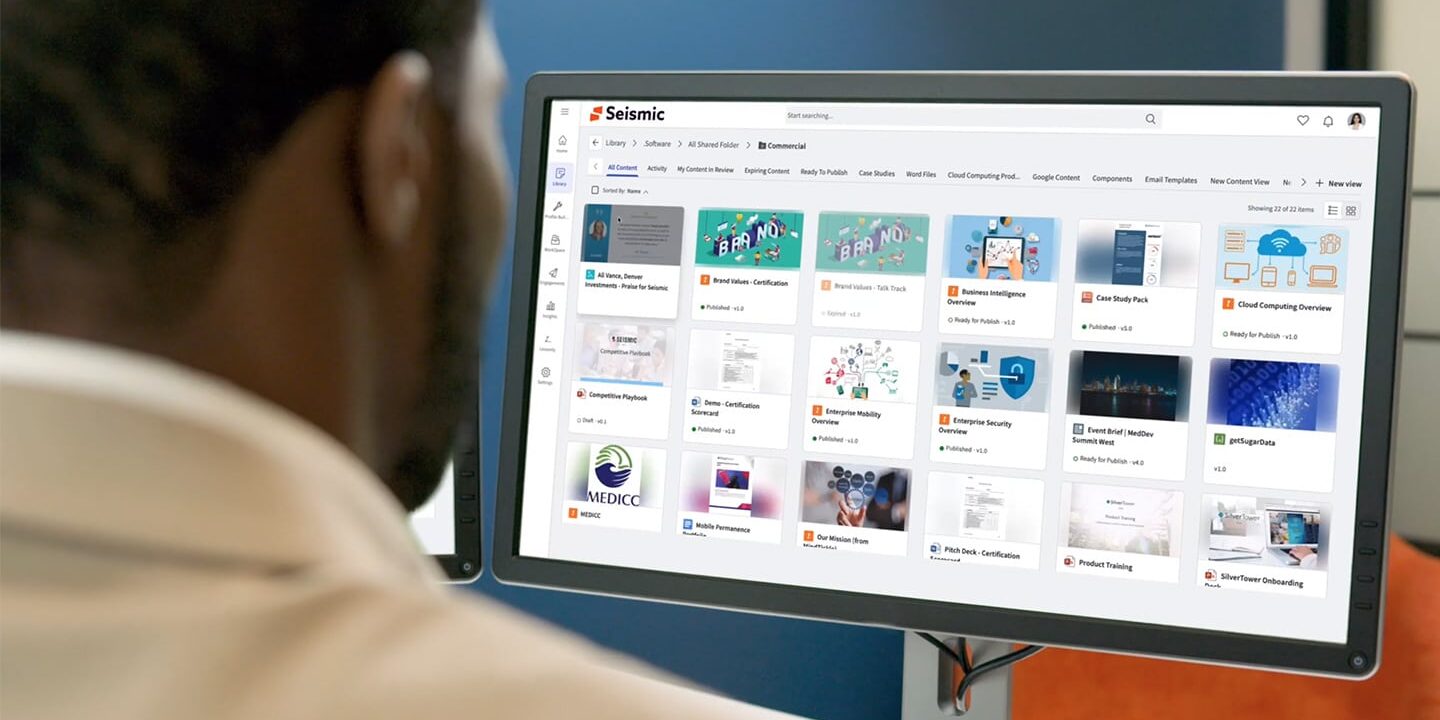
When Steve Foley, Senior IT Automation Engineer at Seismic, joined the company, the IT function was a team of eight. The small but mighty IT team completed the myriad of tasks they were responsible for manually.
Trusted by IT: BetterCloud is the highest rated and most complete SaaS Management Platform on G2
G2 rated BetterCloud a Leader in 30+ of its Spring 2024 grid reports, including SaaS Operations Management, Data Loss Prevention (DLP), Data Security, User Provisioning and Governance (UPG), and Cloud File Security, among others.
Latest from BetterCloud
The IT leader’s mega-guide to SaaS savings
Stop SaaS sprawl from draining your budget! BetterCloud’s guide reveals how to control hidden SaaS costs, optimize your tech stack, and maximize ROI. Download now & conquer SaaS bloat!
Mastering helpdesk support: The right way to submit an IT ticket
Struggling with tech problems at work? Don’t waste time with confusing helpdesk tickets! This guide teaches you how to write clear, concise requests that get your issues resolved faster.
The AI tax: What IT pros need to know
Discover how the AI tax is quietly inflating your software bills and learn how to combat it with a robust SaaS management platform (SMP). Stay ahead of unexpected costs and take control of your organization’s software expenses.